Check if your information is on the dark web for data breaches, phishing attacks, and identity theft as these issues continue to rise. Stolen passwords, email addresses, banking details, and personal information are constantly being bought and sold across hidden cybercriminal marketplaces. In this guide, you will learn how to check if your information is on the dark web, recognize warning signs of data exposure, protect your accounts after a breach, and use the best identity theft protection tools to reduce your risk of fraud and online attacks.
Table of Contents
What Does It Mean If Your Information Is on the Dark Web?
When you check if your information is on the dark web, you are looking for stolen personal data that may have been exposed through data breaches, hacked accounts, malware infections, phishing attacks, or leaked databases. The dark web is a hidden part of the internet where cybercriminals often buy, sell, and trade stolen information such as email addresses, passwords, Social Security numbers, banking details, and phone numbers.
If your information appears on the dark web, it does not always mean your identity has already been stolen. However, it significantly increases the risk of identity theft, account takeovers, financial fraud, phishing scams, and unauthorized access to your online accounts.
Hackers commonly collect personal data from:
- Large company data breaches
- Weak or reused passwords
- Fake login pages and phishing emails
- Public WiFi attacks
- Using unsafe public WiFi can expose your passwords, banking details, and personal accounts to attackers. Click here to learn more about Public WiFi Dangers
- Malware and spyware infections
- Data broker databases
Want to understand how cybercriminals actually steal personal information in the first place? Read our complete guide on How Hackers Get Your Personal Data.
Once exposed, this information can spread quickly across cybercriminal forums and underground marketplaces. This is why many people now use dark web monitoring services and identity theft protection tools to detect leaks early before serious damage occurs.
Cybercriminals often target:
- Email accounts
- Online banking accounts
- Credit card information
- Social media profiles
- Healthcare records
- Password vaults
- Cryptocurrency wallets
Checking if your information is on the dark web can help you act quickly by changing compromised passwords, enabling multi-factor authentication, freezing your credit, and monitoring suspicious activity.
Many identity protection services now include:
- Real-time dark web monitoring
- Data breach alerts
- Identity theft insurance
- Credit monitoring
- Fraud resolution support
👉 Protect your identity and monitor the dark web for leaked personal information with Aura here.
These tools continuously scan leaked databases and underground marketplaces to help detect exposed personal information faster than manual monitoring alone.
According to the Cybersecurity and Infrastructure Security Agency (CISA), stolen credentials remain one of the most common ways attackers gain unauthorized access to personal and financial accounts.

How Personal Information Ends Up on the Dark Web
Many people check if their information is on the dark web after hearing about a major data breach or suspicious account activity. However, most personal information leaks happen long before victims realize their data was stolen. Cybercriminals constantly search for weak security, exposed databases, and vulnerable online accounts to collect valuable personal information.
One of the most common causes of dark web exposure is large-scale company data breaches. When businesses get hacked, attackers may steal millions of customer records containing:
- Email addresses
- Passwords
- Phone numbers
- Home addresses
- Credit card information
- Social Security numbers
These stolen databases are often sold or shared on underground dark web marketplaces where cybercriminals buy data for fraud, phishing attacks, account takeovers, and identity theft.
Another major risk comes from password reuse. If you use the same password across multiple websites, hackers can use stolen credentials from one breach to access your other accounts. This is known as “credential stuffing,” and it remains one of the most effective cyberattack methods today.
Phishing scams also play a huge role in exposing personal information online. Attackers create fake emails, login pages, and text messages designed to trick users into entering passwords, banking details, or verification codes. Once stolen, this information may quickly appear on dark web forums.
Public WiFi networks can also expose your personal data if the connection is unsecured. Hackers sometimes intercept internet traffic on unsafe networks to steal login credentials and sensitive information. This is one reason many cybersecurity experts recommend using VPN services on public networks.
👉 Protect your internet activity and personal information on public WiFi with NordVPN here.
Malware infections are another common source of stolen information. Certain types of malware can:
- Record keystrokes
- Capture passwords
- Steal browser cookies
- Access saved payment information
- Collect personal files
Some advanced malware specifically targets cryptocurrency wallets, online banking sessions, and password managers.
Data brokers also contribute indirectly to online exposure risks. These companies collect massive amounts of personal information from public records, apps, websites, and online activity. The more information available online, the easier it becomes for scammers and cybercriminals to build detailed identity profiles for phishing and fraud attacks.
Many people do not realize how much personal information data brokers collect and sell online. Learn how these companies work here: What Is a Data Broker
If you want to check if your information is on the dark web, monitoring tools can help identify leaked credentials before criminals fully exploit them. Many identity theft protection services now scan dark web databases for exposed emails, passwords, phone numbers, and Social Security numbers in real time.
