How your personal data ends up online is something most people do not fully understand until they discover their phone number, address, email, or personal details exposed across the internet. Data brokers, social media platforms, apps, public records, and data breaches constantly collect and share information about users online. In this guide, you will learn how companies collect your data, why your personal information appears online, how scammers use exposed information, and the best tools to protect your privacy and reduce your digital footprint.
Table of Contents
Why Your Personal Data Is Online
Your personal information is online for one simple reason: companies collect, store, share, and sell data constantly. If you have ever created a social media account, downloaded an app, signed up for a website, made an online purchase, or filled out a public form, parts of your digital identity may already be exposed across the internet.
Understanding how your personal data ends up online is important because exposed information can increase the risk of identity theft, phishing scams, spam calls, account takeovers, and financial fraud. Many people are shocked when they discover their phone number, home address, email address, or even family members appearing on people-search websites and data broker databases.
One of the biggest reasons your personal information appears online is data collection. Apps, websites, advertisers, and online services track user activity every day. This information is often shared with third-party marketing companies and data brokers that build detailed consumer profiles. These profiles can include:
- Full name
- Phone numbers
- Email addresses
- Home addresses
- Browsing habits
- Purchase history
- Location data
- Social media activity
Data brokers then sell or distribute this information to advertisers, marketers, recruiters, and sometimes even scammers.
Want to understand how these companies operate? Read our full guide on what a data broker is here!

Another major reason your personal data is online is because of data breaches. Large companies are frequently targeted by hackers who steal customer databases containing usernames, passwords, email addresses, and financial information. Once leaked, this data often spreads across underground forums, scam networks, and dark web marketplaces.
According to the Identity Theft Resource Center, data breaches continue exposing millions of records every year.
Social media also plays a major role in online exposure. Many users unknowingly share birthdays, locations, workplaces, family details, and personal photos publicly. Cybercriminals and data collection companies can use this information to build identity profiles or target victims with scams.
Even public records contribute to the problem. Property records, voter registrations, court documents, and business filings can sometimes become searchable online through government databases or third-party aggregation websites.
The reality is that your information can spread online without your direct permission. Companies legally collect data through terms of service agreements that most users never read. Over time, your personal data may circulate across hundreds of databases and websites.
This is why many people now use privacy protection and data removal services to reduce their digital exposure. Services like Incogni and DeleteMe help remove personal information from data broker websites automatically, which can lower the risk of identity theft and unwanted tracking.
How Data Brokers Collect Your Information
Data brokers collect personal information from dozens of online and offline sources every day. If you are wondering how your personal data ends up online, data brokers are one of the biggest reasons. These companies gather, organize, and sell massive amounts of consumer information to advertisers, marketers, businesses, and sometimes even third parties you have never interacted with directly.
Many people do not realize how much information is being collected about them. Data brokers can build detailed profiles containing your:
- Full name
- Phone number
- Home address
- Email address
- Age and birthday
- Family members
- Income estimates
- Shopping habits
- Location history
- Social media activity
- Browser and search behavior
👉 Remove your personal information from data broker websites automatically with Incogni here!
One common method data brokers use is website tracking technology. Many websites install cookies, tracking pixels, and advertising scripts that monitor your online behavior. These tools can track which pages you visit, what products you search for, how long you stay on websites, and even what links you click.
Apps on your phone can also collect large amounts of personal data. Some apps request access to your location, contacts, microphone, camera, or browsing activity. That information may then be shared with third-party advertising and analytics companies.
Social media platforms are another major source of data collection. Every post, like, follow, comment, and location check-in helps companies build advertising and identity profiles. Even information you never post publicly can sometimes be collected through app permissions and platform tracking systems.
Offline sources also contribute to online exposure. Data brokers may purchase records from:
- Retail loyalty programs
- Sweepstakes entries
- Warranty registrations
- Credit applications
- Public records databases
- Property records
- Voter registrations
Over time, these records become combined into one large consumer profile that may appear across multiple people-search websites online.
According to the Electronic Frontier Foundation (EFF), online tracking systems can follow users across thousands of websites and services.
One reason this industry is so powerful is because data collection is highly automated. Advanced algorithms continuously gather, organize, and update personal records in real time. This is why your information may quickly spread across dozens or even hundreds of websites without you realizing it.
Unfortunately, scammers and cybercriminals can sometimes use exposed broker data for phishing attacks, spam calls, identity theft, and fraud attempts. The more public your personal information becomes, the easier it may be for attackers to target you.
