Why insider threats are more dangerous than hackers is a question more people need to be asking. While most focus on external cyberattacks, the real risk often comes from within—where trusted access, limited visibility, and delayed detection create the perfect conditions for serious damage. In this guide, you’ll learn how insider threats compare to hackers, why they pose a greater risk to your personal data, and what you can do to protect yourself before it’s too late.
Table of Contents
Why Insider Threats Are More Dangerous Than Hackers
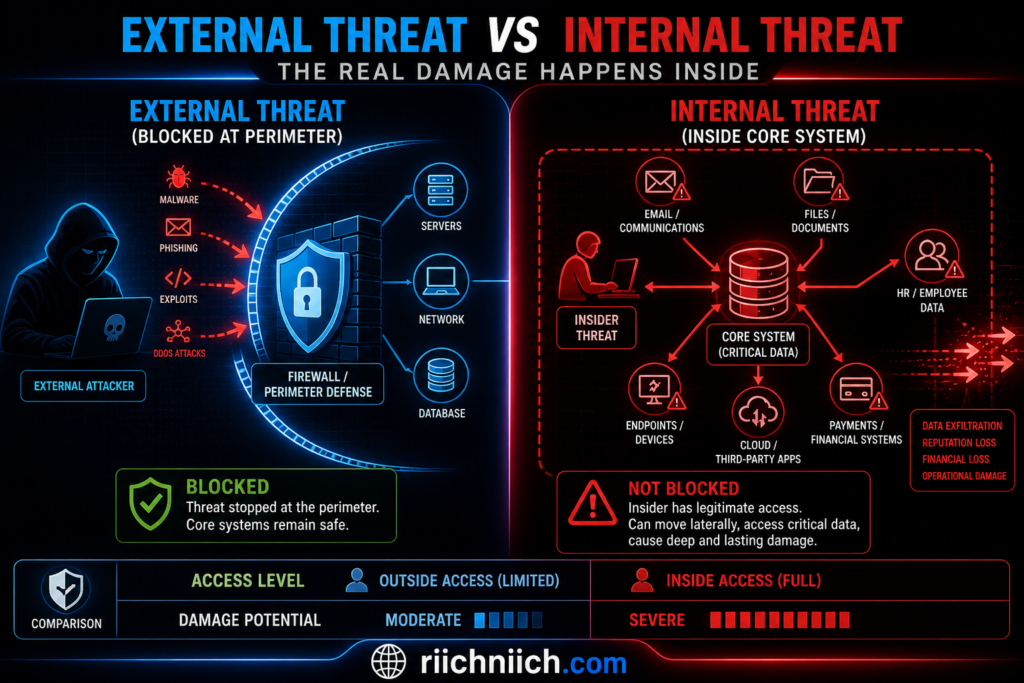
When people think about cybersecurity, they usually picture hackers breaking into systems from the outside. But the reality is often more concerning. Why insider threats are more dangerous than hackers comes down to one critical factor: they’re already inside.
Unlike external cyber threats that must bypass layers of security, insider threats operate with trusted access, making them harder to detect, faster to execute, and often more damaging. Understanding this difference is key if you want to protect your personal data, finances, and identity.
They Already Have Authorized Access
The biggest advantage insiders have over hackers is legitimate access.
Employees, contractors, or partners often:
- Access sensitive databases
- Handle customer information
- Use internal systems daily
Hackers, on the other hand, must:
- Find vulnerabilities
- Break through firewalls
- Avoid detection systems
This means insider threats can skip the hardest part of a cyberattack entirely.
According to research from IBM, breaches involving insiders often take longer to detect and can result in higher overall costs due to the level of access involved.

They Bypass Traditional Security Measures
Most cybersecurity systems are designed to stop external attacks, not internal misuse.
Tools like:
- Firewalls
- Intrusion detection systems
- VPN protections
are highly effective against hackers—but much less effective against insiders.
Why? Because insider activity often looks completely normal.
For example:
- Logging into a company system
- Downloading files
- Accessing customer records
These actions don’t trigger alarms when performed by authorized users—even if the intent is malicious.
This is a major reason why insider threats vs hackers is not an equal comparison. Insiders don’t break the rules—they abuse them.
Insider Attacks Are Much Harder to Detect
One of the most dangerous aspects of insider threats is stealth.
Hackers often leave traces:
- Suspicious login attempts
- Malware signatures
- Unusual traffic patterns
Insiders, however:
- Use real credentials
- Follow normal workflows
- Blend into everyday operations
This makes insider threats:
- Slower to identify
- Harder to investigate
- More costly over time
By the time an insider attack is discovered, the damage is often already done.
The Financial and Personal Damage Is Often Greater
Because insiders can access high-value data directly, the impact is usually more severe.
This includes:
- Social Security numbers
- Financial account details
- Login credentials
- Medical records
Once exposed, this data can be:
- Sold on the dark web
- Used for identity theft
- Exploited for financial fraud
A report from Ponemon Institute highlights that insider-related incidents can lead to significant financial losses due to prolonged exposure and delayed response.
This is where the risk becomes personal. Many identity theft cases don’t start with hackers—they start with data leaks from inside organizations.
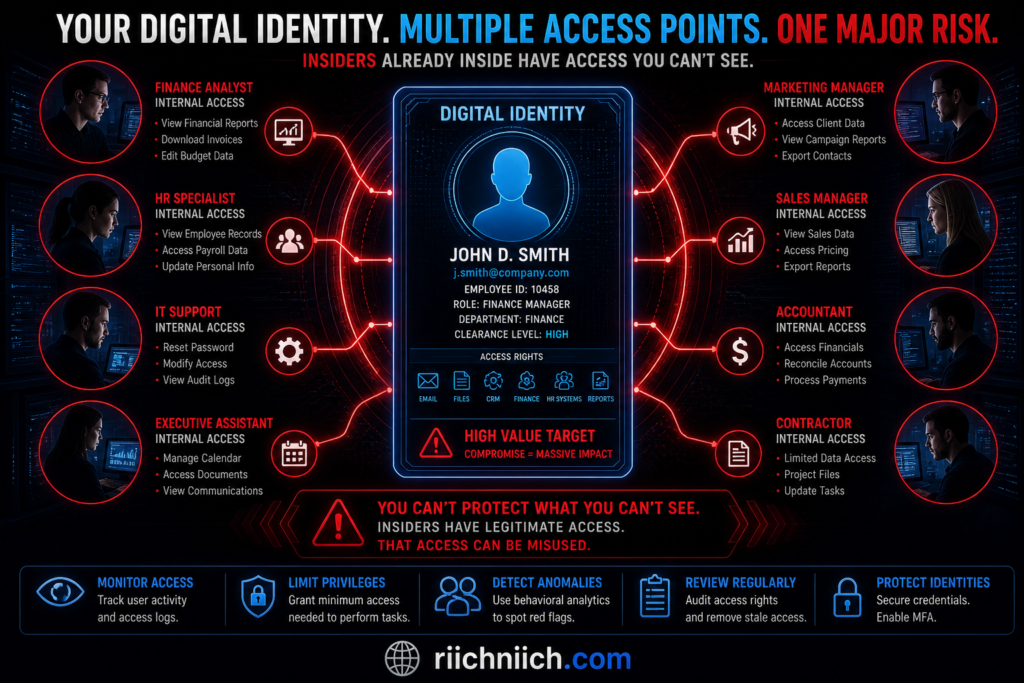
Trust Is What Makes Insider Threats So Dangerous
Organizations are built on trust. Employees are given access because they need it to do their jobs.
