How hackers get your personal data is something most people don’t think about—until it’s too late. The reality is, cyber-criminals don’t need advanced skills to access your information. They rely on simple tactics like phishing, data breaches, and weak passwords to collect and exploit personal data every day.
In this guide, you’ll learn exactly how hackers get your personal data, the warning signs to watch for, and most importantly, how to protect yourself before serious damage occurs.
🔍 Quick Insight: How Hackers Really Get Your Data
Hackers don’t usually “break in” like you see in movies.
Most of the time, they collect your personal information slowly — through phishing emails, data breaches, weak passwords, and unsecured networks.
👉 By the time you notice, your information may already be exposed.
Table of Contents
How Hackers Get Your Personal Data (Explained Simply)
Understanding how hackers get your personal data doesn’t require technical expertise — in fact, most cyber-criminals rely on simple, repeatable methods that target everyday internet users. The truth is, hackers are not always “breaking in” to your accounts. Instead, they’re often taking advantage of weak security habits, data leaks, and human error. You can learn more about the full process in our guide on How Identity Theft Happens.
At a basic level, hackers collect personal data in three main ways: tricking you, finding exposed data, or exploiting weak security systems.
Most Attacks Start With Small Pieces of Information
Hackers rarely get everything at once.
They often gather small details over time — an email here, a password there — until they have enough to access your accounts.
👉 This is why even minor data exposure can lead to bigger problems.
1. Hackers Trick You Into Giving Them Information
One of the most common ways hackers get your personal data is through deception.
This includes:
- Fake emails pretending to be your bank or a trusted company
- Text messages asking you to “verify” your account
- Fake websites that look identical to real login pages
This method is known as phishing, and it works because it targets human behavior, not just technology.
According to the Federal Trade Commission, phishing scams are one of the leading causes of identity theft each year.
2. Hackers Find Your Data From Breaches
Another major way hackers get your personal data is through large-scale data breaches.
When companies get hacked, your information may be exposed, including:
- Email addresses
- Passwords
- Social Security numbers
- Credit card details
Hackers don’t always steal this data themselves — they often buy it on the dark web and use it to access your accounts.
You can check if your data has been exposed using tools like Have I Been Pwned.
3. Hackers Exploit Weak Passwords
Weak or reused passwords make it incredibly easy for hackers to access your accounts.
Cyber-criminals use automated tools to:
- Test common passwords (like “123456” or “password”)
- Try stolen passwords across multiple websites
- Crack simple password combinations in seconds
This method, known as credential stuffing, is one of the fastest ways hackers get your personal data without you even realizing it.
4. Hackers Use Malware to Spy on You
Malware is malicious software that can secretly monitor your activity.
It can:
- Record everything you type (including passwords)
- Track your browsing behavior
- Steal financial information
Malware often enters your device through:
- Suspicious downloads
- Email attachments
- Unsafe websites
The Cyber-security and Infrastructure Security Agency provides guidance on how malware spreads and how to avoid it.
5. Hackers Intercept Data on Unsecured Networks
Public WiFi networks — like those in coffee shops or airports — can be risky if not properly secured.
Hackers can:
- Intercept data being transmitted
- Access login credentials
- Monitor browsing activity
This type of attack is often invisible, making it one of the more dangerous ways hackers get your personal data.