This is why many privacy experts recommend using data removal services to reduce online exposure. Services like Incogni and DeleteMe help users automatically remove information from data broker sites, which can reduce spam, unwanted tracking, and identity theft risks.
Wondering if the service is actually effective? Read our full Incogni review here.
Public Records and Government Databases
Another major reason how your personal data ends up online is through public records and government databases. Many people are surprised to learn that certain personal information can legally become publicly accessible through local, state, or federal record systems.
Public records are documents or pieces of information created and maintained by government agencies. In many cases, these records are considered publicly accessible by law. Data brokers and people-search websites often collect this information, organize it into searchable profiles, and publish it online.
Some common examples of public records include:
- Property ownership records
- Court records
- Marriage and divorce records
- Business registrations
- Professional licenses
- Voter registration records
- Bankruptcy filings
- Criminal records
- Building permits
Once these records are digitized, they can spread across the internet very quickly. Data broker websites often scrape or purchase this information and combine it with data collected from social media platforms, apps, and advertisers.
This is one of the main reasons your home address, phone number, relatives, or age may appear online even if you never personally posted them yourself.
Many people searching for how to remove personal information from the internet discover that public records are one of the hardest sources to control. In some cases, records cannot be completely removed because they are legally public documents. However, you may still be able to reduce exposure by removing your information from data broker and people-search websites that redistribute the data.
Government websites are not always the direct problem. The bigger issue is that third-party companies copy and republish public information across hundreds of searchable databases online. This creates large digital identity profiles that can increase privacy and identity theft risks.
According to the National Conference of State Legislatures (NCSL), states continue debating consumer privacy laws and data-sharing regulations as online data collection expands.
Cybercriminals can sometimes use exposed public information for phishing attacks, social engineering scams, account recovery fraud, and identity theft attempts. Even small details like your address history or relatives can help attackers build more convincing scams.
Some people-search websites make it extremely easy for strangers to find:
- Current addresses
- Previous addresses
- Phone numbers
- Family connections
- Property ownership history
This is why privacy experts often recommend combining data removal services with stronger online privacy habits. Services like Incogni and DeleteMe can help reduce exposure by submitting removal requests to data broker websites automatically.
The less publicly available information attached to your name, the harder it becomes for scammers, advertisers, and unknown third parties to track your digital footprint online.

Social Media Oversharing Risks
Social media is one of the biggest reasons how your personal data ends up online. Every photo, location check-in, comment, friend request, and personal update can contribute to your digital footprint. Many people unknowingly expose sensitive information that can later be collected by data brokers, advertisers, scammers, and cybercriminals.
Oversharing on social media may seem harmless, but it can create serious privacy and identity theft risks over time. Platforms like Facebook, Instagram, TikTok, X, and LinkedIn collect massive amounts of user data while also encouraging users to share personal details publicly.
You can reduce these risks by following our guide on How to Stay Safe Social Media.
Some of the most commonly exposed information includes:
- Full names
- Birthdays
- Phone numbers
- Email addresses
- Workplace information
- Family relationships
- Vacation locations
- Daily routines
- Photos of homes, cars, or IDs
This information can help companies build advertising profiles, but it can also make it easier for scammers to target users with phishing attacks, impersonation scams, and identity theft attempts.
One major problem is that social media platforms track far more than what users post publicly. Many platforms collect browsing behavior, location history, device information, app activity, and interaction patterns. This data is often shared with advertising partners and analytics companies.
If you are wondering why your personal information is online, social media tracking is a major reason. Even deleted posts or old accounts may continue contributing to your digital footprint through archived data and third-party collection systems.
Cybercriminals frequently use social media for social engineering attacks. For example, attackers may study a person’s profile to learn:
- Pet names
- Family member names
- Birthdays
- Schools attended
- Work history
- Favorite locations
These details are often used to guess passwords, bypass security questions, or create highly convincing scam messages.
According to the Cybersecurity and Infrastructure Security Agency (CISA), limiting personal information shared online can help reduce cyber risks and identity theft exposure.
Another hidden risk involves location sharing. Posting real-time vacation photos, gym check-ins, or live event updates can reveal patterns about where you live, work, and travel. This information may be valuable to stalkers, scammers, or criminals monitoring public profiles.
Data brokers also scan social media platforms for publicly available information. Over time, your posts and interactions may become part of larger identity profiles sold across marketing and people-search databases.
To reduce social media privacy risks:
- Set accounts to private
- Limit location sharing
- Avoid posting sensitive personal details
- Remove old unused accounts
- Review app permissions regularly
- Use strong passwords and two-factor authentication
Many users also combine stronger privacy habits with data removal services like Incogni and DeleteMe to reduce how much personal information appears online across broker sites and people-search databases.