But that same trust creates risk.
Insider threats can come from:
- Disgruntled employees
- Negligent staff members
- Compromised user accounts
Even a simple mistake—like sending sensitive data to the wrong email—can lead to massive exposure.
This is why internal vs external cyber threats should not be viewed equally. Internal risks are often less visible but far more dangerous.
Why This Matters for You
You might be thinking: “This sounds like a company problem—how does it affect me?”
Here’s the reality:
Your personal data is stored by:
- Banks
- Healthcare providers
- Employers
- Online platforms
If an insider mishandles or steals that data, you become the victim.
That’s why understanding why insider threats are more dangerous than hackers isn’t just informational—it’s actionable.
To reduce your risk:
- Monitor your personal data exposure
- Use identity protection tools
- Remove your data from broker sites
- Secure your accounts with strong passwords
Bottom Line
Insider threats are more dangerous than hackers because they:
- Already have access
- Avoid detection systems
- Cause deeper and faster damage
- Exploit trust instead of breaking defenses
Hackers attack from the outside.
Insiders operate from within.
And in cybersecurity, the most dangerous threats are often the ones you don’t see coming.
What Is an Insider Threat? (Simple Explanation)
To understand why insider threats are more dangerous than hackers, you first need a clear definition of what an insider threat actually is.
An insider threat is a security risk that comes from someone inside an organization—someone who already has authorized access to systems, networks, or sensitive data.
This could include:
- Employees
- Contractors
- Business partners
- Vendors with system access
Unlike external hackers, these individuals don’t need to break in. They already have the credentials, permissions, and trust required to access valuable information.
Simple Definition (Quick Answer)
An insider threat is when a trusted individual misuses their access—intentionally or accidentally—causing data breaches, security incidents, or exposure of sensitive information.
This is a key reason insider threats vs hackers is not an equal comparison. Hackers must force entry, while insiders operate from a position of trust.
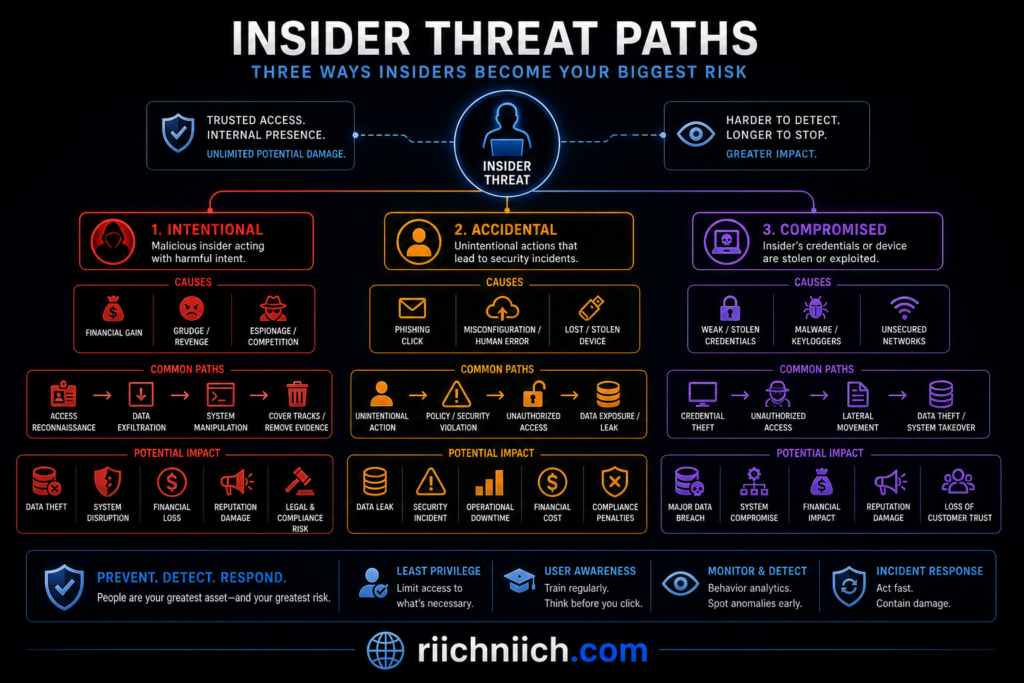
Types of Insider Threats You Should Know
Not all insider threats are malicious. In fact, many are caused by simple mistakes. Understanding the different types helps explain why insider threats are more dangerous than hackers.
1. Malicious Insider
This is the most obvious type.
- Intentionally steals or leaks data
- May be motivated by money, revenge, or competition
- Often targets sensitive customer or financial information
Example: An employee downloading customer data and selling it.
2. Negligent Insider
This is one of the most common—and underestimated—risks.
- Accidentally exposes data
- Falls for phishing scams
- Uses weak passwords or unsafe devices
According to the Cybersecurity and Infrastructure Security Agency, human error is a major factor in many security incidents.
Example: Sending confidential information to the wrong email address.
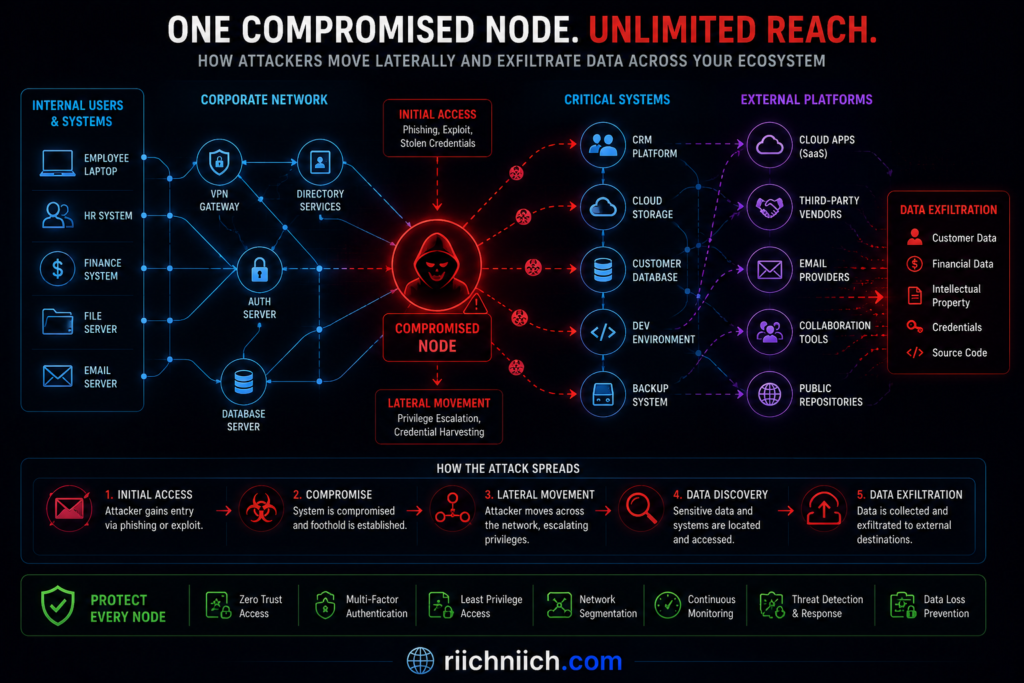
3. Compromised Insider
This happens when a hacker gains access to a legitimate user’s account.
- Stolen login credentials
- Malware or phishing attacks
- Unauthorized access disguised as normal activity
This creates a dangerous overlap between internal vs external cyber threats, making detection even harder.
