How identity theft happens is something many people don’t think about until it affects them directly. In today’s digital world, personal information is stored across dozens of websites, apps, and financial platforms, making it easier than ever for criminals to collect and misuse sensitive data. Identity theft can begin with a data breach, phishing scam, stolen password, or even information shared on social media.
According to the Federal Trade Commission, millions of identity theft cases are reported every year, and many victims only discover the fraud after financial damage has already occurred. Understanding the common methods criminals use can help you recognize risks earlier and take steps to protect your personal information.

In this guide, we’ll explain how identity theft happens, the most common tactics criminals use, warning signs to watch for, and practical ways to reduce your risk of becoming a victim.
🔍 Quick Insight: How Identity Theft Happens
Identity theft doesn’t usually start with your bank account.
It often begins with small pieces of personal information — leaked data, phishing scams, or stolen credentials — that are later used to access your accounts.
👉 This is why understanding how identity theft happens is the first step to protecting yourself.
Table of Contents
How Identity Theft Happens in the Digital Age
Understanding how identity theft happens today requires looking at how much personal information exists online. In the past, identity theft often involved stolen wallets, lost documents, or physical mail theft. Today, however, most identity crimes begin digitally.
As more financial services, banking platforms, and personal accounts move online, criminals have developed sophisticated ways to collect and exploit personal data. Instead of targeting one person at a time, cyber-criminals often steal millions of records at once through large-scale cyber-attacks.
According to the Federal Trade Commission, millions of identity theft cases are reported each year in the United States. Many of these cases originate from digital sources such as hacked databases, compromised passwords, and phishing scams.

The Internet Has Expanded the Identity Theft Attack Surface
Every online account you create stores pieces of personal information. This can include:
- Full name
- Email address
- Phone number
- Date of birth
- Home address
- Banking or credit card details
When this information is stored across dozens of websites and platforms, it creates a large digital footprint. If even one of those services suffers a security breach, criminals may gain access to valuable identity data.
Once obtained, stolen information is frequently sold on hidden marketplaces across the dark web. These underground markets allow criminals to purchase full identity profiles containing everything needed to commit financial fraud.
Security researchers from the Identity Theft Resource Center report that data breaches expose billions of personal records every year, dramatically increasing the risk of identity fraud.
Why Identity Theft Is Easier Than Ever for Criminals
One reason how identity theft happens today is so different from the past is the automation of cyber-crime. Modern criminals use tools that can scan massive databases, test stolen passwords, and attempt fraudulent account logins automatically.
These automated attacks often exploit a common problem known as password reuse. When people use the same password across multiple websites, a breach at one service can allow criminals to access many other accounts.
For example, if a hacker obtains login credentials from a breached online store, they may attempt to use those same credentials on:
- banking websites
- email accounts
- investment platforms
- payment services
This tactic, known as credential stuffing, is one of the fastest ways criminals take over online identities.
The Financial Impact of Digital Identity Theft
Once criminals gain access to personal information, they may use it to commit several types of fraud, including:
- opening credit cards in someone else’s name
- applying for personal loans
- filing fraudulent tax returns
- taking over existing financial accounts
These activities can damage a victim’s credit score and create serious financial stress.
Organizations such as the Federal Bureau of Investigation warn that identity theft is now one of the fastest-growing cyber-crimes globally due to the increasing availability of stolen data.

Why Many Victims Discover Identity Theft Too Late
One of the biggest challenges with digital identity theft is delayed detection. Many victims only discover the problem after:
- receiving debt collection notices
- seeing unfamiliar accounts on their credit reports
- being denied credit unexpectedly
By the time these warning signs appear, the fraud may have already caused financial harm.
This is why many consumers now use identity monitoring services such as Aura (digital security company), LifeLock, or Identity Guard. These platforms monitor credit activity, dark web data leaks, and suspicious account changes in real time, helping detect identity theft earlier.
The Importance of Early Detection
The key to minimizing identity theft damage is early detection and rapid response. When suspicious activity is detected quickly, victims can freeze credit reports, secure financial accounts, and work with recovery specialists to resolve fraud.
Understanding how identity theft happens in the digital age helps individuals recognize risks sooner and take proactive steps to protect their personal information.
As cyber-crime continues to evolve, staying informed about identity theft methods is one of the most effective ways to reduce the chances of becoming a victim.
The Most Common Entry Point for Identity Theft
Most identity theft doesn’t happen all at once.
It starts with small pieces of information being collected over time — often through data breaches, phishing attempts, or weak passwords.
Once enough information is gathered, it can be used to access accounts or create new ones.
👉 This is why early detection is so important.
Data Breaches
Large-scale data breaches are one of the biggest contributors to identity theft. When companies store customer information in online databases, those records can become valuable targets for hackers.
If a security vulnerability is discovered, criminals may gain access to sensitive information such as:
- full names
- email addresses
- passwords
- Social Security numbers
- payment information
Once stolen, this data is often sold or traded on underground marketplaces. According to the Identity Theft Resource Center, data breaches expose millions of personal records every year, increasing the likelihood of identity fraud.
Phishing and Social Engineering
Another major example of how identity theft happens involves phishing scams. Phishing attacks attempt to trick individuals into providing sensitive information through fraudulent emails, text messages, or fake websites.
These messages often appear to come from trusted sources such as banks, shipping companies, or government agencies.
Victims may be asked to:
- verify account information
- reset passwords
- confirm payment details
Once this information is entered into a fake login page, criminals can immediately use it to access financial accounts or personal data.
The Federal Bureau of Investigation regularly warns consumers that phishing remains one of the most effective cyber-crime tactics used by identity thieves.