Why This Matters (And Where Most People Get It Wrong)
Most people assume identity theft only happens to others — but hackers typically target easy opportunities, not specific individuals.
If your data is:
- Exposed in a breach
- Protected by weak passwords
- Entered into a fake website
…you can become a target instantly.
👉 Many of these attacks happen without any obvious warning.
This is exactly why many people turn to identity protection tools — not just for recovery, but for early detection and prevention before serious damage happens.
External Resources to Learn More
- Federal Trade Commission – Identity theft prevention and reporting
- Cyber-security and Infrastructure Security Agency – Tips on protecting personal data
- Identity Theft Resource Center – Free assistance for identity theft victims
By understanding how hackers get your personal data, you put yourself one step ahead. The next step is learning how to detect threats early and protect your information before hackers can use it against you.
The Most Common Ways Hackers Get Your Personal Data
To fully understand how hackers get your personal data, you need to look at the most common methods they use every day. These are not rare, complex attacks — they are proven tactics that work at scale, targeting millions of people at once.
Below are the most common ways hackers get your personal data — and why they are so effective.
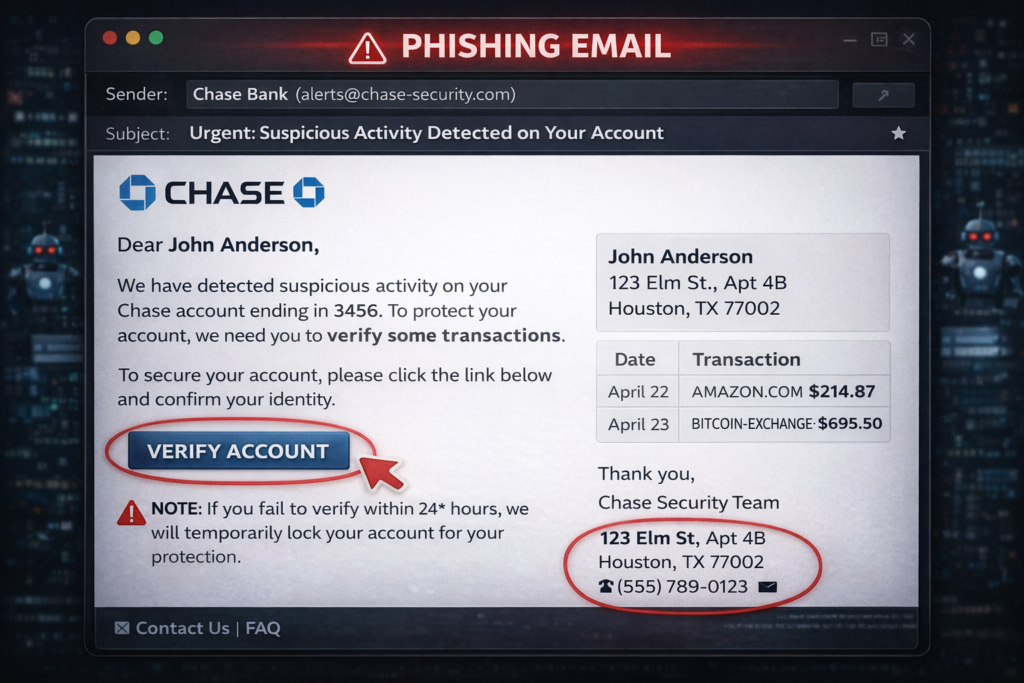
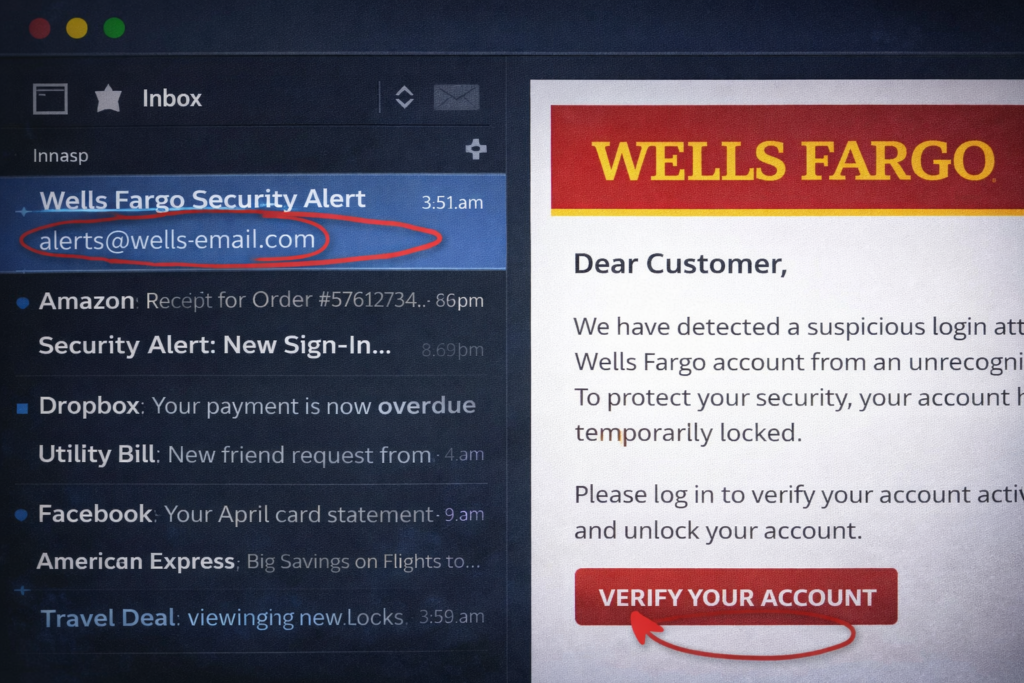
Phishing Emails and Fake Messages
Phishing remains one of the top ways hackers get your personal data because it’s simple and highly effective.
Hackers send messages that appear to come from:
- Banks
- Credit card companies
- Delivery services
- Government agencies
These messages often create urgency, such as:
- “Your account has been locked”
- “Suspicious activity detected”
- “Confirm your identity now”
Once you click the link and enter your information, hackers instantly capture your login credentials.
The Federal Trade Commission reports that phishing is one of the most reported fraud methods in the U.S.
Data Breaches and Leaked Databases
Large-scale data breaches are one of the biggest sources of stolen personal data.
When companies are hacked, sensitive information like:
- Emails
- Passwords
- Social Security numbers
- Financial data
can be exposed and sold online.
Hackers often don’t need to target you directly — they simply purchase your data from breach marketplaces.
You can monitor exposure using tools like Have I Been Pwned.
Credential Stuffing Attacks
Credential stuffing is one of the fastest-growing methods hackers use.
Here’s how it works:
- Hackers take stolen usernames and passwords from breaches
- They automatically test them across multiple websites
- If you reuse passwords, they gain access quickly
This is a major reason how hackers get your personal data without directly hacking you.