The less personal information connected to your online identity, the harder it becomes for companies and cybercriminals to track, profile, or exploit your data.

Apps and Websites That Track Your Activity
Apps and websites play a major role in how your personal data ends up online. Every time you browse the internet, shop online, use social media, or download a mobile app, your activity may be tracked, analyzed, and shared with third parties.
Many companies collect user data to improve advertising, personalize recommendations, and increase engagement. However, this tracking can also contribute to privacy risks, identity exposure, and unwanted data sharing across the internet.
Some of the most commonly collected information includes:
- Search history
- Browsing behavior
- Purchase activity
- Device information
- GPS location data
- IP addresses
- App usage habits
- Ad clicks and interactions
This information helps companies build detailed digital profiles that may later be sold to advertisers and data brokers.
One of the most common tracking tools is browser cookies. Cookies are small files stored on your device that remember your activity across websites. While some cookies improve user experience, others are designed specifically for advertising and user tracking.
Many websites also use tracking pixels and analytics scripts. These tools can monitor:
- Which pages you visit
- How long you stay on a website
- What products you view
- What buttons you click
- What ads you interact with
This is one reason ads sometimes seem to “follow” you across the internet after visiting a website once.
Mobile apps can collect even more sensitive information. Some apps request access to:
- Contacts
- Camera
- Microphone
- Photos
- Precise location
- Bluetooth connections
Users often approve these permissions without realizing how much data is being shared behind the scenes.
According to the Mozilla Foundation, many apps and connected devices collect large amounts of personal data that users may not fully understand.
Another major issue is third-party data sharing. Many apps and websites share collected information with advertising networks, analytics companies, and marketing partners. Over time, this data can spread across hundreds of databases online.
This is one reason why people searching for how to protect personal information online often discover their data appearing on people-search websites or targeted advertising platforms.
Some websites even use fingerprinting technology, which can identify users based on their browser settings, screen size, device type, and other technical details. Unlike cookies, fingerprinting is harder to block and can continue tracking users across multiple sites.
To reduce online tracking risks, privacy experts often recommend:
- Limiting app permissions
- Clearing browser cookies regularly
- Using privacy-focused browsers
- Disabling ad tracking settings
- Avoiding unnecessary app downloads
- Using VPN services on public networks
Many users also combine these steps with data removal services like Incogni and DeleteMe to reduce how much personal information remains visible online.
The more websites and apps collect your data, the larger your digital footprint becomes. Reducing unnecessary tracking can help improve privacy, reduce spam, and lower the risk of identity theft.
Data Breaches and Hacked Databases
Data breaches are one of the biggest reasons how your personal data ends up online. Even if you are careful with your privacy, your information can still become exposed when companies, apps, or websites are hacked.
A data breach happens when cybercriminals gain unauthorized access to databases containing sensitive customer information. Once stolen, this data is often leaked online, sold on underground marketplaces, or shared across cybercriminal networks.
Some of the most commonly exposed information in data breaches includes:
- Email addresses
- Passwords
- Phone numbers
- Home addresses
- Credit card information
- Social Security numbers
- Login credentials
- Date of birth information
When large companies experience breaches, millions of user records can become exposed at once. This is why many people discover their personal information online even if they never intentionally shared it publicly.
Hackers often target businesses that store massive amounts of customer data. Retailers, social media platforms, healthcare providers, financial institutions, and online services are common targets because of the valuable information they collect.
Learn more about the methods cybercriminals use in our guide on How Hackers Get Your Personal Data!
Once data is stolen, cybercriminals may use it for:
- Identity theft
- Phishing attacks
- Account takeovers
- Financial fraud
- Spam campaigns
- Credential stuffing attacks
Credential stuffing happens when attackers use leaked passwords from one breach to try logging into other accounts. This is one reason why using the same password across multiple websites can be extremely dangerous.
According to IBM’s Cost of a Data Breach Report, breached data can remain exposed for months before organizations fully detect and contain the incident.
Many hacked databases eventually appear on dark web marketplaces where cybercriminals buy and sell stolen information. In some cases, leaked databases become publicly searchable online, allowing scammers and data brokers to collect and redistribute the information even further.
This contributes heavily to how your personal information spreads online over time.
Another major issue is that breached information often remains online permanently. Even after a company fixes the breach, stolen records may continue circulating across forums, scam networks, and people-search databases for years.