Taking action early can help reduce the risk of:
- Identity theft
- Financial fraud
- Account takeovers
- Unauthorized purchases
- Scam calls and phishing attacks
What Types of Personal Information Get Leaked Online?
When people check if their information is on the dark web, they are often surprised by how much personal data may already be exposed online. Cybercriminals target many different types of information because stolen data can be used for identity theft, financial fraud, phishing attacks, account takeovers, and scams.
Some leaked information may seem harmless on its own, but hackers often combine multiple pieces of personal data to build detailed identity profiles. This is why even small data leaks can become dangerous over time.
The most commonly exposed types of personal information include:
- Email addresses
- Passwords
- Phone numbers
- Home addresses
- Social Security numbers
- Credit card information
- Banking details
- Driver’s license numbers
- Medical records
- Login credentials
- Social media account information
Email addresses are among the most frequently leaked pieces of data online. Once hackers obtain your email address, they may target you with phishing emails, password reset attacks, malware, or spam campaigns. If the leaked email is connected to reused passwords, the risk becomes even greater.
Stolen passwords are especially valuable on the dark web. Attackers often buy massive password databases and use automated tools to attempt logins across multiple websites. This is why cybersecurity experts strongly recommend using unique passwords and password managers for every online account.
Phone numbers are also commonly exposed in data breaches and data broker databases. Criminals may use leaked phone numbers for:
- Scam calls
- Smishing text attacks
- SIM swap fraud
- Two-factor authentication attacks
Financial information such as credit card numbers and banking details can lead directly to unauthorized purchases and fraud. In some cases, criminals sell complete “fullz” identity packages on the dark web that contain:
- Full names
- Addresses
- Social Security numbers
- Date of birth
- Banking information
These complete identity profiles are highly valuable because they allow criminals to open accounts, apply for loans, or commit identity theft more easily.
Medical records are another growing target for cybercriminals. Healthcare data breaches may expose insurance information, prescriptions, medical histories, and sensitive personal details that can be used for fraud or blackmail.
Social media accounts are also frequently targeted. Attackers may hijack profiles to spread scams, impersonate victims, or gather additional personal information from public posts and friend lists.
According to the IdentityTheft.gov, stolen personal information can be used to commit tax fraud, credit fraud, employment fraud, and many other forms of identity theft.
If you want to check if your information is on the dark web, it is important to monitor more than just your email address. Comprehensive identity monitoring services can scan for:
- Exposed passwords
- Breached phone numbers
- Social Security numbers
- Financial account leaks
- Dark web marketplace activity
Early detection can help reduce long-term damage and improve your chances of stopping fraud before it becomes severe.
Signs Your Information May Already Be Exposed
Many people do not realize their personal information has been leaked until serious problems begin to appear. This is why it is important to check if your information is on the dark web before identity theft or financial fraud gets worse. In many cases, cybercriminals may already have access to your data weeks or even months before obvious warning signs appear.
One of the most common signs of exposed information is receiving unexpected password reset emails. If you start getting password reset requests for accounts you did not initiate, attackers may already be attempting to access your accounts using leaked credentials from a data breach.
Another major warning sign is unfamiliar login activity. Many online services now send security alerts when someone signs in from a new location or device. If you notice unknown login attempts, your email address or password may already be circulating online.
You should also watch for:
- Unauthorized bank transactions
- Credit card charges you do not recognize
- New accounts opened in your name
- Missing mail or bills
- Sudden drops in your credit score
- Locked online accounts
- Increased spam emails or scam calls
- Fake social media accounts impersonating you
Spam calls and phishing emails often increase after personal information appears in breached databases or data broker records. Criminals use exposed information to create highly targeted scams that appear more convincing and legitimate.
Want to see the biggest ways personal information spreads across the internet today? Read our full breakdown on How Your Personal Data Ends Up Online.
If your phone suddenly receives nonstop robocalls, fake delivery texts, or suspicious verification codes, your number may already be exposed online. SIM swap attackers sometimes use leaked personal data to hijack phone numbers and bypass two-factor authentication security.
Compromised email accounts are especially dangerous because email access often allows attackers to reset passwords for banking, shopping, and social media accounts. This is why checking for exposed email addresses and password leaks is so important.
Another major red flag is discovering your information inside public people-search websites or data broker platforms. These databases may contain:
- Full names
- Addresses
- Phone numbers
- Relatives
- Employment history
- Age and birth information
The more public information available online, the easier it becomes for scammers and identity thieves to target you.
If you want to check if your information is on the dark web, identity monitoring tools can help detect:
- Exposed passwords
- Breached email accounts
- Leaked Social Security numbers
- Dark web marketplace listings
- Fraud-related activity tied to your identity
The earlier you discover leaked information, the faster you can secure your accounts, freeze your credit, update passwords, and reduce long-term damage.