Example: A hacker logging in as an employee and quietly extracting data.
Why Insider Threats Are So Risky
Now that you understand what an insider threat is, it becomes clearer why insider threats are more dangerous than hackers.
Insiders can:
- Access sensitive systems instantly
- Avoid many security controls
- Blend in with normal user activity
Reports from National Institute of Standards and Technology emphasize that insider risks are among the most challenging cybersecurity issues due to their complexity and lack of visibility.
This makes insider threats:
- Harder to detect
- Slower to respond to
- More damaging over time
How Insider Threats Impact You Personally
Even though insider threats happen inside organizations, the impact reaches far beyond them.
If a company you trust experiences an insider-related breach, your data could be exposed, including:
- Email addresses
- Passwords
- Financial information
- Social Security numbers
This is how insider incidents often lead to:
- Identity theft
- Fraudulent transactions
- Long-term privacy risks
Understanding this connection is critical if you’re serious about protecting yourself online.
Why You Should Care
Most people focus only on hackers—but that’s only part of the picture.
If you ignore insider risks, you’re missing one of the biggest threats to your personal data.
That’s why learning what is an insider threat is not just informational—it’s the first step toward:
- Protecting your identity
- Reducing your exposure online
- Choosing the right security tools
Bottom Line
An insider threat is any risk that comes from someone with authorized access to sensitive systems or data.
They don’t need to hack their way in.
They’re already inside.
And that’s exactly why insider threats are more dangerous than hackers—they operate where defenses are weakest: trust.
Insider Threats vs Hackers: Key Differences You Need to Know
To fully understand why insider threats are more dangerous than hackers, you need to look at how they actually operate. While both can cause serious damage, the way they access systems, avoid detection, and impact victims is very different.
This comparison breaks down insider threats vs hackers so you can clearly see where the real risk lies—and how to protect yourself.
Access: Inside vs Outside
The biggest difference between insider threats and hackers is access.
- Insider threats already have authorized access to systems, databases, and sensitive information.
- Hackers must find vulnerabilities, steal credentials, or exploit weaknesses to break in.
This means insider threats can act immediately, while hackers often spend time trying to gain entry.
According to research from IBM, attacks involving insiders can escalate faster because there are fewer barriers to entry.
Detection: Hidden vs Noticeable
Detection is where insider threats become especially dangerous.
- Hackers often trigger alerts through unusual behavior:
- Suspicious logins
- Malware activity
- Abnormal traffic
- Insider threats:
- Use real credentials
- Follow normal workflows
- Appear as legitimate users
This makes insider activity much harder to detect. It blends into everyday operations, which is a key reason why insider threats are more dangerous than hackers.
Speed of Impact: Immediate vs Gradual
Because insiders don’t need to break in, they can cause damage much faster.
- Insider threats:
- Instant access to sensitive data
- Ability to download or leak information quickly
- No delay from bypassing security
- Hackers:
- Often move slowly to avoid detection
- May take time to escalate privileges
- Gradually extract data
This difference in speed can lead to larger, more immediate data exposure when an insider is involved.
Level of Damage: Deep vs Surface-Level
Both insider threats and hackers can cause serious harm, but insiders often reach deeper layers of data.
- Insiders can access:
- Customer databases
- Financial records
- Internal systems
- Hackers may initially only access:
- Entry-level systems
- Limited datasets
- Partial information
This deeper access is another major reason internal vs external cyber threats should not be treated equally.
Intent: Malicious vs Mixed Risk
Hackers are almost always malicious. Insider threats, however, are more complex.
- Hackers:
- Intentional attacks
- Financial or strategic motives
- Insider threats:
- Malicious (data theft, sabotage)
- Negligent (mistakes, poor security habits)
- Compromised (accounts taken over by hackers)
This mix makes insider threats less predictable and harder to manage.
Why This Difference Matters for You
You might not work inside a company’s systems—but your data does.
Your personal information is stored by:
- Banks
- Employers
- Healthcare providers
- Online services
If an insider mishandles or leaks that data, you could face:
- Identity theft
- Financial fraud
- Long-term privacy exposure
That’s why understanding insider threats vs hackers is not just technical—it directly affects your personal security.
What You Should Do Next
Now that you understand the difference, the next step is action.
To protect yourself from both insider threats and hackers:
- Monitor your identity and personal data
- Reduce your exposure on data broker sites
- Secure your accounts with strong passwords
- Use encrypted connections on public networks
This is how you reduce risk from both internal and external cyber threats—not just one side of the problem.
Bottom Line
When comparing insider threats vs hackers:
- Hackers attack from the outside
- Insider threats operate from within
And because they already have access, avoid detection, and can cause faster damage, it becomes clear why insider threats are more dangerous than hackers.
If you focus only on hackers, you’re missing half the risk.
The real strategy is protecting yourself from both.
Why Insider Threats Are So Hard to Detect
One of the biggest reasons why insider threats are more dangerous than hackers is simple: they’re incredibly difficult to detect. While external attacks often leave clear warning signs, insider activity usually looks like normal behavior—until it’s too late.
Understanding why insider threats are so hard to detect helps you see the real risk and why protecting your personal data requires more than just basic security.
They Use Legitimate Credentials
Insider threats don’t need to hack into systems—they log in.
Because they use:
- Real usernames and passwords
- Authorized devices
- Approved access levels
their activity doesn’t raise immediate suspicion.
Unlike hackers who trigger alerts with failed logins or unusual access attempts, insiders operate within expected boundaries. This is a core reason insider threats vs hackers is not an even comparison.
Their Behavior Blends Into Normal Activity
Security systems are designed to detect abnormal behavior. Insider threats exploit this by staying within normal patterns.
Examples include:
- Accessing files they are permitted to view
- Downloading data during regular hours
- Using company-approved tools
From a system perspective, nothing looks wrong.
This is why insider threats are often described as “hidden in plain sight.” It also explains why insider threats are more dangerous than hackers—they don’t stand out.
This is exactly why identity theft often goes unnoticed—here’s what to do immediately if your identity is stolen.
There Are Fewer Immediate Warning Signs
Hackers often leave behind red flags:
- Malware infections
- Suspicious IP addresses
- Unusual spikes in traffic
Insider threats, however, rarely trigger these signals.
Instead, the warning signs are subtle:
- Slight increases in data access
- Gradual file transfers
- Minor policy violations
This delay in detection allows insider threats to cause greater long-term damage.