Credential Stuffing Attacks
Credential stuffing occurs when criminals use stolen usernames and passwords from previous data breaches to attempt logins on other websites.
Because many people reuse the same passwords across multiple platforms, a single compromised account can lead to unauthorized access across several services.
For example, a leaked password from an online shopping website might also unlock:
- email accounts
- banking apps
- digital payment services
Cyber-criminals often automate these attacks using software that can test thousands of stolen login combinations within minutes.
Mail Theft and Document Theft
Although digital threats are increasing, physical identity theft still occurs. Criminals may steal sensitive documents directly from mailboxes or trash bins.
Common targets include:
- bank statements
- credit card offers
- tax documents
- medical bills
These documents often contain enough personal information for criminals to open fraudulent accounts or impersonate victims.
The United States Postal Inspection Service advises consumers to secure their mail and shred sensitive paperwork to reduce identity theft risks.
Account Takeovers
Another way how identity theft happens is through account takeover fraud. This occurs when criminals gain access to existing online accounts and change login credentials to lock out the original user.
Once inside the account, attackers may:
- transfer funds
- make purchases
- access stored personal information
Account takeovers can happen through phishing, stolen passwords, or malware infections.
Security experts from the Cyber-security and Infrastructure Security Agency (CISA) recommend enabling two-factor authentication and monitoring financial activity regularly to reduce this risk.
Why Understanding This Matters
Identity theft often happens quietly — without obvious warning signs.
By the time you notice something is wrong, fraud may have already occurred.
This is why many people focus not just on prevention, but on early detection and fast response.
👉 Tools that monitor your identity and accounts in real time can help detect suspicious activity earlier.
Many consumers also choose to use identity protection services that monitor credit reports, personal data exposure, and suspicious financial activity. These tools can provide alerts when potential identity theft is detected, helping individuals respond quickly before serious damage occurs.
Because identity theft can happen in many ways, services like NordProtect help detect suspicious activity early and protect your personal data.
How Data Breaches Lead to Identity Theft
One of the most common explanations for how identity theft happens today involves large-scale data breaches. A data breach occurs when hackers gain unauthorized access to a company’s database containing customer information. Because many organizations store massive amounts of personal data, a single breach can expose millions of identities at once.
These incidents have become increasingly common as businesses rely on cloud systems, online accounts, and digital payment platforms. When cyber-criminals successfully infiltrate a database, they may steal sensitive personal information such as:
- full names
- Social Security numbers
- email addresses
- phone numbers
- login credentials
- credit card details
Once this data is stolen, it can be used directly for fraud or sold to other criminals who specialize in identity theft.
Stolen Data Often Appears on the Dark Web
After a breach occurs, stolen personal data is frequently sold on underground marketplaces located on the dark web. These marketplaces allow criminals to purchase identity information in bulk.
For example, a complete identity profile may include:
- name and address
- Social Security number
- birthdate
- financial account details
This type of package is often referred to as a “full identity profile”, and it can be used to open credit accounts, apply for loans, or commit tax fraud.
Research from the Identity Theft Resource Center shows that data breaches continue to expose billions of personal records every year. The more data that becomes available online, the easier it becomes for criminals to carry out identity theft schemes.

Data Breaches Provide Criminals With Everything They Need
Many people assume identity theft only happens when financial information is stolen. In reality, criminals can use smaller pieces of personal data to reconstruct an identity profile.
For example, hackers might combine:
- an email address from one breach
- a password from another breach
- a phone number from a public database
This process allows criminals to build a detailed identity profile that can be used for fraud.
👉 Many of these threats go unnoticed until it’s too late.
Why Victims Often Don’t Know Their Data Was Breached
One of the most concerning aspects of how identity theft happens through data breaches is that victims often remain unaware for months or even years. Companies may not detect the breach immediately, and even when they do, affected individuals may not realize the risks.
During this time, criminals may quietly use stolen data to:
- test fraudulent credit applications
- attempt account logins
- sell identity data to other attackers
The Federal Trade Commission advises consumers to monitor credit reports and financial accounts regularly because many identity theft cases are discovered long after the original breach occurred.
Why Identity Protection Services Are Becoming More Popular
Because data breaches are now one of the main reasons how identity theft happens, many individuals are turning to identity monitoring services for additional protection. These platforms monitor personal information across credit reports, public records, and dark web databases.
When suspicious activity is detected, users may receive alerts that allow them to act quickly before serious fraud occurs.
Services such as Aura (digital security company), LifeLock, and Identity Guard offer features like:
- dark web monitoring
- credit report alerts
- fraud resolution support
- identity theft insurance
While no service can completely eliminate the risk of identity theft, early alerts can help reduce financial damage and speed up recovery if personal information is compromised.
The Key Takeaway
Understanding how identity theft happens through data breaches highlights the importance of protecting personal information in an increasingly digital world. As more companies store sensitive data online, the number of potential breach targets continues to grow.
By staying informed, monitoring financial accounts, and considering identity protection tools, individuals can reduce the risk of becoming victims of identity fraud.
How Phishing Attacks Steal Personal Information
Another major example of how identity theft happens is through phishing attacks. Phishing is a type of cyber-crime where attackers trick people into revealing sensitive information such as passwords, banking details, or Social Security numbers. Instead of hacking systems directly, criminals manipulate victims into voluntarily providing their personal data.
Phishing attacks have become increasingly sophisticated in recent years. Cyber-criminals often design messages that appear to come from trusted organizations like banks, delivery companies, government agencies, or popular online services.
According to the Federal Bureau of Investigation, phishing is one of the most common online fraud tactics and causes billions of dollars in losses each year.