How to Check If Your Information Is on the Dark Web
If you want to check if your information is on the dark web, the good news is that you do not need advanced technical skills to get started. Several trusted tools and identity monitoring services can scan known breach databases and dark web marketplaces for exposed personal information.
The most common way to check for leaked data is by searching your email address in breach databases. Many cyberattacks expose millions of login credentials at once, and these stolen records often circulate across underground forums and dark web marketplaces.
If your email appears in breach results, attackers may already have access to:
- Passwords
- Login credentials
- Phone numbers
- Account information
- Security questions
You should also check whether your passwords have been compromised. Some password managers and security tools now include built-in breach monitoring that alerts you when saved credentials appear in leaked databases.
Another effective option is using identity theft protection services with dark web monitoring features. These services continuously scan underground marketplaces and breach collections for:
- Email addresses
- Passwords
- Social Security numbers
- Banking information
- Phone numbers
- Driver’s license information
Unlike free tools that require manual searches, identity monitoring services provide ongoing real-time alerts when new leaks are detected.
You can also:
- Review your bank and credit card statements regularly
- Monitor your credit reports
- Watch for unfamiliar login alerts
- Enable multi-factor authentication on important accounts
- Check public people-search websites for exposed personal information
According to the Federal Bureau of Investigation (FBI) Internet Crime Complaint Center, cybercriminals frequently use stolen credentials from old data breaches to target new victims through phishing attacks, financial fraud, and account takeovers.
If you discover your information has been exposed, you should immediately:
- Change compromised passwords
- Use unique passwords for every account
- Enable multi-factor authentication
- Freeze your credit if necessary
- Monitor financial accounts for suspicious activity
- Remove unnecessary personal information from public websites
Many cybersecurity experts also recommend using:
- Password managers
- VPN services
- Identity theft monitoring
- Data removal services
These tools help reduce future exposure risks and make it harder for attackers to collect your information online.
Checking if your information is on the dark web regularly is becoming increasingly important because data breaches happen constantly. Even trusted companies can experience cyberattacks that expose customer information without warning.
The sooner you identify leaked data, the better your chances of preventing identity theft, financial fraud, and long-term account compromise.
How to Check If Your Email Address Was Leaked
One of the most important steps when you check if your information is on the dark web is finding out whether your email address has been exposed in a data breach. Email accounts are often the primary target for cybercriminals because they can be used to reset passwords, access financial accounts, and steal sensitive personal information.
If your email address was leaked online, attackers may attempt:
- Phishing attacks
- Credential stuffing attacks
- Account takeovers
- Scam emails
- Malware delivery
- Password reset abuse
The easiest way to check if your email address was leaked is by using trusted breach-checking tools that scan known databases of stolen credentials.
One of the most widely used resources is Mozilla Monitor. This free tool allows you to search your email address and see whether it has appeared in publicly known data breaches. It can also show:
- Which companies experienced the breach
- What types of data were exposed
- When the breach occurred
- Whether passwords were compromised
If your email appears in breach results, it does not automatically mean hackers currently control your accounts. However, it does mean your information may already be circulating online among cybercriminals.
You should also pay attention to warning signs such as:
- Sudden increases in spam emails
- Security alerts from online accounts
- Password reset emails you did not request
- Login attempts from unknown devices
- Locked accounts due to suspicious activity
If your email address has been exposed, changing passwords immediately is critical — especially if you reused the same password across multiple websites.
Cybersecurity experts strongly recommend:
- Using unique passwords for every account
- Enabling multi-factor authentication
- Using password managers
- Monitoring accounts regularly for suspicious activity
👉 Secure your accounts with strong encrypted passwords using NordPass here.
This type of monitoring can help you:
- Detect breaches faster
- Secure compromised accounts early
- Reduce identity theft risks
- Prevent financial fraud
- Stop attackers before major damage occurs
Checking your email exposure regularly is important because new breaches happen constantly. Even accounts from trusted companies can become vulnerable after cyberattacks or database leaks.
The earlier you discover an exposed email address, the faster you can secure your online accounts and reduce long-term risks.
How to Check If Your Passwords Were Stolen
If you want to check if your information is on the dark web, one of the most important things to monitor is your passwords. Stolen passwords are extremely valuable to cybercriminals because they can be used to access email accounts, banking platforms, shopping websites, social media accounts, and even password managers.
When passwords appear in a data breach, they are often shared or sold across dark web marketplaces. Attackers then use automated tools to test stolen credentials on multiple websites in hopes that victims reused the same password across different accounts.
This type of attack is known as credential stuffing, and it remains one of the most common causes of account takeovers online.