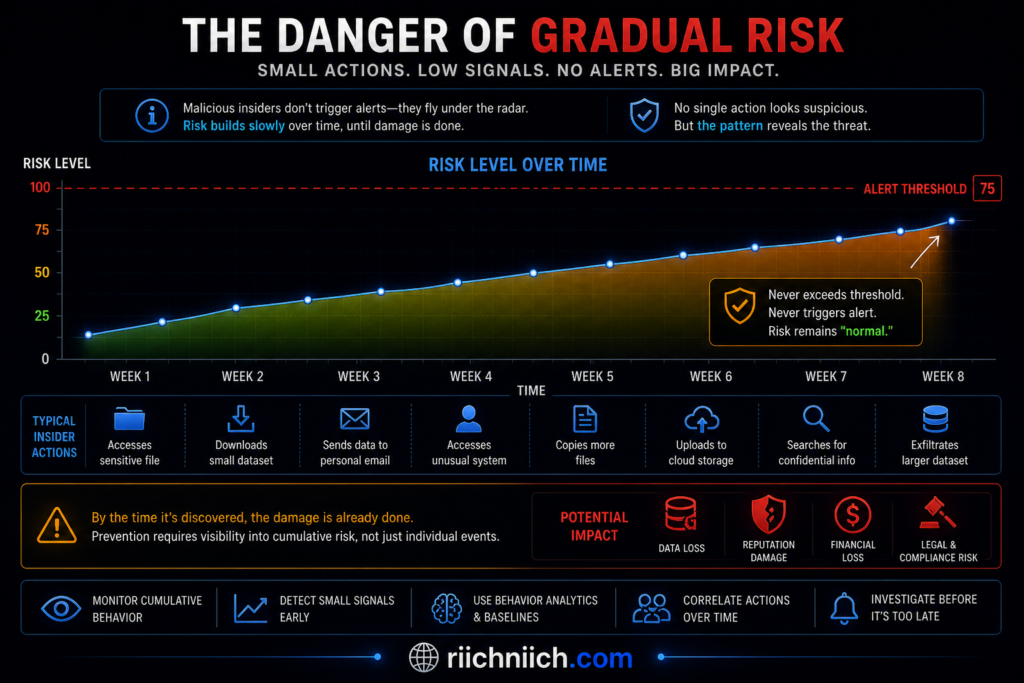
Detection Takes Longer—Much Longer
Because insider threats are harder to identify, they often remain active for extended periods.
This means:
- More data can be exposed
- More systems can be accessed
- More damage can accumulate
This extended timeline is a major reason internal vs external cyber threats should be taken seriously—especially from a personal data perspective.
Human Behavior Is Unpredictable
Another challenge is that insider threats involve people, not just systems.
Human behavior is:
- Inconsistent
- Emotional
- Difficult to model
An employee might:
- Act normally for months
- Suddenly misuse access
- Accidentally expose data without realizing it
The Cybersecurity and Infrastructure Security Agency emphasizes that both intentional and unintentional actions contribute to insider risk.
This unpredictability makes insider threats harder to detect than automated or external attacks.
Why This Matters for You
You might not control company security systems—but your data is stored inside them.
If insider threats go undetected:
- Your personal information can be exposed silently
- You may not know until fraud occurs
- Recovery can take months or even years
This is exactly why insider threats are more dangerous than hackers from a personal security standpoint.
You can’t rely on organizations alone to protect your data.
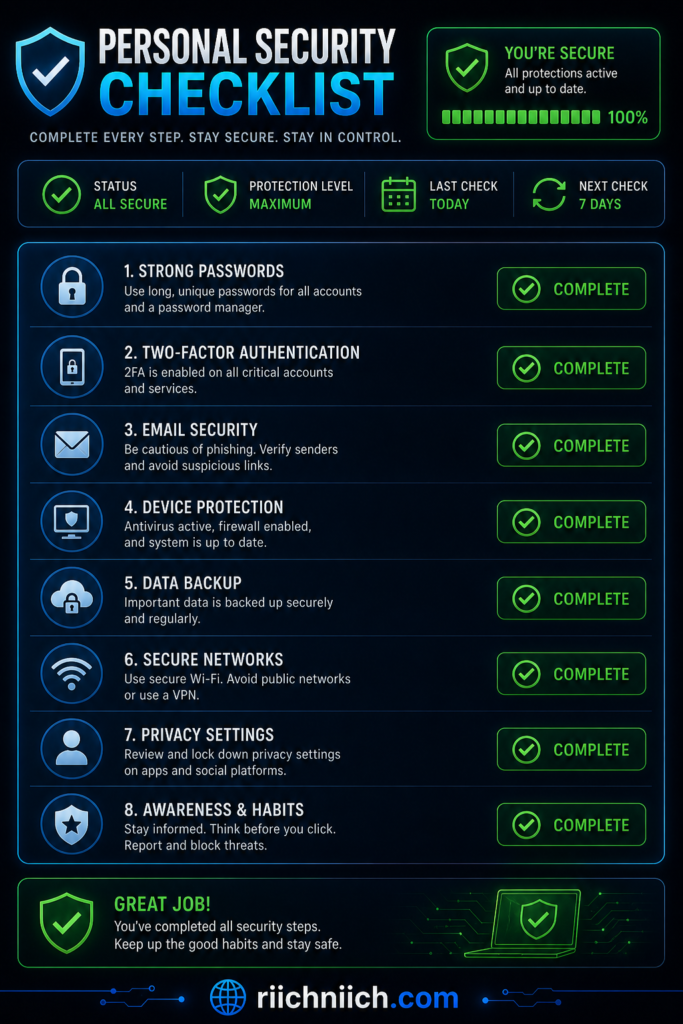
What You Can Do to Protect Yourself
Since insider threats are so hard to detect, your best strategy is proactive protection:
- Monitor your identity and financial accounts
- Reduce your exposure on data broker sites
- Use strong, unique passwords across accounts
- Enable multi-factor authentication wherever possible
These steps help limit the damage—even if an insider breach happens behind the scenes.
Bottom Line
Insider threats are hard to detect because they:
- Use legitimate access
- Blend into normal behavior
- Avoid triggering traditional security alerts
- Remain active for longer periods
This invisibility is exactly why insider threats are more dangerous than hackers.
The biggest risks aren’t always the loudest ones—they’re the ones that go unnoticed.
Real Examples of Insider Threats Causing Massive Data Breaches
To truly understand why insider threats are more dangerous than hackers, it helps to look at real-world cases with specific dates, locations, and timelines. These examples show how internal access, insider knowledge, or compromised credentials can lead to massive data breaches.
1. Tesla Insider Data Leak
- Date: Reported August 2023
- Location: United States (internal data shared externally)
- Timeline: Data accessed over time, leak reported publicly in August 2023
In 2023, reports revealed that two former employees leaked sensitive internal data, including personal employee information and internal communications.
Because the individuals had authorized access, they were able to collect and distribute data over time without immediate detection.
This is a clear example of why insider threats are more dangerous than hackers—no forced entry, no alarms triggered early, just direct misuse of access.
2. Capital One Data Breach (Insider Knowledge Exploitation)
- Date: July 2019 (breach disclosed)
- Location: United States (cloud infrastructure hosted on AWS)
- Timeline: Attack occurred March–July 2019 before discovery
In this case, a former employee of a cloud provider used insider knowledge to exploit a misconfigured firewall and access data from over 100 million customers.
Even though this was technically an external attack, the attacker’s insider-level understanding of systems made the breach possible.
This shows how internal vs external cyber threats overlap, and why insider knowledge can be just as dangerous as direct insider access.
3. Twitter Internal Access Abuse Incident
- Date: July 15, 2020
- Location: United States (remote internal systems access)
- Timeline: Attack executed within hours after employee manipulation
Attackers used social engineering to manipulate employees and gain access to internal tools. Once inside, they took control of high-profile accounts.
The critical moment happened within hours of gaining access—showing how quickly damage can occur once insider-level permissions are obtained.
According to the Cybersecurity and Infrastructure Security Agency, compromised insiders are a major category of insider threats.
This case proves that attackers don’t always hack systems—they use insiders to get in.
4. Anthem Data Breach via Compromised Credentials
- Date: Discovered January 2015
- Location: United States (health insurance database systems)
- Timeline: Attack believed to have started months before discovery
The breach exposed nearly 80 million records, including names, birthdates, and Social Security numbers.
Attackers gained access using stolen credentials, allowing them to operate inside systems undetected for an extended period.