How Phishing Scams Work
To understand how identity theft happens through phishing, it helps to look at the typical steps criminals use.
Most phishing attacks follow a simple pattern:
- The victim receives a message that appears legitimate.
- The message urges the victim to take immediate action.
- The victim clicks a link that leads to a fake website.
- The victim enters personal information that is captured by the attacker.
These messages often include warnings such as:
- “Your account has been locked.”
- “Suspicious activity detected.”
- “Verify your information immediately.”
Because the message creates a sense of urgency, many people respond quickly without verifying whether the request is legitimate.
Types of Phishing Attacks
Phishing attacks can appear in several forms, each designed to capture personal data.
Common types include:
Email phishing – Fake emails that imitate banks, payment services, or online retailers.
SMS phishing (smishing) – Fraudulent text messages that include malicious links.
Voice phishing (vishing) – Phone calls where scammers impersonate government officials or financial institutions.
Spear phishing – Targeted attacks directed at specific individuals using personalized information.
Cyber-security experts from the Cyber-security and Infrastructure Security Agency warn that these attacks are becoming more convincing as criminals use stolen data to personalize messages.
Why Phishing Is So Effective
One reason how identity theft happens through phishing is so common is because the attack targets human behavior rather than technical vulnerabilities.
Many phishing emails are carefully designed to look identical to legitimate communications. They may include:
- official logos
- familiar website layouts
- realistic email addresses
- urgent security warnings
👉 Many of these threats go unnoticed until it’s too late.
Once a victim enters their login credentials on a fake website, criminals can immediately access financial accounts or gather enough information to commit identity fraud.
How Phishing Leads to Identity Theft
When attackers successfully capture personal information, they can use that data in several ways. For example, stolen credentials may allow criminals to:
- access online banking accounts
- reset account passwords
- open fraudulent credit accounts
- impersonate victims for financial transactions
In many cases, phishing attacks are only the first step. Once criminals gain access to email accounts, they may search for additional personal information such as financial statements or identification documents.
This is one reason phishing remains one of the fastest-growing forms of identity theft worldwide.
How Identity Protection Services Can Help
Because phishing attacks are so common, many consumers use identity monitoring services to detect suspicious activity quickly. These platforms monitor financial accounts, credit reports, and dark web data exposure for signs that personal information has been compromised.
While identity monitoring services can alert you to suspicious activity, tools like NordVPN help prevent your data from being exposed in the first place by encrypting your internet connection, while NordPass protects your accounts with secure password management.
Services such as Aura (digital security company), LifeLock, and Identity Guard can provide alerts if unusual activity is detected. Early alerts allow users to secure accounts and prevent further identity fraud.
Understanding how identity theft happens through phishing can help individuals recognize warning signs and avoid becoming victims of these increasingly sophisticated scams.
How Criminals Use the Dark Web for Identity Theft
Another important part of understanding how identity theft happens involves the role of the dark web. The dark web is a hidden portion of the internet that is not indexed by traditional search engines and often requires specialized software to access. While some people use it for privacy-related purposes, it has also become a major marketplace for cyber-criminal activity.
One of the most common illegal activities on the dark web is the buying and selling of stolen personal data. Criminals who obtain information through data breaches, phishing attacks, or malware frequently upload that data to dark web marketplaces where other attackers can purchase it.
What Types of Personal Information Are Sold
To understand how identity theft happens, it helps to see what types of data criminals are actually buying and selling. Dark web marketplaces often list stolen information in categories, making it easy for fraudsters to find what they need.
Common types of data sold include:
- Social Security numbers
- credit card numbers
- email login credentials
- bank account information
- passport or driver’s license data
In many cases, criminals sell a complete identity profile that contains enough information to impersonate a victim. These profiles are sometimes referred to as “full identity packages.”
Cyber-crime researchers from the Identity Theft Resource Center report that billions of personal records have been exposed in data breaches over the past decade, providing a steady supply of stolen information for these underground markets.