One of the easiest ways to check if your passwords were stolen is by using password breach monitoring tools. Many modern password managers now include built-in security features that scan known breach databases for compromised credentials.
You can also use free online services that compare your credentials against leaked password databases. These tools help identify whether your passwords may already be circulating online after a data breach.
Warning signs that your passwords may already be compromised include:
- Unexpected password reset emails
- Accounts becoming locked
- Unrecognized login attempts
- Security alerts from websites
- Unauthorized purchases
- Missing access to online accounts
- Strange activity on email or social media accounts
If one of your passwords has been exposed, you should immediately:
- Change the password
- Create a new unique password
- Enable multi-factor authentication
- Update passwords on similar accounts
- Monitor for suspicious activity
Using the same password across multiple websites dramatically increases your risk. If attackers obtain one leaked password, they may attempt to access your:
- Banking accounts
- Shopping accounts
- Streaming services
- Social media accounts
- Work accounts
- Email inboxes
According to the Cybersecurity & Infrastructure Security Agency Password Security Guidelines, strong unique passwords combined with multi-factor authentication provide some of the best protection against credential theft and account compromise.
Password managers can also help generate and store complex passwords securely. Many security experts recommend using password managers because they reduce the temptation to reuse passwords across multiple websites.
Some identity theft protection services also include continuous credential monitoring. These tools automatically scan dark web breach databases and alert users when stolen passwords are detected online.
This type of monitoring can help reduce the risk of:
- Identity theft
- Financial fraud
- Account hijacking
- Email compromise
- Unauthorized purchases
Checking whether your passwords were stolen should become a regular part of your cybersecurity routine. New breaches happen constantly, and exposed credentials can remain active online for years if they are never updated.
The faster you detect compromised passwords, the better your chances of preventing serious long-term damage.
Best Free Tools to Check for Data Breaches
If you want to check if your information is on the dark web, several free tools can help you identify exposed email addresses, leaked passwords, and compromised accounts. These tools search known breach databases and security incident records to determine whether your personal information may already be circulating online.
While free tools usually do not provide full identity protection or continuous monitoring, they are a good starting point for detecting data breach exposure quickly.
One of the most trusted free breach-checking tools is Have I Been Pwned. This platform allows users to search email addresses against massive collections of leaked credentials from known data breaches. It can show:
- Which breaches affected your email
- What data types were exposed
- Whether passwords were leaked
- When the breach occurred
Another useful resource is Google Password Checkup. Google can scan saved credentials connected to your Google account and warn you if passwords were found in known breaches. This helps users identify weak or compromised passwords before attackers exploit them.
Apple users can also benefit from built-in security monitoring through iCloud Keychain. Apple now alerts users when saved passwords appear in known leaked credential databases.
Many antivirus and cybersecurity companies also offer free breach scanners that check:
- Email addresses
- Password exposure
- Dark web leaks
- Breached phone numbers
Some tools even provide limited dark web monitoring and breach notifications without requiring paid subscriptions.
When using free breach-checking tools, you should look for:
- Trusted cybersecurity providers
- Encrypted search systems
- Privacy-focused policies
- Real breach database coverage
- Regular breach updates
Free tools are useful for basic exposure checks, but they often lack:
- Continuous monitoring
- Identity theft insurance
- Credit monitoring
- Fraud recovery assistance
- Real-time dark web alerts
This is why many people eventually upgrade to identity theft protection services for ongoing protection and faster breach detection.
According to the U.S. Department of Justice Cybercrime Resources, early detection of leaked credentials can significantly reduce the impact of identity theft and online fraud.
If you discover your information has been exposed online, you should immediately:
- Change affected passwords
- Enable multi-factor authentication
- Monitor financial accounts
- Freeze your credit if necessary
- Remove unnecessary personal information from public websites
Regularly checking for data breaches is becoming increasingly important because cyberattacks happen constantly across businesses, apps, social media platforms, and online services.
Even if your information has not been exposed yet, proactive monitoring can help you respond quickly if future breaches occur.