This is why cybersecurity experts recommend taking immediate action after a breach notification, including:
- Changing passwords immediately
- Enabling two-factor authentication
- Monitoring financial accounts
- Watching for phishing emails
- Freezing credit if necessary
- Using identity theft monitoring services
Many people also use identity protection and data removal services to reduce exposure after a breach. Services like Aura, Incogni, and DeleteMe can help monitor suspicious activity and reduce the amount of exposed personal information available online.
The more breached information attached to your digital identity, the higher the risk of fraud, scams, and account compromise. Taking proactive privacy steps can help reduce long-term exposure.

How Companies Buy and Sell Your Information
Many people are surprised to learn that personal data has become a massive industry. One of the biggest reasons how your personal data ends up online is because companies regularly buy, share, and sell consumer information behind the scenes.
Every time you create an account, shop online, sign up for newsletters, use mobile apps, or browse websites, companies may collect information about your behavior. That data can then be shared with advertisers, marketing firms, analytics companies, and data brokers.
Some companies collect information directly from users, while others purchase data from third-party sources to build larger consumer profiles.
Common types of information companies buy and sell include:
- Names and email addresses
- Phone numbers
- Home addresses
- Shopping history
- Browsing activity
- Device information
- Income estimates
- Interests and hobbies
- Location history
- Social media engagement
This information helps businesses create targeted advertising campaigns, personalized recommendations, and detailed customer profiles.
Many websites include data-sharing practices inside their privacy policies and terms of service agreements. Most users accept these agreements without fully understanding how much information may be collected or shared.
Advertising networks are one of the largest drivers of online data collection. Companies use tracking systems to monitor user behavior across multiple websites and apps. This allows advertisers to create detailed profiles based on browsing habits, purchases, search history, and online activity.
This is one reason why users often see highly personalized ads shortly after searching for products or visiting websites.
Data brokers take this process even further by combining information from multiple sources into massive searchable databases. These databases may contain thousands of data points tied to a single person.
According to the Federal Trade Commission (FTC), the data broker industry collects and shares large amounts of consumer information, often with limited transparency for users.
One major concern is that consumers often lose control over where their information spreads. Once data is shared between multiple companies, it may continue circulating across advertising networks, marketing databases, and people-search websites for years.
Some companies also use predictive analytics and artificial intelligence to analyze user behavior patterns. This can help businesses estimate things like purchasing habits, financial status, or personal interests based on collected data.
Unfortunately, the more widely your information spreads, the greater the risk of:
- Spam calls and emails
- Phishing scams
- Identity theft
- Targeted scam campaigns
- Unauthorized data exposure
This is why many people searching for how to remove personal information from the internet turn to privacy protection and data removal services.
Reducing your digital footprint often requires limiting app permissions, adjusting privacy settings, opting out of data collection when possible, and removing information from data broker sites.
Services like Incogni and DeleteMe can help automate the removal process by sending opt-out requests to data brokers that collect and sell consumer information online.
The less data companies can collect and share about you, the easier it becomes to protect your privacy and reduce long-term online exposure.
Why Your Phone Number and Address Appear Online
If you have ever searched your name online and found your phone number or home address listed on random websites, you are not alone. One of the most common reasons how your personal data ends up online is through people-search sites and data broker databases that collect and publish personal contact information.
Many users are shocked to discover how easily strangers can find their personal details online. In many cases, your information may appear on dozens of websites without your direct permission.
Some of the most common sources of exposed phone numbers and addresses include:
- Data broker websites
- Public records
- Online account registrations
- Social media platforms
- Marketing databases
- Shopping and loyalty programs
- Old online accounts
- Mobile app data collection
Over time, companies combine information from multiple sources to create detailed online profiles connected to your identity.
Data brokers are one of the biggest contributors to this problem. These companies gather personal information from public records, advertisers, retailers, and online tracking systems. They then organize the data into searchable databases that may include:
- Current address
- Previous addresses
- Phone numbers
- Email addresses
- Relatives and associates
- Age and birth year
Some people-search websites make this information publicly searchable for anyone online.
Another major reason your information appears online is because of account signups and online purchases. Many websites request phone numbers, addresses, and personal details during registration. In some cases, this data may later be shared with marketing partners or data collection companies.
Even old accounts can continue exposing information years later. Forgotten social media accounts, outdated shopping profiles, and inactive services may still contain publicly accessible personal details.
According to the Better Business Bureau (BBB), scammers frequently use publicly available phone numbers and addresses for phishing scams, robocalls, and identity fraud attempts.
Another hidden issue is that once your information spreads online, it can quickly replicate across multiple databases. One people-search website may copy information from another source, causing your phone number and address to appear on dozens of websites simultaneously.