How Criminals Use Stolen Data
Once attackers obtain personal information from the dark web, they can use it in several ways. This is one of the main reasons how identity theft happens so frequently in the digital age.
Criminals may use stolen data to:
- open fraudulent credit card accounts
- apply for personal loans
- file fake tax returns
- access existing financial accounts
- commit medical identity fraud
Because the information was originally obtained through cyber-crime, victims often have no idea their personal data is circulating online until financial damage occurs.
Security agencies such as the Federal Bureau of Investigation warn that identity theft linked to dark web data marketplaces continues to grow as cyber-criminal networks expand.
Why Victims Rarely Know Their Information Is on the Dark Web
One reason how identity theft happens through dark web marketplaces is so dangerous is that victims usually cannot see when their personal data has been exposed. Unlike normal websites, dark web marketplaces are intentionally hidden and often operate anonymously.
Criminals may trade stolen identities for months or even years before the information is used in a fraud scheme. During this time, victims may continue using their accounts normally without realizing their identity data has already been compromised.
Government cyber-security guidance from the Cyber-security and Infrastructure Security Agency explains that stolen personal information may circulate through multiple criminal networks before being used for identity theft.
How Identity Monitoring Can Detect Dark Web Exposure
Because individuals cannot easily search the dark web themselves, many people rely on identity monitoring services to track whether their personal information appears in known breach databases or criminal marketplaces.
Services such as Aura (digital security company), LifeLock, and Identity Guard offer dark web monitoring tools that scan for exposed personal data. If sensitive information such as an email address, password, or Social Security number appears in a breach database, the user may receive an alert.
Early detection allows individuals to change passwords, secure accounts, and take steps to prevent fraud before identity theft occurs.
Why the Dark Web Plays a Major Role in Identity Theft
Understanding how identity theft happens through dark web marketplaces highlights how modern cyber-crime operates. Instead of working alone, criminals often participate in organized networks where stolen data is traded and reused across multiple fraud schemes.
As the amount of personal data stored online continues to grow, monitoring tools and proactive security measures have become increasingly important for protecting personal identities in the digital world.
How Public WiFi Can Expose Your Personal Data
Another important way how identity theft happens is through unsecured public WiFi networks. Public internet connections in places like airports, hotels, coffee shops, and shopping centers are convenient, but they can also create opportunities for cyber-criminals to intercept personal data.
When you connect to an open WiFi network, your device may be sharing information across a network that lacks strong security protections. If attackers are connected to the same network, they may be able to monitor internet traffic and capture sensitive data.
How Hackers Intercept Data on Public Networks
Many public WiFi networks do not use strong encryption. This means the information sent between your device and the internet can sometimes be intercepted.
Cyber-criminals may use specialized software to capture data traveling across the network. This technique is sometimes called a “man-in-the-middle” attack, where the attacker secretly sits between the user and the website they are visiting.
During this process, hackers may attempt to collect:
- login usernames and passwords
- email messages
- financial account details
- personal identification information
According to cyber-security guidance from the Cyber-security and Infrastructure Security Agency, unsecured public WiFi networks are one of the most common environments where attackers attempt to intercept sensitive information.

Fake WiFi Networks Used for Identity Theft
Another way how identity theft happens through public WiFi is through fake hotspots created by attackers. In this type of scam, criminals set up a wireless network that looks legitimate.
For example, a hacker might create a hotspot with a name such as:
- “Airport_Free_WiFi”
- “Hotel Guest Network”
- “CoffeeShop WiFi”
When users connect to these networks, attackers can monitor everything they do online, including login activity and financial transactions.
The Federal Trade Commission warns that fake WiFi networks are frequently used to collect personal information from unsuspecting users.
Why Public WiFi Increases Identity Theft Risk
Using unsecured WiFi networks increases the chances that personal data could be exposed. If criminals obtain login credentials or financial details, they may use that information to access accounts or commit identity fraud.
For example, attackers who capture login credentials could attempt to access:
- online banking platforms
- email accounts
- digital payment services
- shopping accounts
Once criminals gain access to these accounts, they may gather additional personal data that helps them build a complete identity profile.
Cyber-security researchers from the National Institute of Standards and Technology recommend avoiding sensitive transactions on unsecured public networks whenever possible.
How Identity Protection Tools Help Reduce Risk
Because public WiFi risks are increasing, many consumers now rely on digital security and identity monitoring services to help protect their personal information. These services can monitor suspicious account activity and alert users if unauthorized logins or financial changes occur.
Platforms such as Aura (digital security company), LifeLock, and Identity Guard often include features designed to help detect identity theft early, including fraud alerts and account monitoring.
Some readers compare the major protection platforms before choosing one, and this detailed breakdown of Aura vs LifeLock explains the differences in monitoring, alerts, and fraud recovery services.
Another common comparison is Aura vs Identity Guard, especially for users looking at AI-powered fraud detection and identity monitoring features.
While these tools cannot prevent every cyber threat, they can provide early warnings if personal data has been compromised.
Protecting Yourself When Using Public WiFi
Understanding how identity theft happens through public WiFi networks can help reduce risk when connecting to the internet in public places.
Some basic precautions include:
- avoiding financial transactions on public networks
- using secure websites that begin with “https”
- disabling automatic WiFi connections
- logging out of sensitive accounts after use
Taking these steps can reduce the chances that cyber-criminals will intercept personal information while using public internet connections.
How Social Media Oversharing Leads to Identity Theft
Social media platforms allow people to share updates, photos, and personal milestones with friends and family. However, many users don’t realize that social media can also reveal information that criminals may use to commit fraud. In fact, understanding how identity theft happens often includes recognizing how much personal information is publicly available online.
Cyber-criminals frequently analyze social media profiles to collect small pieces of personal data that can later be used to impersonate victims, reset account passwords, or answer security verification questions.