Malicious Apps and Downloads
Downloading the wrong app or file can give hackers direct access to your device.
These can include:
- Fake mobile apps
- Free software bundles
- Email attachments
Once installed, these programs can:
- Steal stored passwords
- Track your activity
- Access sensitive files
The Cyber-security and Infrastructure Security Agency warns users about risks from unverified downloads.
Social Engineering Tactics
Social engineering involves manipulating people into giving up information.
Examples include:
- Phone calls pretending to be tech support
- Messages from fake coworkers or friends
- Requests for verification codes
Hackers rely on trust and urgency, not just technology.
Skimming Devices and Physical Theft
Not all methods are digital. Hackers also use physical tools to steal data.
These include:
- Card skimmers on ATMs or gas pumps
- Stolen mail containing sensitive documents
- Lost or stolen devices without protection
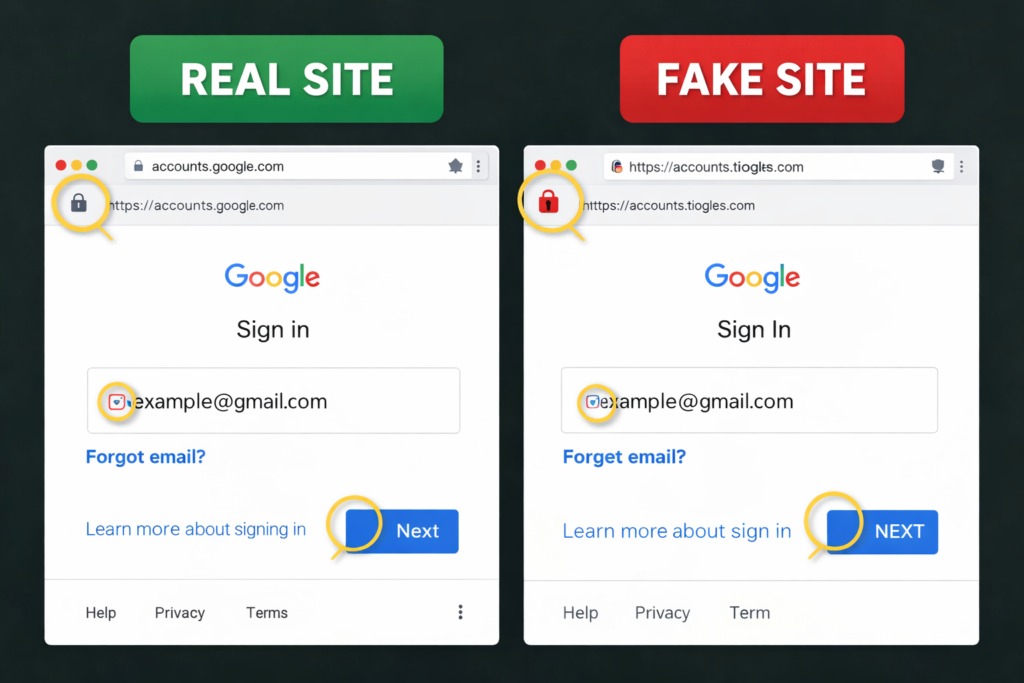
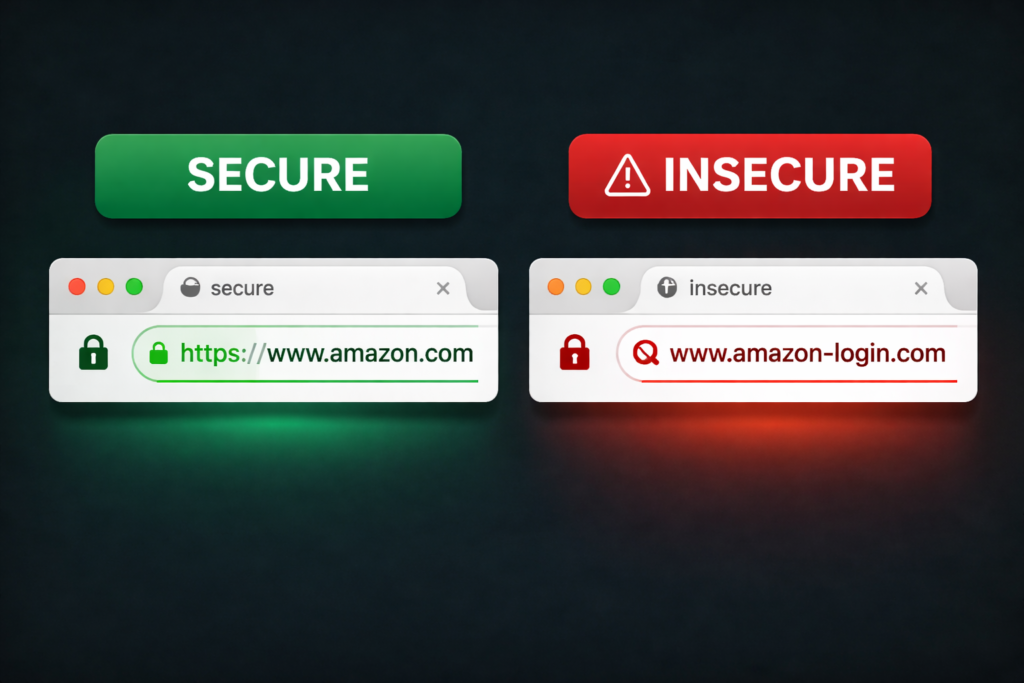
Unsecured Websites and Fake Platforms
Entering your information on unsecured or fake websites can instantly expose your data.
Warning signs include:
- No HTTPS (no padlock icon)
- Poor design or misspelled URLs
- Requests for unnecessary personal details
This is another common example of how hackers get your personal data through simple mistakes.
Why These Methods Work So Well
The most common ways hackers get your personal data all share one thing in common:
They exploit convenience and human behavior
People:
- Reuse passwords
- Click links quickly
- Trust familiar-looking messages
- Skip security checks
Hackers take advantage of this — and automate the process.
Why This Is More Dangerous Than You Think
Many people assume identity theft happens instantly — but it usually builds over time.
Hackers collect your information piece by piece, often without triggering immediate alerts.
By the time fraud is detected, your accounts, credit, or identity may already be compromised.
👉 This is why early detection matters more than most people realize.
Where Identity Protection Comes In
👉 Identity protection tools can help monitor your data and detect suspicious activity early.
See how identity theft protection works here.
Because these threats are so widespread, many people use identity theft protection services to:
- Monitor for data breaches
- Detect suspicious activity early
- Alert you before serious damage occurs
Instead of reacting after the fact, these tools help you stay one step ahead of how hackers get your personal data.
External Resources to Learn More
- Federal Trade Commission
- Cyber-security and Infrastructure Security Agency
- National Institute of Standards and Technology
By understanding the most common ways hackers get your personal data, you can start making smarter decisions online — and take steps to protect yourself before becoming a target.
How Hackers Use Stolen Personal Data Against You
Understanding how hackers get your personal data is only half the picture. What matters just as much is what they do with it after they have it.
Once your information is exposed, hackers don’t just sit on it — they monetize it quickly, often in multiple ways at the same time. In many cases, victims don’t realize anything is wrong until serious financial or legal damage has already been done.
👉 Many of these attacks happen without any obvious warning.
Here’s exactly how hackers use stolen personal data against you.
Opening Credit Accounts in Your Name
One of the most damaging outcomes of stolen data is identity theft through new credit accounts.
Hackers can use your:
- Social Security number
- Name and address
- Date of birth
to apply for:
- Credit cards
- Personal loans
- Financing accounts
By the time you notice, accounts may already be maxed out — leaving you with the consequences.
The Federal Trade Commission provides official guidance on how to report fraudulent accounts.
Draining Bank Accounts and Financial Theft
If hackers gain access to your banking credentials, they can:
- Transfer funds
- Make unauthorized purchases
- Link your account to external payment systems
These transactions often happen quickly, sometimes within hours of gaining access.
Selling Your Data on the Dark Web
A major part of how hackers use stolen personal data involves selling it to other criminals.
Your information can be packaged and sold as:
- “Fullz” (complete identity profiles)
- Credit card data bundles
- Login credentials
Organizations like the Identity Theft Resource Center explain how stolen data circulates through cyber-crime networks.