This highlights how insider-like access—whether from an employee or compromised account—can lead to massive damage.
Reports from Verizon show credential misuse is one of the leading causes of breaches.
5. Coca-Cola Employee Data Theft Incident
- Date: Reported May 2018
- Location: United States
- Timeline: Data taken and discovered within internal review period
An employee stole sensitive data related to coworkers, including personal records and confidential HR information.
The breach did not involve advanced hacking techniques—it was a direct result of authorized access being abused.
This is one of the simplest but strongest examples of why insider threats are more dangerous than hackers.
Key Takeaways from These Insider Threat Examples
Across these cases, the timeline patterns reveal something critical:
- Insider activity can occur over days, months, or even longer
- Detection is often delayed significantly
- Damage increases the longer the threat remains unnoticed
This is the core difference in insider threats vs hackers:
- Hackers create noise
- Insider threats create silent damage over time
Why This Matters for You
Your personal data is stored in systems just like these.
If an insider—or someone with insider-level access—misuses that data:
- You may not know immediately
- Your information could already be circulating
- Fraud may occur long after the breach
Understanding why insider threats are more dangerous than hackers helps you take action before you become a victim.
What You Should Do Next
Because insider threats are hard to detect and often delayed:
- Monitor your identity and credit regularly
- Reduce your exposure on data broker sites
- Secure your online accounts with strong passwords
- Stay alert for unusual activity tied to your identity
Bottom Line
When you add dates, timelines, and real-world context, the pattern becomes clear:
Insider threats:
- Happen over time
- Avoid early detection
- Cause deeper, longer-lasting damage
That’s exactly why insider threats are more dangerous than hackers—they don’t just attack quickly, they persist quietly.
How Insider Threats Lead to Identity Theft and Financial Loss
To fully understand why insider threats are more dangerous than hackers, you need to look at the end result: identity theft and financial damage. When someone inside an organization misuses access—or when an account with insider-level permissions is compromised—your personal data can be exposed quickly and quietly.
This is where insider threats move from a “company problem” to a personal financial risk.
Step 1: Sensitive Data Is Accessed from the Inside
Organizations store large amounts of personal information, including:
- Full names and addresses
- Email accounts and passwords
- Social Security numbers
- Banking and payment details
An insider—whether malicious, negligent, or compromised—can access this data without triggering traditional security alerts.
Because they already have permission, the data extraction often looks like routine activity. This is a key reason insider threats vs hackers is not an equal comparison.
If you’re wondering how this happens in the first place, here’s a full breakdown of how hackers get your personal data.
Step 2: Data Is Exposed, Sold, or Misused
Once accessed, the data can be:
- Sold on underground marketplaces
- Shared with third parties
- Used directly for fraud
Unlike hackers who may need time to exploit stolen data, insiders can immediately access complete, high-value datasets.
Many people don’t realize their data is already exposed—here are the warning signs someone stole your identity.
This is where internal vs external cyber threats becomes critical—internal exposure tends to be more complete and more damaging.
Step 3: Identity Theft Begins
Once your personal data is exposed, identity theft can happen in several ways:
- Opening new credit accounts in your name
- Taking over existing accounts
- Filing fraudulent tax returns
- Applying for loans or benefits
Because insider breaches often include detailed personal records, attackers have everything they need to impersonate you.
The Federal Trade Commission reports that identity theft remains one of the most common consequences of data breaches.
This is a direct outcome of why insider threats are more dangerous than hackers—they provide deeper, more usable data.
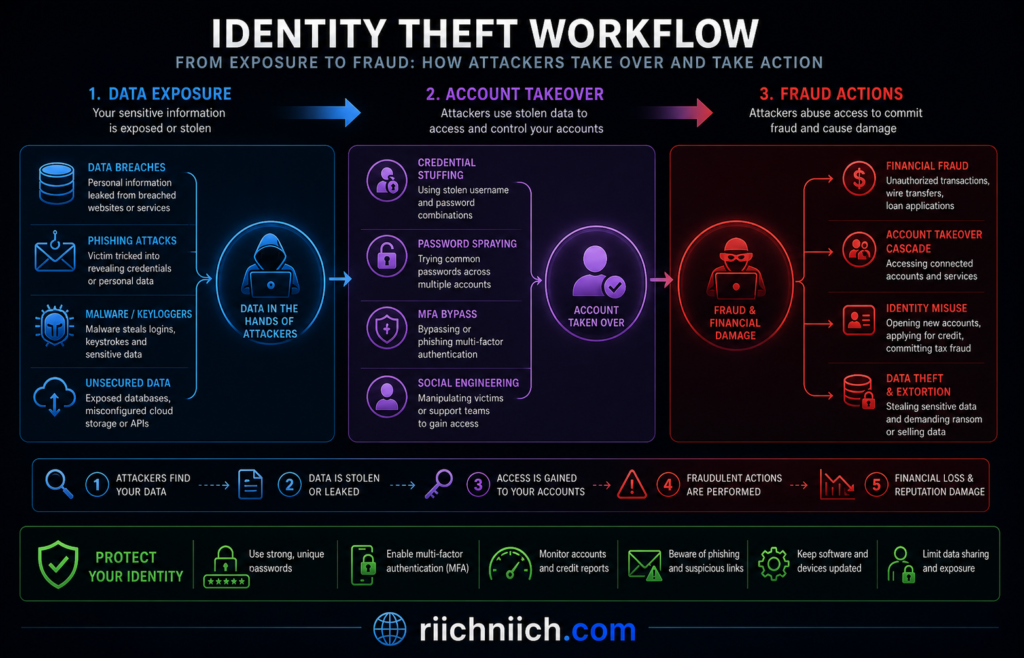
Step 4: Financial Loss Follows
Once identity theft occurs, financial damage can escalate quickly:
- Unauthorized transactions
- Drained bank accounts
- Damaged credit scores
- Long-term financial recovery
In many cases, victims don’t realize what’s happening until after the damage is done—especially when the breach originated from an insider and went undetected.
Why Insider Threats Make This Worse
Now it becomes clear why insider threats are more dangerous than hackers in terms of personal impact:
- They expose complete datasets, not partial information
- They avoid detection, allowing longer exploitation
- They enable faster identity theft due to immediate access
- They often involve trusted systems where your data is stored
In short, insider threats don’t just create risk—they accelerate the entire chain of identity theft and financial loss.
Why This Matters for You
You can’t control how companies handle insider risks—but you can control how exposed you are.
If your data is already out there:
- It can be used at any time
- You may not receive immediate alerts
- Recovery can be slow and stressful
That’s why protecting yourself is not optional—it’s necessary.
How to Protect Yourself from Identity Theft Caused by Insider Threats
To reduce your risk:
- Monitor your identity and credit activity regularly
- Remove your personal data from data broker websites
- Use strong, unique passwords for every account
- Enable multi-factor authentication
These steps help limit the damage—even if an insider breach occurs behind the scenes.
Bottom Line
Insider threats lead to identity theft and financial loss through a clear chain:
Access → Exposure → Exploitation → Financial Damage
Because insiders already have access and can avoid detection, they accelerate every stage of this process.
That’s exactly why insider threats are more dangerous than hackers—they don’t just steal data, they make it easier to turn that data into real-world harm.
The Hidden Risks Most People Ignore About Insider Attacks
Most people focus on hackers when thinking about cybersecurity. But the real danger often comes from within. Understanding the hidden risks of insider attacks is key to seeing why insider threats are more dangerous than hackers—especially when it comes to protecting your personal data and finances.