Personal Information Criminals Look For
When identity thieves examine social media accounts, they are often searching for details that help them build a complete identity profile.
Common pieces of information criminals look for include:
- full name
- date of birth
- hometown or current city
- employer information
- family member names
- photos of identification documents
Even information that appears harmless can become valuable when combined with other stolen data. For example, a birthday posted online may help criminals answer password recovery questions for financial accounts.
Cyber-security researchers from the Federal Trade Commission warn that oversharing personal information online can increase the risk of identity theft and fraud.
How Criminals Combine Social Media Data With Breach Data
One reason how identity theft happens through social media is so effective is that attackers rarely rely on a single source of information. Instead, they combine data from multiple locations.
For example, a cyber-criminal might gather:
- an email address from a data breach
- a password from another breach
- personal details from social media
By combining these pieces of information, attackers can create a detailed identity profile that can be used to access accounts or open fraudulent financial accounts.
Security experts from the Cyber-security and Infrastructure Security Agency note that publicly available information on social media often helps criminals strengthen phishing attacks and impersonation attempts.
Social Media Can Help Criminals Target Victims
Another way how identity theft happens through social media is through targeted scams. When criminals review a person’s online activity, they can craft personalized phishing messages that appear highly convincing.
For example, if a criminal sees that someone recently posted about a vacation, they might send a fake travel-related email or message pretending to come from an airline or hotel.
Similarly, if someone shares their workplace publicly, attackers may send emails that appear to come from a company’s IT department requesting login credentials.
According to cyber-security guidance from the National Institute of Standards and Technology, targeted social engineering attacks are more successful when attackers use personal information gathered from online sources.
How Identity Protection Services Can Help
Because personal information is often scattered across many online platforms, monitoring tools can help detect when that information is exposed or used in suspicious activity.
Identity protection platforms such as Aura (digital security company), LifeLock, and Identity Guard monitor financial activity, credit reports, and exposed personal data to detect possible identity theft.
If suspicious activity appears, users can receive alerts that allow them to take action quickly.

Reducing the Risk of Social Media Identity Theft
Understanding how identity theft happens through social media oversharing can help individuals protect their personal data online.
Some simple ways to reduce risk include:
- limiting the amount of personal information shared publicly
- adjusting social media privacy settings
- avoiding posts that reveal sensitive details such as birthdays or addresses
- being cautious when accepting friend requests from unknown accounts
By controlling what information is shared online, individuals can reduce the chances that criminals will use social media to gather personal data for identity theft.
What Criminals Do After Identity Theft Happens
Understanding how identity theft happens is important, but it’s equally important to know what criminals do once they obtain someone’s personal information. After identity thieves collect enough data—such as Social Security numbers, financial account details, or login credentials—they often move quickly to commit fraud before the victim notices.
In many cases, criminals attempt multiple types of fraud using the same stolen identity. Because identity information can be reused in different ways, a single data breach or phishing attack can lead to several forms of financial damage.
Opening Fraudulent Credit Accounts
One of the most common outcomes of how identity theft happens is the creation of fraudulent credit accounts. Criminals may use stolen personal information to apply for credit cards, personal loans, or retail financing in the victim’s name.
If the application is approved, the criminal can immediately begin making purchases or withdrawing funds. Meanwhile, the victim may not discover the account until the lender reports missed payments to credit bureaus.
According to the Federal Trade Commission, credit card fraud and loan fraud are among the most frequently reported types of identity theft.
Taking Over Existing Financial Accounts
Another way how identity theft happens leads to fraud is through account takeovers. In this situation, criminals gain access to an existing financial account and change the login credentials to lock out the original owner.
Once inside the account, attackers may:
- transfer funds to other accounts
- make unauthorized purchases
- access stored personal information
- attempt additional financial fraud
Because criminals often move money quickly, victims may only notice the fraud after financial damage has already occurred.
Security experts from the Federal Bureau of Investigation report that account takeover fraud has increased significantly as cyber-criminals gain access to stolen login credentials.
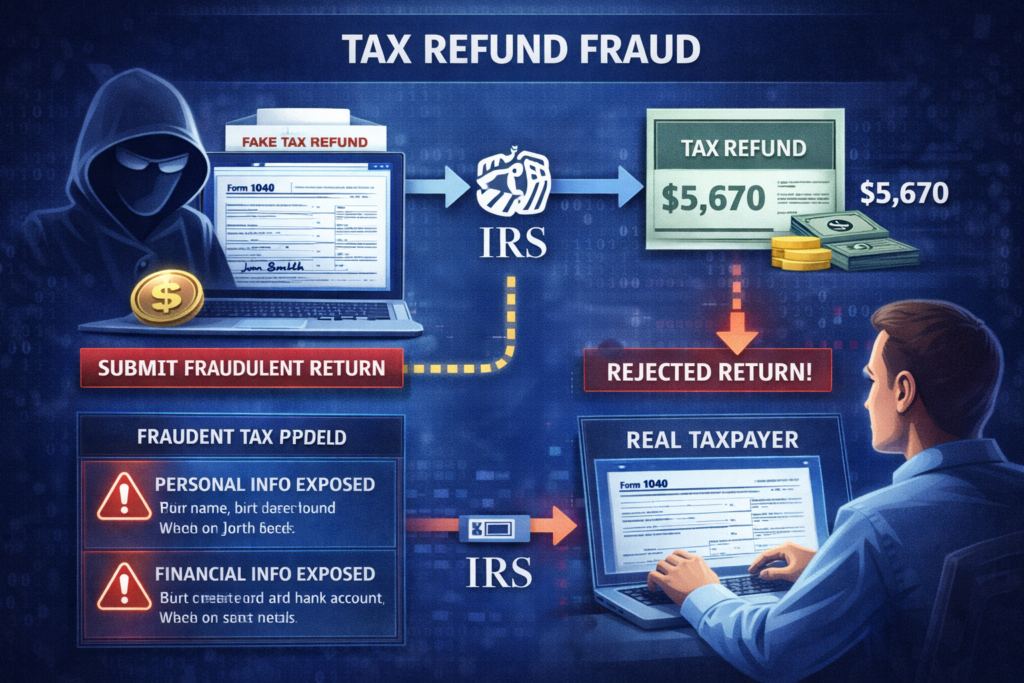
Filing Fraudulent Tax Returns
Another tactic criminals use after learning how identity theft happens involves tax fraud. If attackers obtain a Social Security number and other personal information, they may file a fake tax return using the victim’s identity.
The goal is usually to claim a tax refund before the real taxpayer submits their return. When the legitimate taxpayer later attempts to file, they may receive a notification that a return has already been processed.
The Internal Revenue Service warns that tax-related identity theft remains a serious issue, especially when stolen personal data becomes available after major data breaches.
Medical Identity Theft
Another form of fraud linked to how identity theft happens is medical identity theft. In this situation, criminals use stolen identity information to receive medical services, obtain prescriptions, or file insurance claims under another person’s name.
This type of fraud can create serious problems for victims because incorrect medical records may be added to their health history.
Healthcare fraud investigators have reported cases where stolen identities were used to obtain expensive medical treatments or equipment.
Why Early Detection Matters
Once criminals begin using stolen identity information, the financial damage can escalate quickly. Victims may face credit score damage, fraudulent debt, and time-consuming recovery processes.
This is why understanding how identity theft happens and monitoring personal data exposure is so important.
Identity protection services such as Aura (digital security company), LifeLock, and Identity Guard help detect suspicious activity by monitoring credit reports, financial transactions, and exposed personal data.
Early alerts can allow victims to freeze credit reports, secure accounts, and begin fraud recovery before the situation becomes more severe.
The Key Takeaway
Learning how identity theft happens is only part of the equation. Knowing what criminals do with stolen identities helps individuals recognize warning signs early and take action quickly.
Because identity thieves often attempt multiple types of fraud using the same stolen information, proactive monitoring and rapid response are critical steps in protecting personal financial security.
Warning Signs Your Identity May Already Be Stolen
Understanding how identity theft happens is important, but recognizing the warning signs of identity fraud can help you take action before the damage becomes more severe. In many cases, victims don’t realize their identity has been compromised until they notice unusual financial activity or receive unexpected notifications related to accounts they never opened.
Because identity theft can occur through data breaches, phishing attacks, or stolen personal information, it’s important to monitor for signs that criminals may already be using your identity.
Unexpected Charges or Bank Activity
One of the first warning signs that how identity theft happens has already affected you is unusual activity on your bank or credit card accounts.
Victims may notice:
- purchases they did not make
- withdrawals from unfamiliar locations
- small “test” charges used by criminals before larger transactions
These test transactions are often used by fraudsters to determine whether a stolen card or financial account is still active before attempting larger purchases.
The Federal Trade Commission recommends reviewing financial statements regularly to detect unauthorized transactions as early as possible.