This can lead to:
- Spam calls
- Scam text messages
- Robocalls
- Phishing attempts
- Identity theft risks
- Unwanted marketing outreach
Many people searching for how to remove personal information from the internet specifically want to remove their phone number and address from data broker sites.
Fortunately, there are ways to reduce exposure. Privacy experts often recommend:
- Removing old unused accounts
- Updating social media privacy settings
- Avoiding public directory listings
- Opting out of people-search websites
- Using identity and privacy protection services
Manual removal can take significant time because many broker websites require separate opt-out requests. This is why many users turn to services like Incogni and DeleteMe, which help automate the removal process across multiple data broker platforms.
Not sure which service is better? Compare both tools in our full Incogni vs DeleteMe comparison.
Reducing the visibility of your phone number and address online can help lower the risk of spam, scams, and identity theft over time.

How Scammers Use Exposed Personal Data
One of the biggest dangers of how your personal data ends up online is that scammers can use exposed information to target victims more effectively. The more personal details criminals can find about you, the easier it becomes for them to create convincing scams, steal accounts, or commit identity theft.
Many cybercriminals collect information from:
- Data broker websites
- Social media profiles
- Public records
- Data breaches
- Phishing attacks
- Hacked databases
Once scammers gather enough information, they can build detailed identity profiles that help them impersonate victims or bypass security systems.
Common types of exposed personal data scammers look for include:
- Full names
- Phone numbers
- Email addresses
- Home addresses
- Birthdays
- Family member names
- Passwords
- Financial information
Even small pieces of information can become dangerous when combined together.
One of the most common scams involving exposed personal data is phishing. Attackers send fake emails, text messages, or phone calls designed to look legitimate. Because scammers may already know your name, address, or account details, these scams can appear highly convincing.
For example, a scammer may pretend to be:
- Your bank
- A delivery company
- A government agency
- A social media platform
- A customer support representative
The goal is usually to trick victims into revealing passwords, financial information, or verification codes.
Another major risk is account takeover fraud. If hackers obtain leaked passwords or personal details from data breaches, they may attempt to access email accounts, banking apps, shopping accounts, or social media profiles.
This becomes even more dangerous when people reuse the same password across multiple websites.
According to the Federal Communications Commission (FCC), scam calls and phishing attacks continue increasing as criminals use stolen consumer data to target victims more effectively.
Identity theft is another serious threat connected to exposed personal information. Criminals may use stolen data to:
- Open credit accounts
- File fraudulent tax returns
- Apply for loans
- Access medical services
- Commit financial fraud
👉 Protect yourself from identity theft before scammers can misuse your information with Aura here!
Some scammers also use social engineering techniques to manipulate victims psychologically. By researching social media accounts and public records, attackers can create highly personalized scams that appear trustworthy.
This is why reducing your online exposure is extremely important. The less personal information available online, the harder it becomes for scammers to target you.
Privacy experts often recommend:
- Using strong unique passwords
- Enabling two-factor authentication
- Monitoring financial accounts regularly
- Avoiding suspicious links and messages
- Removing exposed information from broker sites
- Using identity monitoring tools
Many users also rely on privacy services like Incogni and DeleteMe to reduce the amount of publicly accessible personal information available to scammers online.
Protecting your digital footprint is not just about privacy anymore — it is also about reducing fraud and identity theft risks before criminals can exploit your information.
How to Check What Information Is Exposed Online
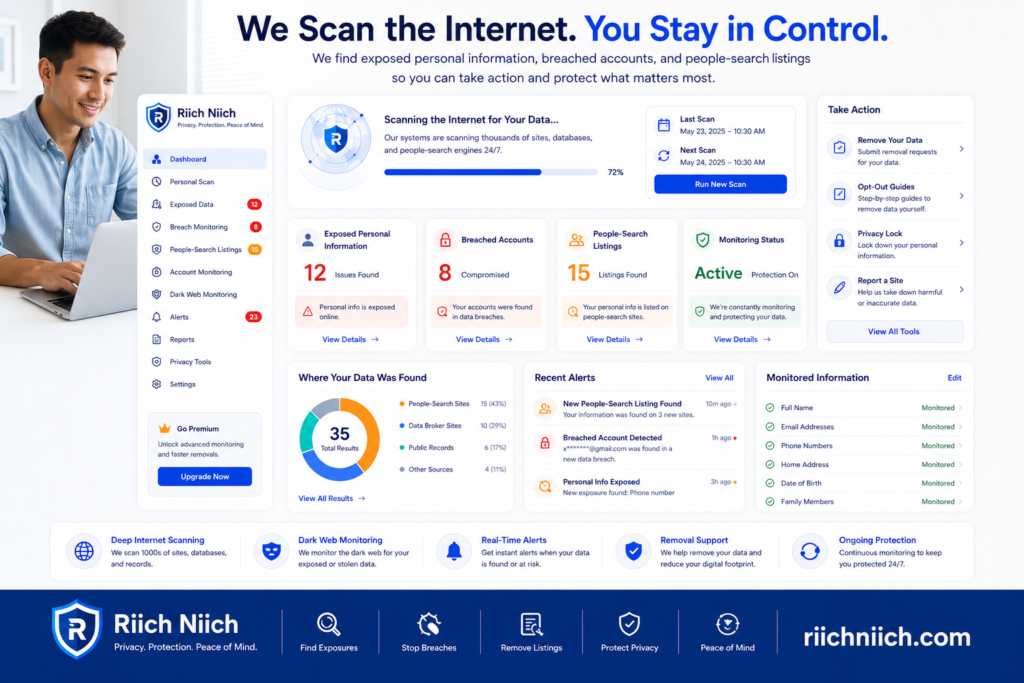
If you are wondering how your personal data ends up online, one of the first steps is learning how to check what information is already exposed. Many people do not realize how much of their personal data is publicly accessible until they search for it themselves.