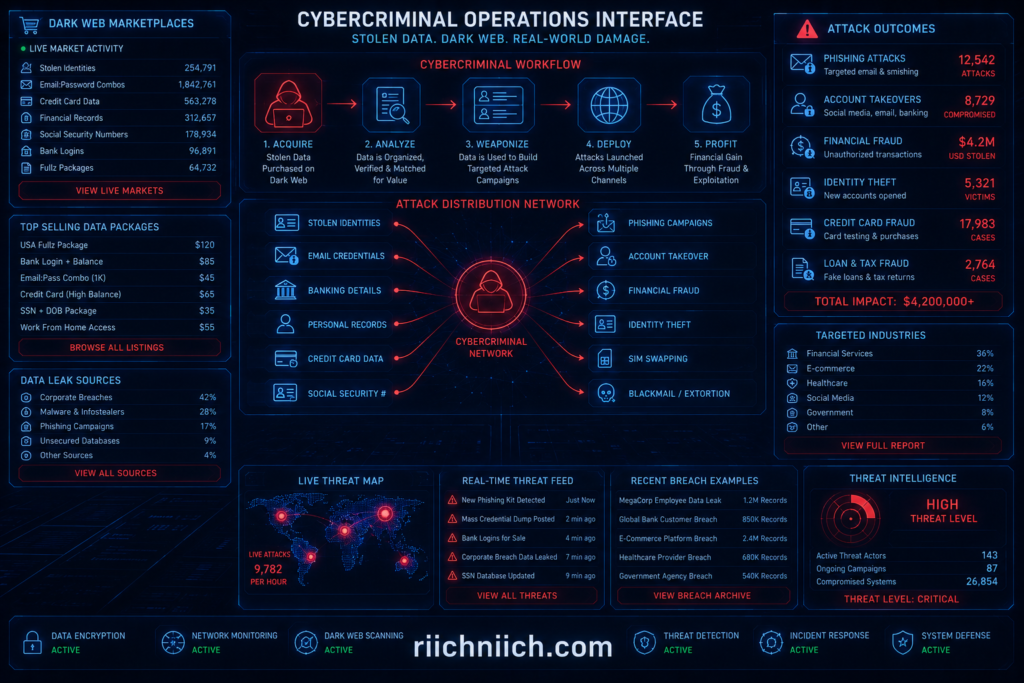
How Hackers Use Stolen Information From the Dark Web
When people check if their information is on the dark web, many are surprised to learn how valuable stolen personal data can be to cybercriminals. Hackers use leaked information in many different ways, ranging from phishing scams and account takeovers to full-scale identity theft and financial fraud.
Once personal data appears on the dark web, it can spread quickly across criminal marketplaces, encrypted forums, and private hacking communities. In many cases, stolen information is bought and resold multiple times between cybercriminal groups.
One of the most common uses for stolen data is credential stuffing attacks. Hackers take leaked email addresses and passwords from old breaches and automatically test them across:
- Banking websites
- Shopping platforms
- Social media accounts
- Streaming services
- Cryptocurrency exchanges
- Email providers
If victims reuse passwords across multiple accounts, attackers can gain access very quickly.
Cybercriminals also use stolen information for phishing attacks. When hackers already know details such as your:
- Full name
- Email address
- Phone number
- Employer
- Banking provider
their scams become much more convincing. This is known as targeted phishing or spear phishing.
Some attackers create fake login pages, customer support scams, or urgent security alerts designed to trick victims into revealing even more sensitive information.
Financial fraud is another major risk tied to dark web exposure. Stolen credit card numbers, banking details, and Social Security numbers may be used for:
- Unauthorized purchases
- Loan applications
- Tax fraud
- Credit fraud
- Insurance fraud
In some cases, hackers purchase complete identity packages called “fullz.” These packages may include:
- Full legal names
- Addresses
- Date of birth
- Social Security numbers
- Driver’s license information
- Banking credentials
Complete identity profiles are especially dangerous because they allow criminals to impersonate victims more easily.
Cybercriminals also target email accounts because email access often gives them control over password resets for other online services. Once attackers gain access to an email inbox, they may attempt to compromise:
- Online banking accounts
- Shopping accounts
- Social media profiles
- Cloud storage accounts
- Cryptocurrency wallets
If you want to check if your information is on the dark web, it is important to monitor more than just passwords. Comprehensive identity monitoring services can help detect:
- Breached credentials
- Identity theft risks
- Fraud-related activity
- Exposed financial information
- Dark web marketplace listings
The sooner you identify leaked information, the faster you can secure your accounts and reduce the risk of long-term damage.
Strong cybersecurity habits can also help protect you from future exposure, including:
- Using unique passwords
- Enabling multi-factor authentication
- Monitoring financial accounts
- Using password managers
- Removing unnecessary public personal information online
What to Do If Your Information Is Found on the Dark Web
If you check if your information is on the dark web and discover that your personal data has been exposed, acting quickly is extremely important. The faster you respond, the better your chances of preventing identity theft, financial fraud, and long-term account compromise.
If you believe your identity may already be compromised, follow these immediate recovery steps here:
What to Do Immediately If Your Identity Is Stolen
The first step is changing any compromised passwords immediately. If the leaked password was reused across multiple accounts, update every account that used the same or similar password. Cybercriminals often use stolen credentials in automated credential stuffing attacks to break into additional accounts.