New Credit Accounts You Didn’t Open
Another major warning sign related to how identity theft happens is the appearance of new credit accounts or loans that you never applied for.
Criminals often use stolen identity information to apply for:
- credit cards
- personal loans
- retail financing accounts
- mobile phone contracts
These accounts may only appear when lenders begin reporting activity to credit bureaus. Victims sometimes discover these fraudulent accounts after being denied credit unexpectedly.
According to the Consumer Financial Protection Bureau, reviewing credit reports regularly is one of the best ways to detect fraudulent accounts early.
Debt Collection Notices for Unknown Accounts
In some cases, victims first realize how identity theft happens after receiving calls or letters from debt collectors regarding accounts they never opened.
If criminals successfully open credit accounts using stolen identities, they may accumulate unpaid balances that eventually get sent to collection agencies.
Common signs include:
- collection letters for unfamiliar accounts
- phone calls about unpaid debt you don’t recognize
- credit score drops caused by unknown delinquent accounts
These situations often require formal identity theft reports to resolve.
Missing Mail or Unexpected Mail
Physical mail can also reveal signs that identity theft has occurred. For example, victims may notice:
- missing bank statements
- missing credit card offers
- unfamiliar financial mail arriving at their address
In some cases, criminals intercept mail to obtain financial information or prevent victims from seeing account notifications.
The United States Postal Inspection Service warns that mail theft continues to be a common method used in identity fraud schemes.
Alerts From Identity Monitoring Services
One of the fastest ways to detect identity theft today is through monitoring services that track suspicious activity related to your personal data. These services monitor things like credit reports, public records, and dark web databases.
If personal information appears in suspicious activity reports, users may receive alerts warning them of potential identity fraud.
Platforms such as Aura (digital security company), LifeLock, and Identity Guard provide monitoring tools that help detect identity theft earlier.
Early detection allows victims to freeze credit reports, secure financial accounts, and begin fraud recovery quickly.
Why Recognizing the Signs Early Matters
Because how identity theft happens often involves stolen data circulating online for months or years before being used, early detection can significantly reduce financial damage.
If you notice any of these warning signs, it’s important to take immediate action by reviewing your credit reports, contacting financial institutions, and reporting identity theft to the appropriate authorities.
Recognizing these signals early can help limit fraud, protect your credit history, and prevent criminals from continuing to misuse your identity.
How Identity Theft Protection Services Help Prevent Fraud
Understanding how identity theft happens helps people recognize the risks of data breaches, phishing scams, and stolen personal information. However, awareness alone does not always stop identity fraud. Because personal data can circulate online without your knowledge, many individuals use identity theft protection services to help monitor and detect suspicious activity.
Identity protection platforms are designed to identify early warning signs of identity fraud so users can respond quickly before criminals cause serious financial damage.