Taking Over Your Online Accounts
Hackers frequently use stolen login details to take control of your accounts.
This includes:
- Email accounts
- Social media profiles
- Shopping accounts
Once inside, they can:
- Change passwords
- Lock you out
- Use your identity to scam others
Committing Tax and Government Fraud
Another serious use of stolen data is filing fraudulent tax returns or claiming government benefits.
Hackers may:
- File a tax return before you do
- Claim refunds using your identity
- Apply for benefits under your name
The Internal Revenue Service warns that tax identity theft continues to be a major issue each year.
Targeting You With More Sophisticated Attacks
Once hackers have your data, they often use it to launch secondary attacks.
For example:
- Personalized phishing emails using your real information
- Phone scams referencing your recent activity
- Targeted fraud attempts against your family
This makes future attacks more convincing and harder to detect.
Why This Becomes So Dangerous
The biggest risk isn’t just one incident — it’s how quickly things escalate.
Hackers can:
- Combine multiple pieces of your data
- Share it across networks
- Use it repeatedly over time
That’s why understanding how hackers get your personal data is critical — because once they have it, the damage can spread far beyond a single account.
Where Identity Protection Makes a Difference
Because these threats often happen behind the scenes, many people don’t realize they’ve been targeted until it’s too late.
Identity theft protection services help by:
- Monitoring for suspicious activity
- Alerting you to new accounts or breaches
- Providing recovery support if something goes wrong
Instead of reacting after the damage is done, these tools help you detect and stop threats early.
External Resources to Learn More
- Federal Trade Commission
- Internal Revenue Service
- Identity Theft Resource Center
Understanding how hackers use stolen personal data against you highlights an important truth:
The real danger isn’t just losing your data — it’s how that data can be used in ways you don’t see coming.
That’s why early detection and protection are essential before small issues turn into major financial and personal damage.
Real-World Examples of How Hackers Steal Personal Information
It’s one thing to understand how hackers get your personal data in theory — it’s another to see how it actually happens in real life. These examples show how quickly everyday situations can turn into serious security risks.
The key takeaway: most attacks don’t feel like “hacking” at all — they feel like normal, routine interactions.
Example 1: The Fake Bank Alert Email
You receive an email that looks like it’s from your bank:
“We detected suspicious activity. Please verify your account immediately.”
You click the link, enter your login details, and everything seems fine.
But in reality:
- The website was fake
- Your credentials were captured instantly
- Hackers now have full access to your account
This is one of the most common real-world examples of how hackers get your personal data through phishing.
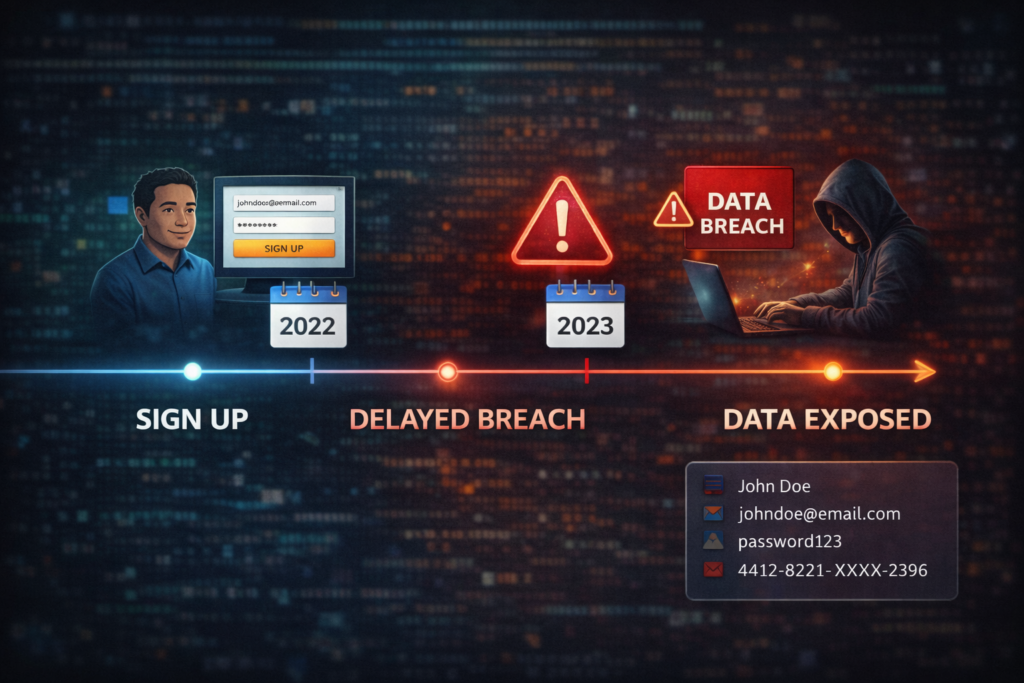
Example 2: A Data Breach You Never Knew About
You sign up for a popular app or website. Months later, that company experiences a data breach — but you never see the notification.
Your data is now exposed:
- Password
- Personal details
Hackers buy this information and begin testing it across other accounts.
According to the Identity Theft Resource Center, data breaches expose millions of records every year.
Example 3: Password Reuse Across Multiple Accounts
Let’s say you use the same password for:
- Banking
- Shopping
If just one site is compromised, hackers can:
- Access your email
- Reset other account passwords
- Take control of multiple platforms
This chain reaction is a major reason how hackers get your personal data spreads quickly across accounts.

Example 4: Downloading a “Free” App That Isn’t Safe
You download a free app or software tool that seems legitimate.
Behind the scenes, it:
- Installs spyware
- Tracks your activity
- Captures login credentials
You may not notice anything unusual — but your data is already being collected.
The Cyber-security and Infrastructure Security Agency warns users about risks from unverified apps and downloads.

Example 5: Using Public WiFi Without Protection
You connect to free WiFi at a coffee shop or airport.
While browsing or logging into accounts:
- Your data is transmitted over an unsecured network
- A hacker intercepts the connection
- Login credentials are captured
This is a silent but effective example of how hackers get your personal data without direct interaction.

Example 6: Social Engineering Phone Scam
You receive a call from someone claiming to be:
- Tech support
- Your bank
- A government agency
They ask you to:
- Confirm personal information
- Provide a verification code
- Reset your password
Because the request sounds legitimate, many people comply — giving hackers exactly what they need.