These risks are often overlooked because they don’t look like traditional cyberattacks. There’s no dramatic breach, no obvious warning—just quiet exposure that can lead to serious consequences later.
Silent Data Exposure You Never See
One of the biggest hidden risks is invisible data exposure.
When insider threats occur:
- Data can be accessed without triggering alerts
- Information can be copied without detection
- Breaches may go unreported for long periods
Unlike hackers, who often create noticeable disruptions, insiders can operate quietly in the background.
According to the National Institute of Standards and Technology, monitoring authorized users is significantly more difficult than detecting external threats.
This is a major reason why insider threats are more dangerous than hackers—they don’t create noise.
Overexposure of Your Personal Data Across Systems
Many people don’t realize how widely their data is stored.
Your personal information exists across:
- Multiple companies
- Third-party vendors
- Data brokers
- Cloud platforms
An insider in any one of these systems can expose your data.
This creates a chain reaction risk—once data leaks from one source, it can spread across multiple channels.
Delayed Impact That Hits You Later
Another hidden risk is time delay.
With insider threats:
- Data may be stolen today
- But used weeks or months later
- With no obvious connection to the original breach
This delayed impact makes it harder to:
- Identify the source
- Take immediate action
- Prevent further damage
If your data is already circulating, you may not notice until it’s too late—here’s how identity theft happens step by step.
This is why insider threats vs hackers is such an important distinction—hackers often act quickly, while insider damage can unfold slowly.
Lack of Transparency from Organizations
Not all insider incidents are disclosed immediately.
Organizations may:
- Take time to investigate
- Delay public disclosure
- Limit details about what was exposed
This means you might not even know your data has been compromised.
The Federal Trade Commission advises consumers to actively monitor their information because breaches are not always immediately visible or reported.
This lack of transparency increases your risk and reinforces why insider threats are more dangerous than hackers.
Insider Threats Can Trigger Multiple Types of Fraud
A single insider-related breach can lead to multiple forms of fraud, not just one.
Your exposed data can be used for:
- Identity theft
- Credit fraud
- Account takeovers
- Phishing and scams
Because insiders often access complete profiles, attackers have everything needed to exploit your identity in multiple ways.
This makes internal vs external cyber threats very different—internal exposure tends to be more comprehensive.
You’re Often the Last to Know
Perhaps the most overlooked risk is this:
You are usually the last person to find out.
By the time you notice:
- Fraudulent charges may already exist
- Your credit score may be affected
- Your accounts may be compromised
This delayed awareness is one of the most dangerous aspects of insider threats.
It’s also a key reason why insider threats are more dangerous than hackers from a personal perspective—they create damage before you even know there’s a problem.
Why This Matters for You
These hidden risks aren’t theoretical—they directly impact your financial and personal security.
If you rely only on companies to protect your data, you’re exposed.
The smarter approach is to:
- Assume your data could already be at risk
- Take proactive steps to monitor and protect it
- Reduce how much of your information is publicly available
What You Should Do to Reduce Your Risk
To protect yourself from insider-related risks:
- Monitor your identity and credit activity regularly
- Remove your personal data from broker and public databases
- Use strong, unique passwords across all accounts
- Enable multi-factor authentication wherever possible
These steps help you stay protected—even when insider threats occur behind the scenes.
Bottom Line
The hidden risks of insider attacks include:
- Silent data exposure
- Widespread data sharing across systems
- Delayed impact and detection
- Lack of transparency
- Multiple layers of fraud
These risks often go unnoticed—but they are exactly why insider threats are more dangerous than hackers.
The most dangerous threats aren’t always visible—they’re the ones quietly working in the background.
How to Protect Yourself from Insider Threats (Step-by-Step)
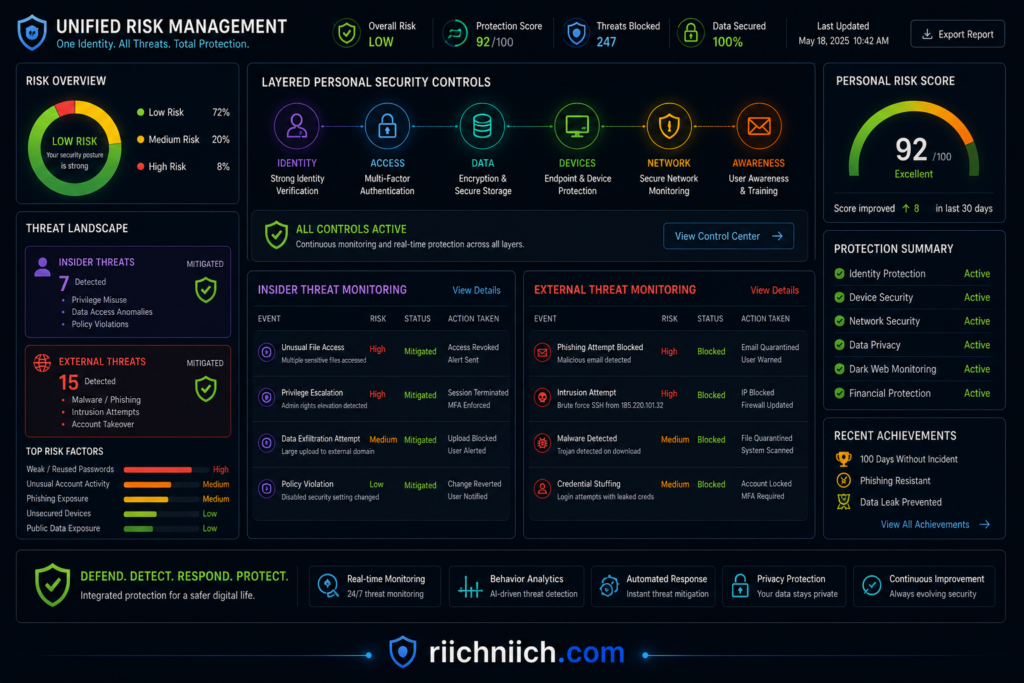
Now that you understand why insider threats are more dangerous than hackers, the next step is taking action. You can’t control what happens inside companies—but you can reduce your exposure, monitor your identity, and limit the damage if an insider-related breach occurs.
This step-by-step plan focuses on practical protection strategies that work against both insider threats and external cyber risks.
Step 1: Monitor Your Identity and Personal Data
Because insider threats are hard to detect, you need early warning signals.
Monitor:
- Credit reports
- Bank accounts
- Email breach alerts
- Dark web exposure
This helps you catch:
- Identity theft early
- Unauthorized account activity
- Suspicious financial behavior
The Federal Trade Commission recommends regularly checking your credit and financial accounts to detect fraud quickly.
Why this matters:
If insider threats expose your data, monitoring helps you respond before financial damage escalates.

Step 2: Remove Your Personal Data from the Internet
One of the biggest risks tied to insider threats is data exposure across multiple platforms.
Your information may already exist on:
- Data broker websites
- Public records databases
- Marketing and tracking platforms
Reducing your digital footprint limits what can be exploited.
According to the Electronic Frontier Foundation, minimizing publicly available personal data is a key step in protecting privacy.
What to do:
- Request data removal manually
- Use automated data removal tools
- Regularly check where your data appears
Why this matters:
Even if insider threats occur, there’s less data available to steal or misuse.
If you want to do this manually, here’s a complete guide on how to remove your personal information from the internet.