Your digital footprint may include information collected from social media accounts, data brokers, public records, old online accounts, marketing databases, and data breaches. Over time, this information can spread across dozens of websites without your knowledge.
Checking your exposed information online can help you identify privacy risks before scammers or cybercriminals take advantage of them.
Some of the most common types of exposed personal information include:
- Full name
- Phone number
- Home address
- Email address
- Birth year
- Family members
- Social media profiles
- Old usernames
- Password breach history
One of the easiest ways to start is by searching your own information on search engines. Try searching:
- Your full name
- Your phone number
- Your email address
- Your home address
- Old usernames or screen names
You may discover profiles on people-search websites, old forum posts, social media accounts, or leaked information connected to your identity.
Another important step is checking whether your email addresses or passwords were exposed in a data breach. Cybercriminals frequently use leaked credentials for phishing attacks and account takeovers.
Websites like Have I Been Pwned allow users to check whether email addresses have appeared in known data breaches.
People-search websites are another major source of exposed information. These websites often display:
- Addresses
- Phone numbers
- Relatives
- Age information
- Property history
Many users searching for how to remove personal information from the internet discover their data appearing across multiple broker sites at the same time.
If you want to reduce your online exposure, read our complete guide on How to Remove Your Personal Information from the Internet.
You should also review your social media privacy settings carefully. Check what information is visible publicly, including:
- Profile details
- Friend lists
- Photos
- Location history
- Tagged posts
Even old inactive accounts can continue exposing personal information online.
According to the National Cybersecurity Alliance, regularly reviewing online accounts and privacy settings can help reduce digital exposure and identity theft risks.
Another useful step is monitoring financial and identity activity for suspicious behavior. Unexpected account notifications, unfamiliar credit inquiries, or strange login alerts may indicate that exposed information is already being misused.
To reduce your online exposure, privacy experts often recommend:
- Removing unused online accounts
- Updating privacy settings
- Using strong unique passwords
- Enabling two-factor authentication
- Opting out of data broker websites
- Using identity monitoring tools
Many users also use privacy services like Incogni and DeleteMe to automate the process of finding and removing exposed information from data broker and people-search websites.
The sooner you identify what information is exposed online, the easier it becomes to protect your privacy and reduce long-term identity theft risks.
How to Remove Your Personal Information From the Internet
If you are concerned about how your personal data ends up online, the good news is that you can take steps to reduce your digital footprint and remove exposed information from many websites. While it is difficult to erase every piece of personal data completely, reducing your online exposure can help lower the risk of identity theft, phishing scams, spam calls, and unwanted tracking.
Personal information often appears online through:
- Data broker websites
- People-search platforms
- Social media accounts
- Public records
- Old online accounts
- Data breaches
- Marketing databases
The first step is identifying where your information appears online. Search for your:
- Full name
- Phone number
- Email address
- Home address
- Old usernames
This can help you locate websites displaying your personal details.
One of the most effective ways to reduce exposure is removing your information from data broker and people-search websites. These sites often collect and publish details such as addresses, phone numbers, relatives, and age information.
Many broker sites offer opt-out forms that allow users to request removal manually. However, the process can be time-consuming because each website typically requires separate requests and periodic follow-ups.
This is why many users turn to automated privacy services like Incogni and DeleteMe. These services help submit removal requests to multiple data broker websites automatically, saving significant time and helping reduce online exposure more consistently.