What These Examples Reveal
All of these scenarios highlight a critical truth:
How hackers get your personal data often depends on small, everyday decisions
- Clicking a link
- Reusing a password
- Downloading an app
- Connecting to WiFi
These actions seem harmless — but they create opportunities.
Why This Leads to Identity Theft
Once hackers collect enough information, they can:
- Access financial accounts
- Open credit lines
- Steal your identity
- Sell your data to others
This is where awareness turns into action.
Where Protection Tools Fit In
Because these attacks are so common — and often invisible — many people use identity theft protection services to:
- Monitor for suspicious activity
- Detect breaches early
- Alert you before accounts are compromised
Instead of guessing whether something is wrong, these tools provide real-time visibility into how hackers get your personal data and use it.
External Resources to Learn More
- Identity Theft Resource Center
- Federal Trade Commission
- Cyber-security and Infrastructure Security Agency
Real-world examples make one thing clear:
You don’t have to be targeted specifically to become a victim.
Understanding how hackers get your personal data in everyday situations is what helps you stay ahead — and take action before real damage occurs.
Warning Signs That Hackers Have Your Personal Data
Understanding how hackers get your personal data is critical — but recognizing the warning signs early can make the difference between a minor issue and a major financial disaster.
In many cases, hackers already have your information before you notice anything is wrong. The key is spotting unusual activity quickly and taking action immediately. Here are the most common warning signs someone stole your identity that you should never ignore.
Here are the most important warning signs that your personal data may be compromised.
Unfamiliar Charges or Transactions
One of the earliest signs is seeing transactions you don’t recognize.
This can include:
- Small “test” charges
- Purchases from unknown merchants
- Withdrawals you didn’t authorize
Hackers often start small to avoid detection before making larger moves.
Alerts About New Accounts or Credit Inquiries
If you receive notifications about:
- New credit cards
- Loan applications
- Hard inquiries
…it could mean someone is using your identity.
The Federal Trade Commission recommends reviewing your credit reports regularly for unfamiliar activity.

Password Reset Requests You Didn’t Initiate
Receiving unexpected password reset emails is a strong indicator that someone is trying to access your accounts.
This often means:
- Your email address is being targeted
- Hackers may already have partial access
Being Locked Out of Your Accounts
If you suddenly can’t log into your accounts, it may mean:
- Your password has been changed
- Your account recovery details were updated
This is a clear sign of account takeover.
Unrecognized Devices or Login Locations
Many platforms now notify you of new login activity.
Warning signs include:
- Logins from unfamiliar locations
- Devices you don’t recognize
- Access attempts from other countries
The Cyber-security and Infrastructure Security Agency advises monitoring login activity as part of basic cyber-security hygiene.
Missing Mail or Unexpected Bills
Physical signs can also indicate identity theft.
Watch for:
- Missing bank statements or mail
- Bills for accounts you didn’t open
- Debt collection notices
Hackers sometimes redirect mail or use your identity offline.
Increased Spam, Calls, or Suspicious Messages
If your data has been exposed, you may notice:
- More spam emails
- Scam phone calls
- Targeted phishing messages
This often happens after your information is sold or shared.
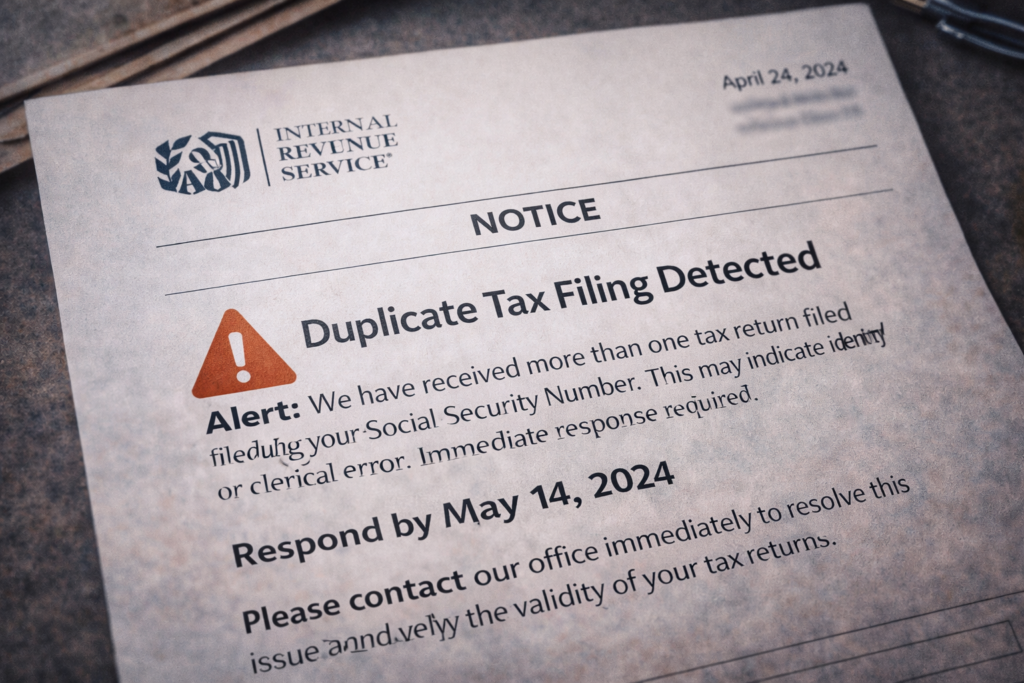
Tax Filing or Government Notice Issues
If you receive a notice that:
- A tax return has already been filed
- Benefits have been claimed in your name
…it could indicate identity theft involving government systems.
The Internal Revenue Service provides guidance on recognizing and reporting tax fraud.
Why These Warning Signs Matter
Most people don’t connect these signs immediately. But together, they often reveal a bigger issue:
Your personal data may already be in the hands of hackers
This is why understanding how hackers get your personal data is only part of the solution — early detection is just as important.
What to Do If You Notice These Signs
If you recognize any of these warning signs:
- Check your credit reports immediately
- Secure your accounts and change passwords
- Monitor financial activity closely
If you notice any of these signs, follow these steps on what to do immediately if your identity is stolen.
This is also where identity protection tools become extremely valuable.
How Identity Protection Helps Detect These Signs Early
Identity theft protection services can:
- Alert you to suspicious activity in real time
- Monitor your credit and personal data
- Detect threats before they escalate
Instead of discovering problems after the damage is done, these tools help you stay ahead of how hackers get your personal data and use it.
External Resources to Learn More
- Federal Trade Commission
- Cyber-security and Infrastructure Security Agency
- Internal Revenue Service
Recognizing the warning signs that hackers have your personal data gives you a critical advantage.
The sooner you act, the easier it is to limit damage — and protect your identity before things spiral out of control.
How to Stop Hackers From Getting Your Personal Data
Now that you understand how hackers get your personal data, the next step is stopping them before they ever get access. The good news is that most attacks can be prevented with a few smart security habits and the right tools. Using one of the best identity theft protection services can help monitor your data and detect threats early.
Hackers look for easy targets — so the goal is to make your data harder to access than the average user.
Use Strong, Unique Passwords for Every Account
One of the simplest ways to stop hackers is by strengthening your passwords.
Best practices:
- Use at least 12–16 characters
- Combine letters, numbers, and symbols
- Avoid using the same password across multiple sites
If one account gets breached and you reuse passwords, hackers can quickly access everything else.
Use a Password Manager
Remembering dozens of strong passwords is unrealistic — that’s where password managers come in.
They:
- Generate secure passwords
- Store them safely
- Autofill login details
This removes one of the biggest risks tied to how hackers get your personal data through password reuse.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of protection.
Even if hackers have your password, they still need:
- A code sent to your phone
- An authentication app
- A biometric verification
The Cyber-security and Infrastructure Security Agency strongly recommends enabling 2FA on all important accounts.