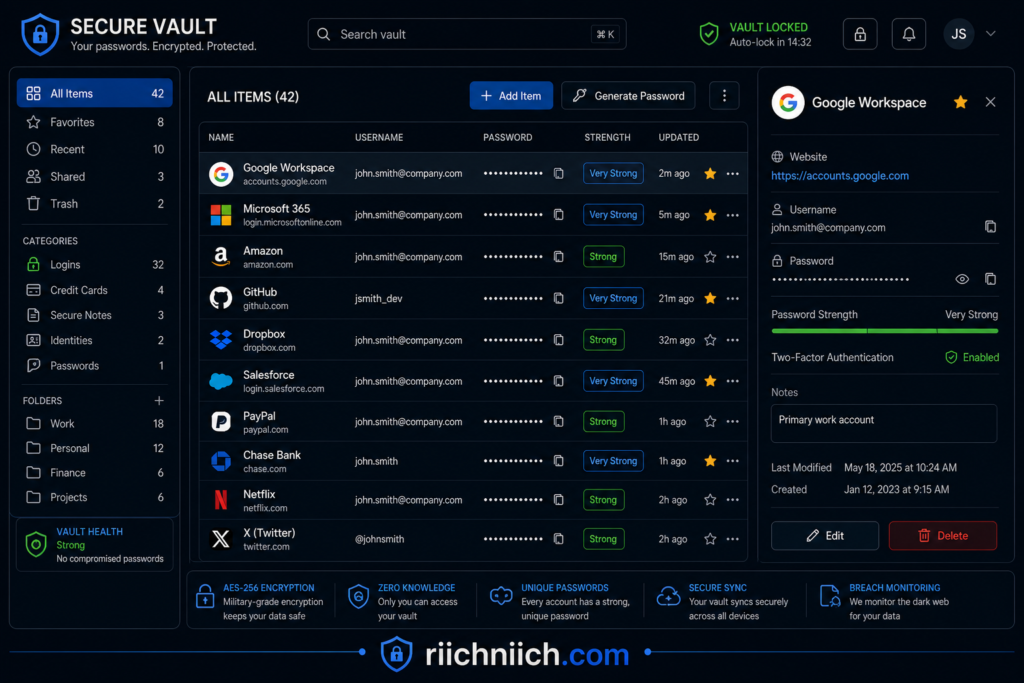
Step 3: Use Strong, Unique Passwords for Every Account
If insider threats involve compromised credentials, weak passwords make things worse.
Best practices:
- Use long, complex passwords
- Never reuse passwords across sites
- Store them securely in a password manager
The National Institute of Standards and Technology recommends using unique passwords and secure storage methods to reduce account compromise risk.
Why this matters:
If your data is exposed internally, strong passwords help prevent account takeovers and further damage.
Step 4: Enable Multi-Factor Authentication (MFA)
Multi-factor authentication adds an extra layer of protection beyond passwords.
Even if someone gains access to your login credentials, MFA can stop them from accessing your accounts.
Common MFA methods:
- SMS verification codes
- Authenticator apps
- Biometric verification
The Cybersecurity and Infrastructure Security Agency strongly recommends MFA as one of the most effective ways to prevent unauthorized access.
Why this matters:
Insider threats often involve credential misuse—MFA helps block that risk.
Step 5: Be Careful Where You Share Your Information
Many insider-related risks start with overexposure of personal data.
Limit sharing of:
- Social Security numbers
- Financial details
- Personal identifiers
- Sensitive documents
Ask yourself:
- Does this platform really need this information?
- Is this a trusted source?
Why this matters:
The less data stored in systems, the less insiders can access or misuse.
Step 6: Secure Your Devices and Connections
Even though insider threats happen inside organizations, your own devices still play a role in protecting your data.
Protect your devices by:
- Keeping software updated
- Using antivirus protection
- Avoiding unsecured public WiFi
- Encrypting sensitive data
Why this matters:
If your data is intercepted or exposed elsewhere, it can combine with insider leaks to increase risk.
Using unsecured networks can expose your data instantly—here’s why public WiFi is more dangerous than you think.
Step 7: Act Quickly If You Notice Suspicious Activity
Speed matters when dealing with identity theft or fraud.
If you notice:
- Unknown transactions
- Credit changes
- Account login alerts
Take action immediately:
- Freeze your credit
- Contact your bank
- Change your passwords
- Report fraud
The Identity Theft Resource Center provides guidance on responding quickly to identity-related incidents.
Why this matters:
Insider threats often go undetected—fast action helps limit financial loss.
Why This Step-by-Step Plan Works
This strategy protects you at every stage:
- Before exposure → reduce your data footprint
- During exposure → secure accounts and credentials
- After exposure → detect and respond quickly
This layered approach is essential because why insider threats are more dangerous than hackers comes down to one thing:
You may never see the breach happen.
Bottom Line
You can’t stop insider threats—but you can protect yourself from the damage.
By following these steps, you:
- Reduce your exposure
- Strengthen your security
- Catch problems early
That’s the smartest way to defend against both insider threats and hackers—and stay one step ahead of risks you can’t see.
Best Tools to Protect Yourself from Insider Threat Risks
If you understand why insider threats are more dangerous than hackers, then you already know this: prevention isn’t enough—you need ongoing protection.
Because insider threats happen inside organizations you don’t control, the smartest move is to protect your identity, reduce your data exposure, and secure your accounts using the right tools.
Below are the best tools to protect yourself from insider threat risks, organized by what they actually do for you.
1. Identity Theft Protection Services (Your First Line of Defense)
Identity protection tools are essential because they monitor your personal data across multiple sources.
They help detect:
- Data breaches
- Dark web exposure
- Suspicious account activity
- Credit changes
Popular options include:
- Aura Identity Theft Protection
- LifeLock by Norton
Why this matters:
If insider threats expose your data, these tools alert you before financial loss escalates.
This is your most important tool—it directly protects against identity theft caused by insider breaches.
If you’re comparing your options, here are the best identity theft protection services to consider.
2. Data Removal Services (Reduce Your Exposure)
Data removal tools help eliminate your personal information from:
- Data broker websites
- Public databases
- Marketing platforms
This reduces how much data insiders (or hackers) can access in the first place.
A top option:
Organizations like the Electronic Frontier Foundation emphasize minimizing publicly available data as a key privacy strategy.
Why this matters:
Even if insider threats occur, there’s less personal data available to exploit.
This is one of the highest ROI tools because it actively reduces your risk surface.
3. VPN Services (Protect Your Data in Transit)
A VPN (Virtual Private Network) encrypts your internet connection, especially on public WiFi.
This prevents:
- Data interception
- Credential theft
- Network-based attacks
Top options:
The Cybersecurity and Infrastructure Security Agency recommends encrypted connections when using unsecured networks.
Why this matters:
While insider threats happen internally, exposed credentials from insecure networks can combine with insider risks, making attacks easier.
Think of VPNs as preventing additional exposure that insiders could later exploit.
4. Password Managers (Prevent Account Takeovers)
Password managers help you:
- Generate strong, unique passwords
- Store credentials securely
- Avoid password reuse
Example:
Why this matters:
If insider threats expose login data, strong passwords prevent chain-reaction account breaches.
👉 This is a low-cost, high-impact tool that dramatically improves your security baseline.
5. Credit Monitoring and Alerts (Financial Protection Layer)
Credit monitoring tools track:
- New credit inquiries
- Account openings
- Changes to your credit report
These alerts help you catch:
- Fraudulent loans
- Unauthorized credit activity
- Identity theft early
The Experian and other credit bureaus provide monitoring services.