Another important step is cleaning up old online accounts. Unused social media profiles, outdated shopping accounts, and abandoned forum accounts may still contain publicly visible information.
You should also review privacy settings on:
- Social media platforms
- Mobile apps
- Shopping websites
- Search engines
- Browser accounts
Limiting public visibility can help reduce how much information companies and scammers can collect about you.
According to Google’s Safety Center, users can request removal of certain sensitive personal information from Google Search results under specific circumstances.
Data breach exposure should also be addressed immediately. If your information has appeared in a breach:
- Change passwords immediately
- Enable two-factor authentication
- Monitor financial accounts
- Watch for phishing attempts
- Use identity monitoring tools
Many cybersecurity experts also recommend using password managers to create strong unique passwords for every account.
Here are the best password managers to protect your accounts from breaches and credential theft.
Another helpful strategy is reducing future data collection by:
- Disabling ad tracking
- Limiting app permissions
- Avoiding unnecessary account signups
- Using privacy-focused browsers
- Using VPN services on public WiFi
The less information companies collect, the smaller your digital footprint becomes over time.
Completely removing personal information from the internet is difficult because some public records may remain legally accessible. However, reducing exposure across broker websites and search engines can still significantly improve your privacy and reduce scam risks.

Best Tools to Protect Your Privacy Online
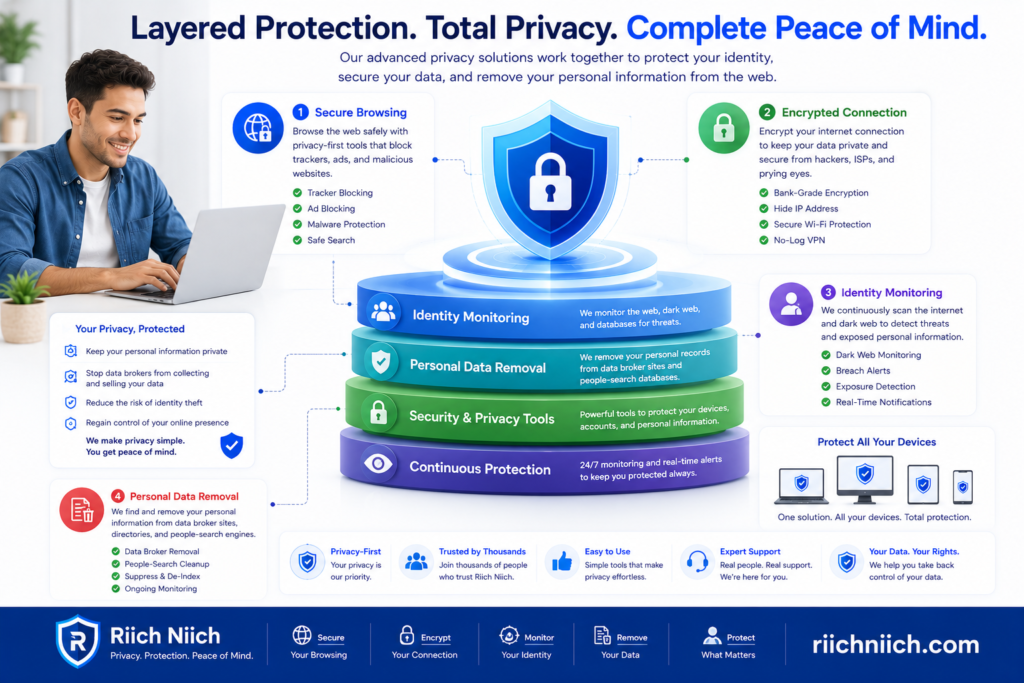
Understanding how your personal data ends up online is only the first step. The next step is protecting your information before scammers, data brokers, advertisers, and cybercriminals can continue collecting and exposing your data.
Today, privacy protection requires more than just using strong passwords. Personal information spreads across apps, websites, marketing databases, public records, and breached systems constantly. Using the right cybersecurity and privacy tools can help reduce your digital footprint and improve online security.
Some of the best tools to protect your privacy online include:
- Data removal services
- VPN services
- Password managers
- Identity theft protection tools
- Antivirus software
- Privacy-focused browsers
Each tool helps protect a different part of your digital life.
Data Removal Services
Data removal services help remove personal information from data broker and people-search websites. These services are extremely useful for reducing exposed phone numbers, addresses, relatives, and searchable online profiles.
Popular services like Incogni and DeleteMe automate the opt-out process across multiple broker databases. This can help reduce spam calls, phishing risks, and identity theft exposure over time.