Avoid Clicking Suspicious Links and Messages
Phishing remains one of the top ways hackers steal data — but it’s also one of the easiest to avoid.
Always:
- Verify the sender
- Check URLs carefully
- Avoid clicking urgent or suspicious links
When in doubt, go directly to the official website instead of using the link.
Keep Your Devices and Software Updated
Outdated software can contain security vulnerabilities that hackers exploit.
Make sure to:
- Update your operating system
- Install security patches
- Keep apps up to date
The National Institute of Standards and Technology emphasizes regular updates as a core defense strategy.
Avoid Public WiFi or Use Secure Connections
Public networks can expose your data if not protected.
To stay safe:
- Avoid logging into sensitive accounts on public WiFi
- Use secure, trusted networks whenever possible
- Consider additional protection tools if you travel frequently
This reduces one of the easiest paths for how hackers get your personal data through network interception.
Monitor Your Credit and Financial Activity
Regular monitoring helps you detect issues early.
You should:
- Check your credit reports
- Review bank statements
- Watch for unusual activity
You can access free credit reports through Annual Credit Report.
Use Identity Theft Protection Services
One of the most effective ways to stop hackers is by using identity protection tools.
These services can:
- Monitor your personal data across the web
- Detect breaches and suspicious activity
- Alert you before hackers can act
Instead of trying to manually track everything, these tools provide continuous protection against how hackers get your personal data.
Limit the Personal Information You Share Online
The more information you share publicly, the easier it is for hackers to build a profile on you.
Reduce risk by:
- Avoiding oversharing on social media
- Limiting personal details in public profiles
- Being cautious with online forms
This makes it harder for hackers to piece together your identity.

Why Prevention Is More Important Than Recovery
Once hackers gain access to your data, the damage can escalate quickly:
- Financial loss
- Credit damage
- Time-consuming recovery process
That’s why focusing on prevention is the smartest strategy.
Understanding how hackers get your personal data allows you to stay ahead — but taking action is what truly protects you.
External Resources to Learn More
- Cyber-security and Infrastructure Security Agency
- National Institute of Standards and Technology
- Federal Trade Commission
Stopping hackers isn’t about being perfect — it’s about being prepared.
The more barriers you put in place, the less likely you are to become a target.
Why Identity Theft Protection Services Are Critical Today
Understanding how hackers get your personal data is important — but in today’s digital world, awareness alone is no longer enough. Cyber threats have become more advanced, more automated, and more widespread than ever before.
That’s exactly why identity theft protection services have gone from being “optional” to essential for many people.
Hackers Are Faster Than Ever
One of the biggest reasons identity protection is critical today is speed.
Hackers can:
- Access stolen data within minutes of a breach
- Run automated attacks across thousands of accounts
- Exploit vulnerabilities before you even know they exist
By the time you manually notice a problem, the damage may already be done.
The Federal Trade Commission reports millions of identity theft cases each year, many involving rapid account compromise.
Data Breaches Are Increasing Every Year
Even if you follow best practices, your data can still be exposed through third-party breaches.
Companies you trust — including:
- Retailers
- Financial institutions
- Online platforms
…can experience breaches that expose your personal information.
The Identity Theft Resource Center tracks thousands of breaches annually affecting millions of individuals.
Manual Monitoring Is No Longer Enough
Checking your bank account occasionally is not enough to protect against modern threats.
Hackers can:
- Open accounts without your knowledge
- Use your identity in ways that don’t show up immediately
- Operate across multiple platforms simultaneously
Identity theft protection services provide:
- Continuous monitoring
- Real-time alerts
- Broader visibility into your data
This is critical because how hackers get your personal data often happens behind the scenes.
Early Detection Prevents Major Damage
The biggest advantage of identity protection services is early detection.
These tools can alert you when:
- Your data appears in a breach
- New accounts are opened in your name
- Suspicious activity is detected
Catching these issues early can prevent:
- Financial loss
- Long-term credit damage
- Complex recovery processes

Recovery Support Saves Time and Stress
If identity theft does happen, recovery can be overwhelming.
You may need to:
- Contact banks and credit bureaus
- File reports
- Dispute fraudulent charges
- Restore your identity
Many identity protection services include:
- Dedicated recovery specialists
- Step-by-step assistance
- Insurance coverage for certain losses
The Federal Trade Commission outlines how complex recovery can be without support.
Protection Tools Address Multiple Threats at Once
One of the biggest benefits is that these services combine multiple layers of protection.
They typically monitor:
- Credit activity
- Dark web data exposure
- Financial transactions
- Personal information usage
Instead of managing everything separately, you get a centralized system protecting against how hackers get your personal data.
Why More People Are Using These Services
As cyber threats increase, more people are realizing:
It’s not about if your data is exposed — it’s about when.
Identity protection services help you:
- Stay informed
- Act quickly
- Reduce risk
They shift your approach from reactive to proactive protection.
External Resources to Learn More
- Federal Trade Commission
- Identity Theft Resource Center
- Cyber-security and Infrastructure Security Agency
The Bottom Line
Understanding how hackers get your personal data is only the first step.
The real advantage comes from detecting threats early and stopping them before they escalate.
That’s why identity theft protection services are no longer just helpful — they are a critical layer of defense in today’s digital environment.
Do You Really Need Identity Theft Protection?
After learning how hackers get your personal data, the next logical question is:
Do you actually need identity theft protection — or can you handle this on your own?
The honest answer depends on your risk level, your time, and how proactive you want to be. If you’re still unsure, read our full breakdown on whether you really need identity theft protection. But in today’s environment, most people underestimate how exposed their data really is.
The Reality: Your Data Is Already Out There
Even if you’ve never been hacked personally, your information may already exist in:
- Past data breaches
- Online accounts
- Public records
- Marketing databases
Hackers don’t need to target you directly — they often collect and reuse data that’s already available.
The Identity Theft Resource Center reports that millions of records are exposed every year through breaches.