Continuous Monitoring of Personal Information
One of the most valuable features of identity protection services is continuous monitoring. These platforms track multiple data sources where identity theft activity may occur.
Monitoring often includes:
- credit report changes
- public record activity
- dark web marketplaces
- financial account alerts
Because how identity theft happens frequently involves stolen data circulating across different systems, monitoring tools help detect suspicious activity across several areas at once.
According to the Federal Trade Commission, early detection plays a critical role in limiting financial damage caused by identity fraud.
Real-Time Fraud Alerts
Another key way identity protection services help prevent fraud is through real-time alerts. If suspicious activity is detected—such as a new credit inquiry or unusual financial transaction—the system can immediately notify the user.
These alerts allow individuals to quickly investigate potential fraud and take protective actions such as:
- freezing credit reports
- contacting financial institutions
- changing compromised passwords
Quick response times are important because criminals often attempt to complete fraudulent transactions shortly after obtaining stolen data.
Dark Web Monitoring
A major reason how identity theft happens today involves personal data appearing on the dark web after data breaches. Identity protection services often scan dark web databases to determine whether sensitive information such as email addresses, passwords, or Social Security numbers have been exposed.
If exposed data is discovered, users may receive alerts that recommend immediate actions, such as changing passwords or securing accounts.
Security guidance from the Cyber-security and Infrastructure Security Agency encourages individuals to monitor exposed credentials and update passwords if their information appears in breach databases.
Identity Recovery Assistance
If identity theft does occur, recovery services can help victims restore their accounts and financial records. Many identity protection platforms provide dedicated fraud specialists who assist users with the recovery process.
Recovery support may include:
- contacting lenders to close fraudulent accounts
- helping file identity theft reports
- assisting with credit bureau disputes
- guiding victims through fraud resolution steps
These services can significantly reduce the time and stress involved in resolving identity theft cases.
Identity Theft Insurance
Some identity protection plans also include insurance coverage designed to help cover expenses related to identity theft recovery. These expenses may include legal fees, lost wages during recovery, and certain financial losses caused by fraud.
While insurance cannot prevent identity theft, it can help reduce the financial impact if a fraud incident occurs.
Consumer protection resources from the Consumer Financial Protection Bureau recommend reviewing protection services carefully to understand the coverage and monitoring features offered.

Popular Identity Protection Services
Several well-known companies provide identity monitoring and fraud protection tools. Platforms such as Aura (digital security company), LifeLock, and Identity Guard offer a range of security features including monitoring alerts, fraud recovery assistance, and identity theft insurance.
Many consumers also compare premium protection platforms with basic monitoring tools. This guide explains Is Aura Better Than Free Credit Monitoring? and what additional security features full identity protection services provide.
For readers who want to compare leading options, you can review a detailed breakdown of the Best Identity Theft Protection Services to determine which features best match your security needs.
The Bottom Line
Learning how identity theft happens is an important step toward protecting your personal information. However, because identity theft methods continue evolving, many consumers use identity protection services to add an additional layer of monitoring and security.
By detecting suspicious activity early and providing recovery support, these services can help reduce the financial and emotional impact of identity theft while helping users stay ahead of emerging cyber threats.
How to Reduce Your Risk of Identity Theft
Learning how identity theft happens is the first step toward protecting your personal information. Once you understand the methods criminals use—such as data breaches, phishing scams, and stolen personal data—you can take proactive steps to reduce your risk.
Although no security strategy can eliminate identity theft completely, following a few important practices can significantly lower the chances that criminals will gain access to your personal information.
Use Strong and Unique Passwords
Weak or reused passwords are one of the most common reasons how identity theft happens through compromised accounts. If one website suffers a data breach and you use the same password elsewhere, attackers may be able to access multiple accounts.
To improve account security:
- create long passwords with a mix of letters, numbers, and symbols
- avoid using the same password on multiple websites
- consider using a password manager to securely store login credentials
Cyber-security guidance from the National Institute of Standards and Technology recommends using unique passwords and password managers to reduce account compromise risks.
Enable Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security to online accounts. In addition to entering a password, users must verify their identity through another method such as a temporary code sent to their phone.
Even if criminals obtain your password, they may still be unable to access your account without the additional verification step.
Because how identity theft happens often begins with stolen login credentials, enabling two-factor authentication can significantly reduce the chances of unauthorized access.
Monitor Financial Accounts and Credit Reports
Regularly reviewing financial statements and credit reports can help detect identity theft early. Victims who discover fraudulent activity quickly often experience less financial damage.
Some important monitoring steps include:
- checking bank and credit card transactions frequently
- reviewing credit reports for unfamiliar accounts
- watching for unexpected credit inquiries
Consumers can access free credit reports through the AnnualCreditReport.com website, which allows individuals to review their credit information from major credit bureaus.