Many people searching for how to remove personal information from the internet start with data removal tools because manually contacting broker websites can take significant time.
VPN Services
VPNs (Virtual Private Networks) help protect your internet activity by encrypting your connection and hiding your IP address. This makes it harder for advertisers, trackers, and hackers to monitor your browsing activity.
VPNs are especially important when using:
- Public WiFi
- Airports
- Hotels
- Coffee shops
- Shared networks
Public networks can expose your information to attackers. See the biggest public WiFi dangers here.
Popular VPN services like NordVPN, Surfshark, and ProtonVPN help improve online privacy while reducing tracking risks.
According to the Cybersecurity & Infrastructure Security Agency (CISA), encrypted internet connections help reduce certain online security risks.
Password Managers
Weak or reused passwords are one of the biggest cybersecurity risks online. Password managers help users generate and store strong unique passwords securely.
Using a password manager reduces the risk of:
- Credential stuffing attacks
- Account takeovers
- Password reuse vulnerabilities
Many password managers also include breach monitoring and security alerts.
Identity Theft Protection Services
Identity protection tools help monitor sensitive information for signs of fraud or misuse.
Compare the top monitoring tools in our guide to the Best Identity Theft Protection Services.
Services like Aura can monitor:
- Credit activity
- Dark web exposure
- Financial account alerts
- Identity theft warnings
These services can help users respond faster if personal information becomes compromised.
Antivirus and Device Security Tools
Antivirus software helps protect devices from malware, spyware, ransomware, and malicious downloads. Modern security software may also include:
- Web protection
- Scam detection
- Email filtering
- Phishing protection
Keeping devices updated and secured helps reduce the risk of hackers stealing personal data directly from your devices.
Privacy-Focused Browsers and Search Engines
Privacy-focused browsers and search engines help reduce tracking and targeted advertising. These tools can block:
- Tracking cookies
- Fingerprinting scripts
- Ad trackers
- Data collection systems
Reducing online tracking helps shrink your digital footprint over time.
No single tool can completely eliminate online privacy risks. However, combining multiple layers of protection can significantly improve online security and reduce how much personal information becomes exposed online.
Final Verdict: Can You Stop Your Data From Spreading Online?
Completely stopping your personal data from spreading online is difficult, but you can significantly reduce your exposure and take back more control of your privacy. Understanding how your personal data ends up online is the first step toward protecting yourself from identity theft, scams, tracking, and unwanted data collection.
Today, personal information spreads through:
- Data brokers
- Social media platforms
- Public records
- Apps and websites
- Online purchases
- Data breaches
- Advertising networks
The internet constantly collects, shares, and stores user data. This means your digital footprint can continue growing unless you actively manage your privacy settings and reduce unnecessary exposure.
The good news is that there are effective ways to limit how much personal information remains accessible online.
One of the most important steps is reducing the amount of information available on data broker and people-search websites. Removing exposed phone numbers, addresses, and personal records can help reduce spam calls, phishing scams, and identity theft risks.
Privacy protection tools like Incogni and DeleteMe can help automate this process by sending removal requests to broker websites on your behalf. This saves time and helps reduce how much personal information remains searchable online.
Compare the top privacy tools in our guide to the Best Data Removal Services.
It is also important to improve your overall cybersecurity habits by:
- Using strong unique passwords
- Enabling two-factor authentication
- Limiting social media sharing
- Reviewing app permissions
- Using VPN services on public WiFi
- Monitoring accounts for suspicious activity
These steps help reduce how much information companies and cybercriminals can collect over time.
Another important reality is that online privacy requires ongoing maintenance. Even after removing exposed data, new information can continue appearing online through new accounts, marketing databases, public records, or future data breaches.
This is why many privacy experts recommend combining:
- Data removal services
- Identity theft monitoring
- Password managers
- VPN protection
- Privacy-focused browsing habits
Using multiple layers of protection creates a stronger long-term privacy strategy.
You can improve your online safety further with these essential cybersecurity tips everyone should know.
According to the Electronic Privacy Information Center (EPIC), consumers should actively manage privacy settings and limit unnecessary data collection whenever possible.
The internet may never become completely private, but you can make yourself much harder to track, profile, and target. Reducing your digital footprint helps lower the risk of identity theft, phishing attacks, spam campaigns, and online scams.
You can also follow our complete guide on How to Protect Yourself from Identity Theft.
If you are serious about protecting your personal information, the best time to start is now. The earlier you reduce your online exposure, the easier it becomes to protect your identity and maintain better privacy moving forward.