When creating new passwords:
- Use unique passwords for every account
- Avoid simple or predictable phrases
- Use long passwords with mixed characters
- Store passwords securely inside a password manager
You should also enable multi-factor authentication (MFA) on important accounts whenever possible. MFA adds an additional security layer that makes it much harder for attackers to gain access even if they already have your password.
Focus first on securing:
- Email accounts
- Banking accounts
- Credit card accounts
- Shopping accounts
- Social media accounts
- Cryptocurrency wallets
If your financial information or Social Security number was exposed, consider freezing your credit with the major credit bureaus. A credit freeze helps prevent criminals from opening new accounts or loans in your name.
You should also monitor:
- Credit reports
- Bank statements
- Credit card activity
- Tax filings
- Login notifications
- Security alerts
Unexpected transactions or unfamiliar accounts could be early signs of identity theft.
If you notice suspicious activity, review these 13 warning signs someone may have already stolen your identity.
Another important step is removing unnecessary personal information from public people-search websites and data broker platforms. Publicly available information makes it easier for scammers and cybercriminals to target victims with phishing attacks and fraud schemes.
Many people also choose to use identity theft protection services after discovering leaked information online. These services may include:
- Dark web monitoring
- Identity theft alerts
- Credit monitoring
- Fraud recovery assistance
- Identity theft insurance
Continuous monitoring can help detect future leaks faster and reduce the chances of long-term damage.
According to the U.S. Federal Trade Commission Identity Theft Recovery Guide, victims of identity theft should document suspicious activity and report fraudulent accounts as quickly as possible.
You should also stay alert for:
- Phishing emails
- Scam calls
- Fake login pages
- Fraudulent text messages
- Unusual account activity
Cybercriminals may continue targeting exposed victims long after a breach occurs.
If you regularly check if your information is on the dark web, you can often catch problems early before attackers fully exploit your personal data. Early detection remains one of the best ways to reduce identity theft risks and secure your online accounts.
How to Protect Yourself After a Data Breach
After you check if your information is on the dark web and discover your data may have been exposed, taking immediate action can help reduce the risk of identity theft, financial fraud, and account compromise. Data breaches are becoming more common every year, and even major companies with strong security systems can become targets for cyberattacks.
The first step after a data breach is changing compromised passwords immediately. If you reused the same password on multiple accounts, update every account connected to that password. Attackers often use stolen credentials to attempt logins across banking sites, email providers, shopping platforms, and social media accounts.
Strong password security is critical after a breach. Experts recommend:
- Using unique passwords for every account
- Creating long complex passwords
- Avoiding personal information in passwords
- Storing credentials inside password managers
You should also enable multi-factor authentication (MFA) on important accounts. MFA adds an extra verification step that can block unauthorized access even if criminals already know your password.
Priority accounts to secure include:
- Email accounts
- Banking accounts
- Credit cards
- Investment accounts
- Healthcare portals
- Cloud storage accounts
- Cryptocurrency exchanges
Monitoring your financial activity is also extremely important after a breach. Review your:
- Bank transactions
- Credit card statements
- Credit reports
- Loan applications
- Tax records
Unexpected charges or unfamiliar accounts could signal identity theft.
Another effective step is freezing your credit with the major credit bureaus. Credit freezes make it harder for criminals to open new lines of credit using stolen personal information.
Removing exposed personal information from people-search sites and data broker databases can also reduce future risks. Public records and online profiles give scammers additional information that may be used in phishing attacks or fraud attempts.
Many people also use identity theft protection services after a breach because these tools can provide:
- Dark web monitoring
- Credit monitoring
- Identity theft alerts
- Fraud recovery support
- Real-time breach notifications
Continuous monitoring can help detect suspicious activity faster and improve your response time if additional leaks occur later.
You should also remain cautious about phishing scams after a breach. Cybercriminals often target breach victims with fake security alerts, scam phone calls, and fraudulent emails designed to steal even more information.
If you regularly check if your information is on the dark web, you can often identify problems earlier and secure your accounts before attackers fully exploit stolen data.
Protecting yourself after a data breach is not just about fixing one account — it is about strengthening your entire digital security setup for the future.
Best Identity Theft Protection Services for Dark Web Monitoring
If you regularly check if your information is on the dark web, using a dedicated identity theft protection service can make the process much easier and more effective. These services continuously monitor dark web marketplaces, breach databases, financial activity, and identity records to help detect suspicious activity before serious damage occurs.
Unlike free breach-checking tools that only perform one-time scans, identity theft protection services provide ongoing monitoring and real-time alerts when your information appears in newly leaked databases.
Some of the best identity theft protection services for dark web monitoring include:
- Aura
- LifeLock
- Identity Guard
Another growing option is NordProtect, which combines dark web monitoring, identity theft alerts, credit monitoring, and cybersecurity-focused protection tools into one platform.