Freeze Your Credit If Necessary
A credit freeze prevents lenders from accessing your credit report when reviewing new credit applications. Because most lenders require access to credit reports before approving loans or credit cards, a freeze can help stop criminals from opening new accounts.
Understanding how identity theft happens helps many consumers realize that freezing their credit can be an effective defense after a data breach or suspicious activity.
Guidance from the Consumer Financial Protection Bureau explains that credit freezes are free and can be lifted temporarily when legitimate credit applications are needed.
Be Careful With Emails, Links, and Messages
Phishing scams remain one of the most common ways how identity theft happens. Criminals often send messages that appear to come from trusted organizations in order to trick users into revealing personal information.
To reduce this risk:
- avoid clicking suspicious links in emails or text messages
- verify website addresses before entering login information
- contact companies directly if you receive unexpected account alerts
Developing these habits can help prevent attackers from collecting sensitive information through phishing attempts.
Consider Identity Theft Protection Services
Because personal data can be exposed in ways that individuals cannot easily monitor, many people use identity monitoring services for additional protection. These services track credit activity, data breaches, and suspicious financial behavior.
Platforms such as Aura (digital security company), LifeLock, and Identity Guard offer monitoring tools that can alert users when unusual activity occurs.
One of the most popular platforms in this space is Aura. If you’re considering it, this detailed review explains Is Aura Worth It? and what protection features it offers.
The Key Takeaway
Knowing how identity theft happens helps individuals take practical steps to protect their personal information. While cyber-criminals continue developing new tactics, combining strong passwords, account monitoring, cautious online behavior, and identity protection tools can significantly reduce the risk of identity fraud.
By staying proactive and informed, individuals can better safeguard their financial accounts and personal data from modern identity theft threats.
Final Thoughts: Understanding How Identity Theft Happens and How to Stay Protected
Understanding how identity theft happens is one of the most important steps in protecting your personal and financial information. As digital services continue to expand, criminals have more opportunities to collect and misuse personal data through tactics such as data breaches, phishing scams, public WiFi attacks, and stolen login credentials.
Because personal information is often stored across many online platforms, identity theft can occur without victims realizing their data has been compromised. In many cases, fraud only becomes visible after financial damage has already occurred.
This is why awareness and proactive security measures are essential in today’s digital environment.

Identity Theft Prevention Requires Multiple Layers of Security
Learning how identity theft happens reveals that criminals rarely rely on a single tactic. Instead, they often combine several methods to gather personal information and commit fraud.
For this reason, effective identity protection usually involves multiple layers of defense, including:
- secure password practices
- careful monitoring of financial accounts
- protection against phishing scams
- awareness of data breaches
- identity monitoring tools
Security experts from the Cyber-security and Infrastructure Security Agency recommend using layered security strategies to reduce exposure to cyber threats and identity fraud.
Why Monitoring Your Personal Data Matters
Even if you follow good cyber-security habits, your personal information may still be exposed through data breaches at companies you interact with. Because these incidents are outside your control, monitoring tools can help detect suspicious activity sooner.
Organizations like the Identity Theft Resource Center report that data breaches continue to expose millions of records each year, increasing the chances that personal data may appear in criminal marketplaces.
Monitoring services can help identify warning signs such as new credit inquiries, unusual financial activity, or exposed personal information.
Choosing Identity Protection Tools
For individuals concerned about how identity theft happens and how to stay protected, identity protection services can provide additional monitoring and recovery support.
Services such as Aura (digital security company), LifeLock, and Identity Guard offer tools designed to detect suspicious activity and help users respond quickly if identity theft occurs.
These platforms often include features such as:
- credit monitoring alerts
- dark web data scans
- fraud recovery assistance
- identity theft insurance
While no service can eliminate identity theft entirely, early detection can significantly reduce the financial and emotional impact of identity fraud.

Staying Informed Is One of the Best Defenses
As cyber-crime continues evolving, staying informed about how identity theft happens helps individuals recognize risks and respond quickly to potential threats.
By combining strong cyber-security habits, careful monitoring of personal information, and reliable identity protection tools, individuals can reduce their exposure to identity theft and protect their financial well-being in an increasingly connected world.
If you’re still unsure whether monitoring services are necessary, this guide explains Do You Really Need Identity Theft Protection? and when these services are most useful.



Pingback: 13 Warning Signs Someone Stole Your Identity (And What To Do Immediately) - Riich Niich
Pingback: How Hackers Get Your Personal Data (And How to Stop Them) - Riich Niich
Pingback: What To Do Immediately If Your Identity Is Stolen (Step-by-Step Guide) - Riich Niich
Pingback: Credit Freeze vs Credit Lock — What’s Safer? - Riich Niich
Pingback: Best Password Managers (2026 Guide): Protect Your Accounts From Hackers - Riich Niich
Pingback: NordProtect Review (Is It Worth It in 2026?) - Riich Niich
Pingback: How to Remove Your Personal Information from the Internet (2026 Guide) - Riich Niich
Pingback: Cybersecurity Tips Everyone Should Know (2026 Guide) - Riich Niich
Pingback: NordVPN vs Surfshark: Which VPN Is Better in 2026? - Riich Niich
Pingback: How to Protect Yourself from Identity Theft (Step-by-Step Guide) - Riich Niich
Pingback: Best Data Removal Services - Riich Niich