What Happens If You Don’t Use Protection Services?
Without identity theft protection, you are responsible for:
- Monitoring your credit manually
- Checking financial accounts regularly
- Detecting suspicious activity on your own
- Handling recovery if something goes wrong
While this is possible, it requires:
- Time
- Consistency
- Attention to detail
And even then, you may miss early warning signs.
The Biggest Risk: Delayed Detection
The main problem isn’t just how hackers get your personal data — it’s how long it takes to notice.
Without monitoring tools:
- Fraudulent accounts can go undetected
- Hackers can reuse your data multiple times
- Damage can grow before you take action
The Federal Trade Commission emphasizes early detection as a key factor in reducing damage.
What Identity Theft Protection Actually Does
Identity protection services are designed to automate what most people don’t have time to do manually.
They typically:
- Monitor your credit and personal data
- Scan for breaches and leaked information
- Alert you to suspicious activity
- Help you recover if identity theft occurs
Instead of reacting late, you get real-time visibility into how hackers get your personal data and use it.
Who Needs Identity Theft Protection the Most?
While anyone can benefit, these groups are at higher risk:
- People who shop or bank online frequently
- Families managing multiple accounts
- Individuals with credit history or active loans
- Anyone who has been part of a data breach
If your personal data exists online — which it almost certainly does — you are a potential target.
When You Might Not Need It (But Be Careful)
Some people choose not to use identity protection if they:
- Closely monitor all accounts daily
- Use strong passwords and security practices
- Have minimal online exposure
However, even with strong habits, you can’t control:
- Company data breaches
- Third-party data leaks
- Automated cyber-attacks
That’s why many people still choose protection for added peace of mind.
Cost vs Risk: What Are You Really Protecting?
Identity theft can lead to:
- Financial loss
- Credit damage
- Time-consuming recovery
- Stress and uncertainty
Compared to that, identity protection services are often relatively affordable — especially when considering the potential consequences.

The Smart Approach: Prevention + Monitoring
The most effective strategy is combining:
- Strong personal security habits
- Continuous monitoring tools
This approach reduces your risk and helps you respond quickly if something happens.
External Resources to Learn More
- Federal Trade Commission
- Identity Theft Resource Center
- Cyber-security and Infrastructure Security Agency
The Bottom Line
So, do you really need identity theft protection?
If you want to rely on manual checks and accept the risk of delayed detection — you may not need it.
But if you want faster alerts, better visibility, and added protection — it becomes a smart investment.
Understanding how hackers get your personal data shows one clear truth:
It’s easier to prevent identity theft than to fix it after it happens.
Best Tools to Protect Your Personal Data From Hackers
Once you understand how hackers get your personal data, the next step is choosing the right tools to protect yourself. The reality is simple: manual protection is no longer enough. The most effective strategy combines automation, monitoring, and layered security tools.
Below are the best types of tools to protect your personal data — along with how they help stop hackers before serious damage occurs.
Identity Theft Protection Services (All-in-One Protection)
Identity theft protection services are the most comprehensive tools available today.
They typically include:
- Credit monitoring
- Dark web monitoring
- Fraud alerts
- Identity recovery support
Popular options include:
- Aura
- LifeLock
- Identity Guard
If you’re considering Aura, read our full breakdown, ‘Is Aura Worth It?‘.
You can also compare top providers in our guide, Aura vs LifeLock.
These services are designed to detect suspicious activity early — which is critical because how hackers get your personal data often happens without immediate signs.
Password Managers (Stop Credential-Based Attacks)
Password managers help eliminate one of the biggest risks: weak or reused passwords.
They:
- Generate strong, unique passwords
- Store credentials securely
- Autofill login information
Well-known tools include:
- 1Password
- LastPass
Using a password manager makes it much harder for hackers to access multiple accounts using stolen credentials.