Want a deeper breakdown of NordProtect’s monitoring and identity protection features? Read our full review here: NordProtect Review
These services typically offer features such as:
- Dark web monitoring
- Identity theft alerts
- Credit monitoring
- Fraud resolution support
- Password breach detection
- Financial account monitoring
- Identity theft insurance
According to , services like Aura and LifeLock consistently rank among the top identity theft protection providers because of their broad monitoring coverage and real-time alert systems.
Aura is especially popular for users who want an all-in-one cybersecurity and identity protection platform.
Thinking about using Aura for dark web monitoring and identity protection? Read our full Aura review here: Is Aura Worth It?
Aura includes:
- Dark web monitoring
- Three-bureau credit monitoring
- Password manager tools
- VPN protection
- Fraud alerts
- Identity theft insurance
Aura also monitors exposed personal information such as:
- Email addresses
- Social Security numbers
- Banking information
- Driver’s license records
- Password leaks
LifeLock is another major provider that combines identity monitoring with Norton cybersecurity tools. LifeLock offers:
- Dark web scanning
- Credit monitoring
- Device security
- VPN services
- Fraud recovery assistance
- Large insurance coverage options
Some users prefer LifeLock because of its extensive recovery support and broad identity monitoring coverage, while others choose Aura for its simpler pricing and bundled security tools.
Identity Guard focuses heavily on AI-powered fraud detection and identity monitoring. It provides dark web monitoring, risk alerts, and identity theft protection tools designed to help users respond quickly to suspicious activity.
Many of these services also provide family plans that help monitor children and other household members for identity theft risks.
When choosing an identity theft protection service for dark web monitoring, consider:
- Real-time alerts
- Credit bureau coverage
- Identity theft insurance
- Password breach detection
- Financial account monitoring
- Customer support quality
- Fraud recovery assistance
If you frequently check if your information is on the dark web, a dedicated monitoring service can help automate the process and provide earlier warnings when sensitive information becomes exposed online.
According to cybersecurity testing and review organizations, continuous monitoring and fast alert response times are among the most important features for reducing identity theft risks after data breaches.
Can You Remove Your Information From the Dark Web?
If you check if your information is on the dark web and discover leaked personal data, one of the first questions you may ask is whether it can actually be removed. Unfortunately, removing information from the dark web is often very difficult once data has already been stolen and distributed across cybercriminal networks.
In many cases, leaked credentials, passwords, email addresses, and identity records are copied and shared repeatedly across multiple underground forums and marketplaces. Once that happens, completely deleting the information becomes nearly impossible.
However, while you may not be able to fully erase stolen data from the dark web, you can still take important steps to reduce the risks and limit future exposure.
The most important step is securing any compromised accounts immediately. If exposed passwords or email addresses were found online, you should:
- Change passwords immediately
- Enable multi-factor authentication
- Use unique passwords for every account
- Monitor accounts for suspicious activity
If financial information or Social Security numbers were exposed, you should also:
- Freeze your credit
- Monitor credit reports
- Watch for fraudulent transactions
- Report identity theft if necessary
Another important strategy is reducing the amount of personal information available online.
👉 Remove your personal information from data broker websites automatically with Incogni here.
Cybercriminals often combine leaked dark web data with publicly available information from:
- Data broker websites
- People-search sites
- Social media profiles
- Public records databases
This is why many privacy experts recommend removing your information from data broker platforms whenever possible.
Services like Incogni and DeleteMe help users remove personal information from many online data broker databases automatically. While these services cannot erase information already circulating on the dark web, they can reduce future exposure and make it harder for scammers to build detailed identity profiles.
Identity theft protection services can also help monitor ongoing dark web activity tied to your information. These tools continuously scan for:
- Leaked passwords
- Exposed Social Security numbers
- Financial account leaks
- Fraud-related activity
- Newly breached credentials
You should also remain cautious about:
- Phishing emails
- Scam calls
- Fake security alerts
- Fraudulent login pages
- Suspicious text messages
Cybercriminals often target individuals repeatedly after discovering leaked information online.
If you regularly check if your information is on the dark web, you can often catch new exposures faster and respond before serious financial or identity damage occurs.
While fully removing data from the dark web is rarely guaranteed, strengthening your cybersecurity, monitoring your identity, and reducing your public online footprint can significantly lower your long-term risk.
How to Prevent Your Personal Information From Being Leaked Again
After you check if your information is on the dark web and secure exposed accounts, the next step is preventing future leaks. While no security setup is perfect, strong cybersecurity habits can dramatically reduce the chances of your personal information being exposed again.