Why this matters:
Insider breaches often lead to identity theft—credit monitoring helps you respond before damage spreads.
👉 Combine this with identity protection tools for maximum coverage.
6. Antivirus and Device Security Tools
Security software protects your devices from:
- Malware
- Keyloggers
- Unauthorized access
Even though insider threats originate internally, compromised devices can:
- Leak credentials
- Enable account takeovers
- Increase overall risk
The Federal Communications Commission recommends keeping devices secure and updated.
Why this matters:
Insider threats + compromised devices = amplified risk
👉 This is your foundation layer—don’t skip it.
How These Tools Work Together (Full Protection Strategy)
No single tool is enough. The best protection comes from combining them:
- Identity Protection → detects threats
- Data Removal → reduces exposure
- VPN → protects connections
- Password Manager → secures accounts
- Credit Monitoring → prevents financial damage
- Device Security → blocks technical threats
This layered approach is critical because why insider threats are more dangerous than hackers comes down to unpredictability—you don’t control where or how the breach happens.
Why This Matters for You
You can’t stop insider threats inside companies.
But you can:
- Limit how much of your data is exposed
- Detect breaches faster
- Prevent identity theft
- Reduce financial damage
That’s the real goal.
Bottom Line
The best tools to protect yourself from insider threat risks are the ones that:
- Reduce your exposure
- Monitor your identity
- Secure your accounts
- Detect threats early
Because at the end of the day, why insider threats are more dangerous than hackers isn’t just about access—it’s about impact.
And the right tools help you stay protected before that impact reaches you.
Insider Threats vs Hackers: Which One Should You Be More Worried About?
If you’re trying to protect your identity and finances, it’s a fair question: insider threats vs hackers—who poses the bigger risk?
The honest answer: both are dangerous—but insider threats are often the risk you should worry about more.
This comes down to access, detection, and impact. And it’s exactly why insider threats are more dangerous than hackers in many real-world scenarios.
If you’re still unsure whether protection is worth it, here’s a breakdown of whether you really need identity theft protection.
Hackers: The Threat You Can See Coming
Hackers are the most talked-about cybersecurity threat—and for good reason.
They:
- Attempt to break into systems
- Use malware, phishing, and exploits
- Target individuals and organizations
The good news? Hackers are often easier to detect.
Security systems are built specifically to stop:
- Unauthorized access attempts
- Suspicious network activity
- Malware signatures
What this means for you:
Hackers are dangerous—but they often trigger warnings that allow for faster response.

Insider Threats: The Risk You Don’t See
Insider threats operate differently—and that’s what makes them more concerning.
They:
- Already have access to systems
- Use legitimate credentials
- Avoid triggering traditional alerts
Unlike hackers, insider threats don’t need to break in—they simply use what’s already available.
What this means for you:
Insider threats can expose your data without immediate warning, making them harder to respond to.
Comparing the Real Risk
When you compare insider threats vs hackers, the difference becomes clear:
- Hackers
- Must break into systems
- Often detected by security tools
- May access limited data initially
- Insider threats
- Already inside systems
- Harder to detect
- Can access complete datasets immediately
This is the core reason why insider threats are more dangerous than hackers—they start where hackers are trying to get.
Which One Causes More Damage?
Both threats can cause serious harm, but insider threats often lead to:
- Larger data exposure
- Longer undetected activity
- More detailed personal information leaks
Reports from Verizon consistently show that human elements—such as internal misuse and credential abuse—play a major role in breaches.
This leads to:
- Identity theft
- Financial fraud
- Long-term privacy risks
Bottom line:
Insider threats often cause deeper and longer-lasting damage.
The Real Answer: You Should Worry About Both—But Prioritize Insider Risk
This isn’t about ignoring hackers.
It’s about understanding where the bigger blind spot is.
- Hackers are visible threats
- Insider threats are hidden risks
And hidden risks are often the most dangerous.
This is especially important when considering internal vs external cyber threats—most people prepare for external attacks but overlook internal exposure.
Why This Matters for You
You don’t control corporate security systems.
You don’t control employee behavior.
You don’t control insider access.
But your data is stored in those systems.
That means your personal security depends on how well you protect yourself, not just how well companies protect their networks.
What You Should Do Next
To protect yourself from both insider threats and hackers:
- Monitor your identity and financial activity
- Reduce your data exposure online
- Use strong, unique passwords
- Enable multi-factor authentication
These steps ensure that even if your data is exposed—internally or externally—you stay protected.
Bottom Line
So, insider threats vs hackers—which one should you be more worried about?
- Hackers are dangerous
- Insider threats are unpredictable
And because they:
- Already have access
- Avoid detection
- Cause deeper damage
It becomes clear why insider threats are more dangerous than hackers.
If you only prepare for hackers, you’re missing the bigger risk.
The smartest strategy is protecting yourself from both—but never underestimating the threat from within.
Conclusion: Why Insider Threats Are More Dangerous Than Hackers
After comparing insider threats vs hackers, the conclusion is clear:
why insider threats are more dangerous than hackers comes down to access, visibility, and impact.
Hackers attack from the outside.
Insider threats operate from within.
And in cybersecurity, the most damaging threats are often the ones that already have trusted access.
The 3 Reasons Insider Threats Are the Bigger Risk
1. They Start With Access
Insider threats don’t need to break in—they log in.
They already have:
- System permissions
- Data access
- Trusted credentials
This eliminates the biggest barrier hackers face and allows insider attacks to begin immediately.
2. They Are Much Harder to Detect
Traditional security systems are designed to stop external attacks—not internal misuse.
Insider threats:
- Use legitimate accounts
- Follow normal workflows
- Avoid triggering alerts
According to the National Institute of Standards and Technology, monitoring authorized user behavior is one of the most complex challenges in cybersecurity.
This invisibility is a major reason why insider threats are more dangerous than hackers.
3. They Cause Deeper and Longer-Lasting Damage
Because insiders can access full datasets, the damage is often more severe.
This includes:
- Complete personal profiles
- Financial information
- Login credentials
This leads directly to:
- Identity theft
- Financial fraud
- Long-term privacy risks
The Real Risk Most People Miss
The biggest danger isn’t just the breach—it’s the delay.
With insider threats:
- Data may be exposed without your knowledge
- Fraud may happen weeks or months later
- You may not connect the damage to the original breach
This delayed impact makes insider threats especially dangerous for individuals trying to protect their identity and finances.
Why This Matters for You
You don’t control internal company security.
You don’t control employee behavior.
But your personal data is stored inside these systems.
That means your protection strategy must go beyond worrying about hackers.
To stay safe, you need to:
- Monitor your identity and financial activity
- Reduce your data exposure online
- Secure your accounts with strong credentials
- Act quickly when something looks wrong
If you want a deeper comparison of tools, here’s how Aura compares to other top identity protection services.
The Smarter Strategy: Protect Yourself Before the Damage Happens
The reality is simple:
You can’t prevent insider threats from happening inside companies.
But you can:
- Limit how much of your data is exposed
- Detect problems earlier
- Reduce the impact if a breach occurs
This is how you stay protected against both internal vs external cyber threats—not just one side of the risk.
Final Takeaway
So, why insider threats are more dangerous than hackers?
Because they:
- Already have access
- Avoid detection
- Expose more valuable data
- Cause longer-lasting damage
Hackers are the visible threat.
Insider threats are the hidden one.
And in today’s digital world, the hidden threat is often the one that causes the most harm.