Antivirus and Security Software (Device-Level Protection)
Antivirus software protects your devices from:
- Malware
- Spyware
- Malicious downloads
It acts as your first line of defense against threats that try to capture your personal data directly from your device.
The Cyber-security and Infrastructure Security Agency recommends using updated security software to reduce risk.
Credit Monitoring Services (Financial Protection)
Credit monitoring tools track changes to your credit profile.
They can alert you when:
- New accounts are opened
- Credit inquiries occur
- Suspicious activity appears
This is essential because financial fraud is one of the main outcomes of how hackers get your personal data.
You can also compare paid options versus free options in our guide on whether Aura is better than free credit monitoring.
Two-Factor Authentication Apps (Account Security Boost)
Two-factor authentication (2FA) apps add an extra layer of protection.
Even if hackers get your password, they cannot access your account without:
- A one-time code
- Device verification
Common apps include:
- Google Authenticator
- Authy
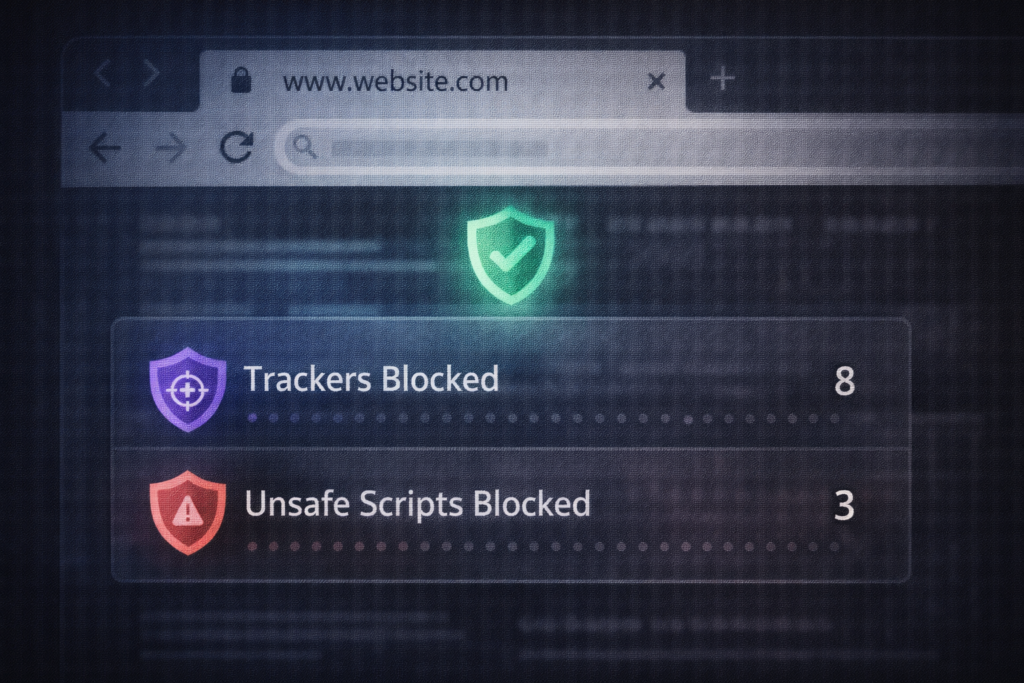
Secure Browsers and Privacy Tools
Privacy-focused browsers and extensions help protect your data while browsing online.
They can:
- Block trackers
- Prevent malicious scripts
- Warn you about unsafe websites
This reduces exposure to phishing and unsafe platforms — a key factor in how hackers get your personal data.
Why Layered Protection Works Best
No single tool can protect you completely.
The most effective strategy combines:
- Identity monitoring
- Strong password security
- Device protection
- Real-time alerts
This layered approach makes it significantly harder for hackers to:
- Access your data
- Use your information
- Go undetected
How to Choose the Right Tools
When selecting tools, look for:
- Real-time monitoring and alerts
- Ease of use
- Comprehensive coverage
- Strong reputation and support
If you want a simple solution, all-in-one identity protection services are often the best starting point.
External Resources to Learn More
- Cyber-security and Infrastructure Security Agency
- National Institute of Standards and Technology
- Federal Trade Commission
The Bottom Line
Understanding how hackers get your personal data shows why protection tools are no longer optional.
The right tools don’t just protect your data — they give you visibility, control, and peace of mind in a world where cyber threats are constantly evolving.
The goal isn’t just to react to attacks… it’s to prevent them before they happen.
Final Thoughts: Protecting Your Personal Data Before It’s Too Late
By now, you understand how hackers get your personal data, how they use it, and how quickly things can escalate once your information is exposed.
The most important takeaway is this:
Identity theft doesn’t usually happen all at once — it happens in stages.
- First, your data is exposed (often without your knowledge)
- Then, it’s tested or sold
- Finally, it’s used for fraud, account takeovers, or financial gain
By the time most people notice, the damage is already underway.
The Cost of Waiting Too Long
Many people delay taking action because:
- “It hasn’t happened to me yet”
- “I’ll deal with it if something comes up”
- “My accounts seem fine”
But the reality is, waiting can lead to:
- Financial loss
- Credit damage
- Time-consuming recovery
- Ongoing stress
The Federal Trade Commission highlights how identity theft cases often require significant time and effort to resolve.
Why Prevention Is the Smartest Move
Once hackers have your data, stopping them becomes much harder.
That’s why the focus should always be on:
- Reducing exposure
- Detecting threats early
- Acting before serious damage occurs
Understanding how hackers get your personal data gives you awareness — but prevention is what gives you control.
Small Steps Make a Big Difference
You don’t need to overhaul everything overnight. Start with simple actions:
- Strengthen your passwords
- Enable two-factor authentication
- Monitor your accounts regularly
- Be cautious with links and downloads
These small steps can significantly reduce your risk.

When to Take Protection Seriously
If any of the following apply to you, it’s time to take protection seriously:
- You’ve reused passwords across accounts
- You shop or bank online frequently
- You’ve received suspicious emails or alerts
- Your data may have been exposed in a breach
In these cases, relying on manual monitoring alone may not be enough.
The Advantage of Being Proactive
People who stay ahead of threats don’t rely on luck — they rely on systems.
Using the right tools and habits allows you to:
- Detect issues early
- Respond quickly
- Reduce long-term damage
This is especially important because how hackers get your personal data is constantly evolving.
External Resources to Stay Informed
- Federal Trade Commission
- Cyber-security and Infrastructure Security Agency
- Identity Theft Resource Center
The Bottom Line
Protecting your personal data isn’t about fear — it’s about preparation.
Because hackers often target unsecured connections and weak passwords, using tools like NordVPN to encrypt your internet activity and NordPass to manage secure passwords can significantly reduce your risk of identity theft.
Hackers don’t wait.
Threats don’t slow down.
And data exposure often happens without warning.
Understanding how hackers get your personal data puts you ahead of most people — but taking action is what truly protects you.
The earlier you start, the easier it is to stay in control.
Because when it comes to your identity…
it’s always better to be early than too late.
How to Protect Yourself Next
Understanding how hackers get your personal data is the first step.
The next step is making sure you’re protected before your information is used against you.


Pingback: Best Antivirus for Families (2026 Guide) - Riich Niich
Pingback: NordVPN vs Surfshark: Which VPN Is Better in 2026? - Riich Niich
Pingback: Public WiFi Dangers (And How To Stay Safe) - Riich Niich
Pingback: Is Incogni Worth It in 2026? (Full Review + Results) - Riich Niich
Pingback: How to Remove Your Personal Information from the Internet (2026 Guide) - Riich Niich
Pingback: How to Stay Safe on Social Media in 2026 (Avoid These Costly Mistakes) - Riich Niich
Pingback: Is Online Banking Safe in 2026? (Risks + How to Protect Your Money) - Riich Niich
Pingback: Cybersecurity Tips Everyone Should Know (2026 Guide) - Riich Niich
Pingback: Best VPN for Privacy (Stay Anonymous & Protect Your Data Online) - Riich Niich
Pingback: Is NordVPN Worth It? Full Review, Pros, Cons & Who Should Use It - Riich Niich
Pingback: Is Surfshark Worth It? Full Review, Pros, Cons & Real Value - Riich Niich
Pingback: Incogni vs DeleteMe: Which Data Removal Service Is Better? - Riich Niich
Pingback: Why Insider Threats Are More Dangerous Than Hackers (Real Risks Explained) - Riich Niich
Pingback: What Is a Data Broker? - Riich Niich
Pingback: How to Check If Your Information Is on the Dark Web - Riich Niich