One of the most important security practices is using unique passwords for every account. Password reuse remains one of the biggest reasons cybercriminals successfully compromise multiple accounts after a single breach. If one password gets leaked, attackers immediately test it across banking sites, email providers, shopping platforms, and social media accounts.
Using a password manager can help you:
- Generate strong passwords
- Store credentials securely
- Avoid password reuse
- Monitor for compromised passwords
Want stronger password protection? Here are the Best Password Managers for securing your online accounts.
You should also enable multi-factor authentication (MFA) on all important accounts. MFA adds another verification step that helps protect your accounts even if your password becomes exposed online.
Priority accounts for MFA include:
- Email accounts
- Banking accounts
- Shopping accounts
- Social media accounts
- Cryptocurrency platforms
- Cloud storage services
Another important step is reducing the amount of personal information publicly available online. Data brokers, people-search websites, and public records databases often expose:
- Phone numbers
- Addresses
- Family members
- Employment history
- Age information
Removing your data from these platforms can make it harder for cybercriminals to build identity profiles for phishing attacks and fraud schemes.
Want to reduce your online exposure even further? Compare the Best Data Removal Services here.
Privacy-focused services like Incogni and DeleteMe can help automate the data removal process from many broker databases.
You should also stay cautious when using public WiFi networks. Unsecured networks can expose sensitive information to attackers monitoring internet traffic. Using a trusted VPN service helps encrypt your connection and improve online privacy when browsing on public networks.
Keeping devices and software updated is another critical security habit. Many cyberattacks target outdated:
- Browsers
- Apps
- Operating systems
- Antivirus software
- Router firmware
Security updates often patch vulnerabilities before attackers can exploit them.
Phishing awareness is equally important. Avoid clicking suspicious:
- Email links
- Attachments
- Text messages
- Pop-up alerts
- Fake login pages
Even advanced security tools can fail if attackers successfully trick users into revealing sensitive information manually.
Many people also use identity theft monitoring services to continuously check if their information is on the dark web. These services can provide:
- Real-time breach alerts
- Credential monitoring
- Fraud detection
- Identity theft notifications
- Financial account monitoring
Preventing future leaks is not about relying on one single tool. The strongest protection comes from combining:
- Strong passwords
- Multi-factor authentication
- Privacy protection
- Secure browsing
- Ongoing monitoring
- Safe online habits
The more layers of protection you build, the harder it becomes for cybercriminals to exploit your personal information.
Conclusion: Should You Worry About Dark Web Exposure?
Yes — you should absolutely take dark web exposure seriously. If you check if your information is on the dark web and discover leaked personal data, ignoring it can increase your risk of identity theft, financial fraud, account takeovers, phishing attacks, and long-term privacy problems.
The reality is that data breaches have become extremely common. Even trusted companies, banks, healthcare providers, apps, and social media platforms experience cyberattacks that expose customer information online. Once stolen data appears on dark web marketplaces, cybercriminals may continue using and sharing it for years.
However, finding your information on the dark web does not automatically mean your identity has already been stolen. In many cases, early detection gives you enough time to secure accounts, change passwords, monitor financial activity, and strengthen your cybersecurity before serious damage occurs.
The biggest mistake most people make is waiting until fraud already happens before taking action.
If you regularly check if your information is on the dark web, you can often detect:
- Leaked passwords
- Exposed email addresses
- Breached financial information
- Identity theft risks
- Fraud-related activity
- Suspicious account exposure
This allows you to respond faster and reduce long-term risks.
Strong cybersecurity habits remain one of the best defenses against dark web exposure. Important protection steps include:
- Using unique passwords
- Enabling multi-factor authentication
- Monitoring financial accounts
- Removing personal information from data broker websites
- Using password managers
- Avoiding phishing scams
- Using identity theft monitoring services
Many people now use identity protection platforms with dark web monitoring because these services can automate breach detection and provide real-time alerts when personal information appears online.
Compare the top tools for monitoring fraud, data breaches, and identity theft in our full guide here:
Best Identity Theft Protection Services
Services that include:
- Dark web monitoring
- Credit monitoring
- Identity theft alerts
- Fraud recovery support
- Password breach detection
can significantly improve your ability to respond quickly after a breach.
According to the Cybersecurity & Infrastructure Security Agency (CISA) Secure Our World Initiative, proactive cybersecurity habits and ongoing monitoring are critical for reducing identity theft and online fraud risks in today’s digital environment.
The good news is that you are not powerless. While you may not be able to completely remove stolen data from the dark web, you can greatly reduce your risk by:
- Securing compromised accounts
- Improving password security
- Monitoring your identity
- Limiting your online exposure
- Using layered cybersecurity protection
Dark web exposure is becoming a normal part of modern online life — but strong security habits and early detection can make a huge difference.



